Manual Chapter :
Hardware HSM Setup and Administration
Applies To:
Show Versions
BIG-IP AFM
- 21.1.0
BIG-IP APM
- 21.1.0 , 21.0.0, 17.5.1, 17.5.0, 17.1.3, 17.1.2, 17.1.1, 17.1.0
BIG-IP LTM
- 21.1.0 , 21.0.0, 17.5.1, 17.5.0, 17.1.3, 17.1.2, 17.1.1, 17.1.0
BIG-IP DNS
- 21.1.0 , 21.0.0, 17.5.1, 17.5.0, 17.1.3, 17.1.2, 17.1.1, 17.1.0
BIG-IP ASM
- 21.1.0 , 21.0.0, 17.5.1, 17.5.0, 17.1.3, 17.1.2, 17.1.1, 17.1.0
Hardware HSM Setup and Administration
Setup of embedded FIPS platforms in a device group
You can configure a device group using two BIG-IP platforms from the same series with a FIPS hardware security module (HSM) installed in each unit. When setting up an embedded FIPS solution on a device group, you install the two systems and can connect to a serial console to remotely manage the systems. In the event that network access is impaired or not yet configured, the serial console might be the only way to access your system.
After you have set up and configured the systems, you can create the FIPS security domain by initializing the HSM and creating a Security Officer (SO) password. You must configure the same security domain name on all HSMs in the group.
Embedded HSM initialization and synchronization
overview
After you have set up and configured your F5 FIPS platform,
you create a FIPS security domain by initializing the embedded hardware security module (HSM) and then
synchronizing all applicable HSMs.
HSM management on BIG-IP platforms
On BIG-IP platforms with an embedded hardware security module
(HSM), you perform all HSM management tasks, such as HSM initialization and
synchronization, from the TMOS Shell (
tmsh
).Initialize the HSM in 5000/7000/10200 platforms
You must initialize the hardware security module (HSM) installed in each unit before you can use it. This is typically a one-time operation. When you are creating a device group using more than one FIPS platform, you initialize the HSM on one unit, and then initialize the HSM on a peer unit using the same security domain label that you used on the first unit.
You can initialize the HSM and create the security domain before you license the system and create a traffic management configuration.
- Log in to the command line of the system using an account with root access.
- Open the TMOS Shell (tmsh).tmsh
- Initialize the HSM and set a security officer (SO) password.run util fips-util -f initRunning this command deletes all keys in the HSM and makes any previously exported keys unusable.The initialization process takes a few minutes to complete.The initialization process begins. When prompted, type the Security Officer (SO) password.F5 recommends that you choose a strong value for the SO password. You cannot use the keyworddefaultas the SO password.WARNING: This erases all keys from the FIPS 140 device. Any configuration objects dependent on FIPS keys will cause the configuration fail to load. ==================== WARNING ================================ The FIPS device will be reset to factory default state. All keys and user identities currently stored in the device will be erased. Any configuration objects dependent on FIPS keys will cause the configuration fail to load. Press <ENTER> to continue or Ctrl-C to cancel Resetting the device ... The FIPS device is now in factory default state. Enter new Security Officer password (min. 7, max. 14 characters): Re-enter Security Officer password:
- When this message displays, type a security domain label.NOTE: security domain label must be identical on peer FIPS devices in order to be able to synchronize with them. Enter security domain label (max. 50 chars, default: F5FIPS):Be sure to keep the security domain label and password in a secure location. You need the domain label and password when you initialize the HSM on a peer unit. You can use the same password or choose a new one. This information is also required when replacing a unit (for RMA or other reasons). Since keys are synchronized from the working unit to a new unit, the domain label and password are required.Initializing new security domain (F5FIPS)... Creating crypto user and crypto officer identities Waiting for the device to re-initialize ... Creating key encryption key (KEK) The FIPS device has been initialized.
- Enable the HSM device using one of these options:
- Reboot the unit.
- Restart all services:restart sys service all.Restarting services disrupts load-balanced traffic and might terminate remote login sessions to the system.
After you complete the initialization process on the first unit, you can initialize a peer system and add it to the security domain of the first unit. You must use the same security domain label that you used on the first unit.
Initialize the HSM in 10350v-F platforms
You must initialize the hardware security module (HSM) installed in each unit before you can use it. This is typically a one-time operation. When you are creating a device group using more than one FIPS platform, you initialize the HSM on one unit, and then initialize the HSM on a peer unit using the same security domain label that you used on the first unit. You can choose to use a different password on the peer unit.
You can initialize the HSM and create the security domain, before you license the system and create a traffic management configuration.
- Log in to the command line of the system using an account with root access.
- Open the TMOS Shell (tmsh).tmsh
- Initialize the HSM and set a security officer (SO) password.run util fips-util initRunning this command deletes all keys in the HSM and makes any previously exported keys unusable.The initialization process takes a few minutes to complete.The initialization process begins. When prompted, type the Security Officer (SO) password. You cannot use the keyworddefaultas the SO password.F5 recommends that you choose a strong value for the SO password.If this text displays in the message below, you need to first delete all keys from the device before running the command:There are keys stored in the FIPS device Delete all keys from the device before re-initializing it. You can use the-foption to force initialization, which deletes all user-generated keys (util fips-util -f init).WARNING: This erases all keys from the FIPS 140 device. Any configuration objects dependent on FIPS keys will cause the configuration fail to load. ==================== WARNING ================================ The FIPS device will be reset to factory default state. All keys and user identities currently stored in the device will be erased. Any configuration objects dependent on FIPS keys will cause the configuration fail to load. Press <ENTER> to continue or Ctrl-C to cancel Resetting the device ... The FIPS device is now in factory default state. Enter new Security Officer password (min. 7, max. 14 characters): Re-enter Security Officer password:
- When this message displays, type a security domain label.NOTE: security domain label must be identical on peer FIPS devices in order to be able to synchronize with them. Enter security domain label (max. 50 chars, default: F5FIPS):Be sure to keep the security domain label and password in a secure location. You need the domain label and password when you initialize the HSM on a peer unit. You can use the same password or choose a new one. This information is also required when replacing a unit (for RMA or other reasons). Since keys are synchronized from the working unit to a new unit, the domain label and password are required.Initializing new security domain (F5FIPS)... Creating crypto user and crypto officer identities Waiting for the device to re-initialize ... Creating key encryption key (KEK) The FIPS device has been initialized.
- Enable the HSM device using one of these options:
- Reboot the unit.
- Restart all services:restart sys service all.Restarting services disrupts load-balanced traffic and might terminate remote login sessions to the system.
After you complete the initialization process on the first unit, you can initialize a peer system and add it to the security domain of the first unit. You can choose to use the same SO password that you used on the first unit.
Initialize the HSM in i5000F (i5820-DF)/i7000F (i7820-DF)/i15000-DF (i15820-DF) platforms
You must initialize the hardware security module (HSM) installed in each unit before you can use it. This is typically a one-time operation. When you are creating a device group using more than one FIPS platform, you initialize the HSM on one unit, and then initialize the HSM on a peer unit using the same security domain label that you used on the first unit. You can choose to use a different password on the peer unit.
You can initialize the HSM and create the security domain, before you license the system and create a traffic management configuration.
- Log in to the command line of the system using an account with root access.
- Open the TMOS Shell (tmsh).tmsh
- Initialize the HSM and set a security officer (SO) password.run util fips-util initRunning this command deletes all keys in the HSM and makes any previously exported keys unusable.The initialization process takes a few minutes to complete.The initialization process begins. When prompted, type the Security Officer (SO) password. You cannot use the keyworddefaultas the SO password.F5 recommends that you choose a strong value for the SO password.If this text displays in the message below, you need to first delete all keys from the device before running the command:There are keys stored in the FIPS device Delete all keys from the device before re-initializing it. You can use the-foption to force initialization, which deletes all user-generated keys (util fips-util -f init).WARNING: This erases all keys from the FIPS 140 device. Any configuration objects dependent on FIPS keys will cause the configuration fail to load. ==================== WARNING ================================ The FIPS device will be reset to factory default state. All keys and user identities currently stored in the device will be erased. Any configuration objects dependent on FIPS keys will cause the configuration fail to load. Press <ENTER> to continue or Ctrl-C to cancel Resetting the device ... The FIPS device is now in factory default state. Enter new Security Officer password (min. 7, max. 14 characters): Re-enter Security Officer password:
- When this message displays, type a security domain label.NOTE: security domain label must be identical on peer FIPS devices in order to be able to synchronize with them. Enter security domain label (max. 49 chars, default: F5FIPS):Be sure to keep the security domain label and password in a secure location. You need the domain label and password when you initialize the HSM on a peer unit. You can use the same password or choose a new one. This information is also required when replacing a unit (for RMA or other reasons). Since keys are synchronized from the working unit to a new unit, the domain label and password are required.Initializing new security domain (F5FIPS)... Creating crypto user and crypto officer identities Waiting for the device to re-initialize ... Creating key encryption key (KEK) The FIPS device has been initialized.
- Enable the HSM device using one of these options:
- Reboot the unit.
- Restart all services:restart sys service all.Restarting services disrupts load-balanced traffic and might terminate remote login sessions to the system.
After you complete the initialization process on the first unit, you can initialize a peer system and add it to the security domain of the first unit. You can choose to use the same SO password that you used on the first unit.
View HSM information using tmsh
You can use the TMOS Shell (
tmsh
) to view
information about the hardware security module (HSM) on BIG-IP systems. If you have a
10350v-FIPS platform provisioned for Virtual Clustered Multiprocessing (vCMP),
you can also view information about any FIPS partitions on the HSM.- Log in to the command line of the system using an account with root access.
- Open the TMOS Shell (tmsh).tmsh
- View information about the HSM.run util fips-util infoDepending on the HSM installed in your system, a summary similar to this example (from a 10350 platform) displays.Label: F5FIPS Model: NITROX-III CNN35XX-NFBE Serial Number: 3.0G1501-ICM000059 FIPS state: 2 MaxSessionCount: 2048 SessionCount: 13 MaxPinLen: 14 MinPinLen: 7 TotalPublicMemory: 557540 FreePublicMemory: 234552 TotalUserKeys: 10075 AvailableUserKeys: 10075 Logging failures: user: 0 officer: 0 Temperature: 72 C HW version: 0.0 Firmware version: CNN35XX-NFBE-FW-1.0-27
- View information about FIPS partitions on the HSM.run util fips-util ptninfo
Before you synchronize the HSMs
Before you can synchronize the FIPS hardware security modules (HSMs), you must ensure that the target HSM:
- Is already initialized
- Has an identical security domain name
- Does not contain existing keys
- Is the same hardware model
- Contains the same firmware version
Before you run the
fips-card-sync
command, ensure that you have this information:- The Security Officer (SO) password for the source F5 device
- The SO password for the target F5 device
- The root password for the target F5 device
The target device must also be reachable using SSH from the source device.
Synchronize the HSMs using tmsh
Be sure that you meet all
prerequisites before synchronizing the hardware security modules (HSMs) in
your devices.
Synchronizing the HSMs enables you
to copy keys from one HSM to another. This is also required to synchronize the
software configuration in a device group.
You only need to perform the synchronization process
during the initial configuration of a pair of devices. After the two
devices are in sync, they remain in sync.
- Log on to the command line of the source F5 device using an account with root access.
- Open the TMOS Shell (tmsh).tmsh
- Synchronize the masking from the HSM on the source F5 device to the HSM on the target F5 device, where <hostname> is the IP address or hostname of the target F5 device.run util fips-card-sync<hostname>Be sure to run this command on a device that contains a valid masking key. Otherwise, you might invalidate all keys loaded in the HSM.A masking key is shared between the HSMs on each F5 device. This shared masking key is used to encrypt the SSL private keys when the keys leave the cryptographic boundary of the HSM.
- When prompted, type the security officer (SO) password for the local device.
- When prompted, type the SO password for the remote device or press Enter if the password is the same as for the local device.A message similar to this example displays:Connecting to 192.0.2.255 as user root ...
- When prompted, type the root password.When the synchronization operation completes, a message similar to this example displays:FIPS devices have been synchronized.
- Synchronize the software configuration in the device group.You must runfips-card-syncbefore runningconfig-sync. Otherwise, the FIPS keys will not load on the remote device.run cm config-sync [to-group|from-group] <device-group-name>
HSM management on F5 rSeries platforms
On F5 rSeries platforms with an embedded HSM, you manage the hardware security module (HSM) from the system CLI. This includes initializing the HSM and managing FIPS partitions. You can also view HSM information and manage FIPS partitions from the F5OS webUI.
You perform key management tasks at the tenant level from the TMOS Shell (
tmsh
) using utilities that are also available on BIG-IP platforms with an embedded HSM. For more information, see Key management on embedded FIPS systems.HSM management from the CLI
You can manage the hardware security module (HSM) and FIPS
partitions from the CLI.
Initialize the HSM in F5 r5000/r10000 platforms
The hardware security module (HSM) installed in your F5 r5000/r10000 FIPS platform is uninitialized by default. You must initialize the HSM before you can use it. This is typically a one-time operation.
- Log in to the command line interface (CLI) of the system using an account with admin access.When you log in to the system, you are in user (operational) mode.
- Initialize the HSM and set a security officer (SO) password.Forcing the initialization deletes all keys in the HSM and makes any previously-exported keys unusable.fips hsm force-initWhen prompted, type an SO password. You cannot use the keyworddefaultas the SO password.F5 recommends that you choose a strong value for the SO password and keep it in a secure location.Value for 'new-so-password' (<string, min: 7 chars, max: 30 chars>): ******** Value for 'confirm-new-so-password' (<string, min: 7 chars, max: 30 chars>): ********The initialization process begins and might take a few minutes to complete..Initialization is complete, when this message displays:result The FIPS device has been initialized.
After you complete the initialization, you create a FIPS partition.
Create a FIPS partition from the CLI
After initializing the HSM, these resources are assigned to a single default FIPS partition called PARTITION_1 (also called a virtual HSM):
- Number of keys that the FIPS partition can hold. The range is from 1 to 1000000.
- Number of acceleration devices (or acceleration cores) for the FIPS partition. The range is from 1 to 63. F5 r5000-DF platforms support up to 32 acceleration devices, and F5 r10000-DF platforms support up to 63 acceleration devices.
Before you can create a new FIPS partition from the CLI, you must first deallocate resources from the default partition so that they can be assigned to any new partitions.
F5 r5000-DF platforms support up to 24 FIPS partitions, and F5 r10000-DF platforms support up to 32 FIPS partitions.
- Log in to the command line interface (CLI) of the system using an account with admin access.When you log in to the system, you are in user (operational) mode.
- View information about the default FIPS partition.show fips partitionsA summary similar to this example displays:appliance-1# show fips partitions OCCUPIED ACCEL FIPS SESSION SESSION PCI NAME NAME KEYS DEVS BACKUP ID STATE KEYS COUNT ADDRESS ----------------------------------------------------------------------------------------- PARTITION_1 PARTITION_1 10075 63 disabled - 255 0 10 ca:10.0
- Change to config mode.configThe CLI prompt changes to include(config).
- Resize the default partition.fips set-partition name <fips-partition> accel-devs <quantity> keys <quantity> backup {false|true}This example changes PARTITION_1 to use one acceleration device and hold 10 keys:appliance-1(config)# fips set-partition name PARTITION_1 accel-devs 1 keys 10 Value for 'so-password' (<string, min 7 chars, max 30 chars>): *********** result fips partition PARTITION_1 has been resized
- Create a new FIPS partition.fips set-partition name <fips-partition> accel-devs <quantity> keys <quantity> backup {false|true}If you plan to migrate keys from an iSeries FIPS platform and restore to this FIPS partition on your rSeries FIPS platform, be sure to set thebackupoption totrue.This example creates PARTITION_2:appliance-1(config)# fips set-partition name PARTITION_2 accel-devs 12 keys 128 backup true Value for 'so-password' (<string, min 7 chars, max 30 chars>): *********** result fips partition PARTITION_2 has been created
- Verify the FIPS partition information.show fips partitionsA summary similar to this example displays:appliance-1# show fips partitions OCCUPIED ACCEL FIPS SESSION SESSION PCI NAME NAME KEYS DEVS BACKUP ID STATE KEYS COUNT ADDRESS ----------------------------------------------------------------------------------------- PARTITION_1 PARTITION_1 20 1 disabled - 255 0 10 ca:10.0 PARTITION_2 PARTITION_2 128 12 disabled - - - - ca:10.2
After you complete the initialization, you create a tenant that uses the FIPS partition.
Create a tenant with a FIPS partition from the CLI
After you create a FIPS partition, you can create a tenant and assign the FIPS partition to it from the CLI.
F5 rSeries FIPS platforms support only tenants running BIG-IP software version 17.1.0.1 or later.
- Log in to the command line interface (CLI) of the system using an account with admin access.When you log in to the system, you are in user (operational) mode.
- Change to config mode.configThe CLI prompt changes to include(config).
- Create and deploy a tenant that uses a FIPS partition.tenants tenant <name> config type BIG-IP image <filename>.bundle fips-partition <partition-name> cryptos enabled vcpu-cores-per-node <cores> nodes <node> mgmt-ip <ip-address> prefix-length <prefix> gateway <ip-address> memory <memory> running-state deployed vlans <vlan-ids>This example creates a BIG-IP tenant calledbig-ipthat uses a FIPS partition named PARTITION_2:appliance-1(config)# tenants tenant big-ip config type BIG-IP image BIGIP-17.1.0.1-0.0.0.ALL-F5OS.qcow2.zip.bundle fips-partition PARTITION_2 cryptos enabled vcpu-cores-per-node 6 nodes 1 mgmt-ip 192.0.2.42 prefix-length 24 gateway 192.0.2.254 memory 22016 running-state deployed vlans 11
After you complete the initialization, you initialize the FIPS partition from the tenant CLI.
Initialize the HSM partition in F5OS tenants from the CLI
You must initialize the hardware security module (HSM) partition assigned to a tenant before you can use it.
You can initialize the HSM and create the security domain before you license the system and create a traffic management configuration.
- Log in to the command line interface (CLI) of the tenant using an account with admin access.
- Open the TMOS Shell (tmsh).tmsh
- Initialize the HSM and set a security officer (SO) password.run util fips-util initRunning this command deletes all keys in the HSM and makes any previously exported keys unusable.The initialization process takes a few minutes to complete.The initialization process begins. When prompted, type the Security Officer (SO) password. You cannot use the keyworddefaultas the SO password.F5 recommends that you choose a strong value for the SO password.If this text displays in the message below, you need to first delete all keys from the device before running the command:There are keys stored in the FIPS device Delete all keys from the device before re-initializing it. You can use the-foption to force initialization, which deletes all user-generated keys (util fips-util -f init).WARNING: This erases all keys from the FIPS 140 device. Any configuration objects dependent on FIPS keys will cause the configuration fail to load. ==================== WARNING ================================ The FIPS device will be reset to factory default state. All keys and user identities currently stored in the device will be erased. Any configuration objects dependent on FIPS keys will cause the configuration fail to load. Press <ENTER> to continue or Ctrl-C to cancel Resetting the device ... The FIPS device is now in factory default state. Enter new Security Officer password (min. 7, max. 14 characters): Re-enter Security Officer password:
- When this message displays, type a security domain label.NOTE: security domain label must be identical on peer FIPS devices in order to be able to synchronize with them. Enter security domain label (max. 49 chars, default: F5FIPS):Be sure to keep the security domain label and password in a secure location. You need the domain label and password when you initialize the HSM on a peer unit. You can use the same password or choose a new one. This information is also required when replacing a unit (for RMA or other reasons). Since keys are synchronized from the working unit to a new unit, the domain label and password are required.Initializing new security domain (F5FIPS)... Creating crypto user and crypto officer identities Waiting for the device to re-initialize ... Creating key encryption key (KEK) The FIPS device has been initialized.
- Enable the HSM device using one of these options:
- Reboot the unit.
- Restart all services:restart sys service all.Restarting services disrupts load-balanced traffic and might terminate remote login sessions to the system.
View HSM information in the CLI
You can view information about the embedded hardware security module (HSM) on F5 r5000-DF/r10000-DF FIPS systems from the CLI.
If the State is 2, the HSM is initialized. If the State is -1, the HSM is not initialized.
- Log in to the command line interface (CLI) of the system using an account with admin access.When you log in to the system, you are in user (operational) mode.
- View information about the HSM.show fips statusA summary similar to this example displays.appliance-1# show fips status fips status last-updated "Tue Nov 15 18:50:02 2022\n" fips status state 2 fips status desc "FIPS mode with single factor authentication" fips status label cavium fips status model "NITROX-III CNN35XX-NFBE" fips status part-number CNN3560-NFBE-3.0-G fips status serial-number 6.0G2139-VPM006082 fips status firmware-major-version 8 fips status firmware-minor-version 2 fips status hw-major-version 54 fips status hw-minor-version 48 fips status build-number 11-25 fips status firmware-id CNN35XX-NFBE-FW-2.08-11-25 fips status temperature "53 C" fips status wear-leveling DEVICE_STATUS_OK
HSM management from the webUI
You can manage the hardware security module (HSM) and FIPS
partitions from the F5OS webUI.
Display HSM information from the webUI
The HSM Details screen lists
read-only information about the embedded hardware security module (HSM) on F5
r5000-DF/r10000-DF FIPS systems. This screen shows information, such as state,
part/serial numbers, firmware/hardware versions, build number, temperature,
and wear leveling.
If the State is 2,
the HSM is initialized. If the State is -1, the HSM is not
initialized.
- Log in to the webUI using an account with admin access.
- On the left, click .
Configure the default FIPS partition from the webUI
The FIPS Partitions screen lists FIPS
partitions on the embedded hardware security module (HSM). If the HSM is newly
initialized, the FIPS Partitions screen lists only the default partition
(PARTITION_1). If the HSM needs to be initialized, no FIPS partitions are
listed. For more information on initializing the HSM, see Initialize the HSM in F5 r5000/r10000 platforms.
After initializing the HSM,
all resources (keys and acceleration devices) are assigned to a single
default FIPS partition (PARTITION_1). Before you can create a new FIPS
partition from the webUI, you must first deallocate resources from the
default partition so they can be assigned to a new
partition.
- Log in to the webUI using an account with admin access.
- On the left, click .
- Click the default partition name (PARTITION_1).The Edit FIPS Partition screen displays.
- ForKeys, enter the maximum number of keys the FIPS partition can hold.The range is from 1 to 1000000.
- ForAccel Devs, enter the maximum number of acceleration devices used for the FIPS partition.The range is from 1 to 63. F5 r5000-DF platforms support up to 32 acceleration devices, and F5 r10000-DF platforms support up to 63 acceleration devices.
- ForBackup, select whether to enable or disable backup for the FIPS partition.If you plan to migrate keys from an iSeries FIPS platform and restore to this FIPS partition on your rSeries FIPS platform, be sure to selectEnabled.
- ClickSave & Close.
Next, you can create a new custom FIPS partition.
Add FIPS partitions from the webUI
Before you can add a new FIPS partition from the webUI, you must have already deallocated resources from the default partition so they can be assigned to any new partitions.
The FIPS Partitions screen enables you to manage FIPS partitions on the embedded hardware security module (HSM). If the HSM is newly initialized, the FIPS Partitions screen lists only the default partition (PARTITION_1). You can add a new FIPS partition from the webUI.
F5 r5000-DF platforms support up to 24 FIPS partitions, and F5 r10000-DF platforms support up to 32 FIPS partitions.
- Log in to the webUI using an account with admin access.
- On the left, click .
- ForName, enter a name for the FIPS partition.The minimum length is 1 character, and the maximum length is 15 characters.
- ForKeys, enter the maximum number of keys the FIPS partition can hold.The range is from 1 to 1000000.
- ForAccel Devs, enter the maximum number of acceleration devices used for the FIPS partition.The range is from 1 to 63. F5 r5000-DF platforms support up to 32 acceleration devices, and F5 r10000-DF platforms support up to 63 acceleration devices.
- ForBackup, select whether to enable or disable backup for the FIPS partition.If you plan to migrate keys from an iSeries FIPS platform and restore to this FIPS partition on your rSeries FIPS platform, be sure to selectEnabled.
- ClickSave & Close.
Next, you can create a tenant that uses the new FIPS partition and initialize the HSM partition in the tenant. For more information, see Create a tenant with a FIPS partition from the CLI and Initialize the HSM partition in F5OS tenants from the CLI.
F5 rSeries FIPS platforms support only tenants running BIG-IP software version 17.1.0.1 or later.
Key management on embedded FIPS systems
You can manage keys on your embedded
FIPS system from the CLI or the web-based user interface.
FIPS key management using the BIG-IP Configuration utility
You can use the BIG-IP Configuration utility to create FIPS keys, import existing FIPS keys into a hardware security module (HSM), and convert existing keys into FIPS keys.
Existing FIPS keys (.exp files) can be imported only into an HSM that possesses the same partition masking key (AES-256 key for key wrapping and used to import/export CSPs and masked objects) that was used when the FIPS keys were exported. The masking key is used to encrypt SSL private keys as they are exported from an HSM. Therefore, only the same masking key can be used to decrypt the SSL private keys as they are imported into the HSM.
Import of FIPS keys is supported if the F5 system uses the same masking key that was used to export the FIPS keys.
Request a FIPS-type CA-signed certificate
You can use
the Configuration utility to create a request for a certificate with FIPS
type security from a certificate authority.
- On the Main tab, click .A list of certificates installed on the system displays.
- ClickCreate.The New SSL Certificate screen opens.
- In theNamefield, type a unique name for the certificate.
- From theIssuerlist, specify the type of certificate that you want to use.
- To request a certificate from a CA, selectCertificate Authority.
- For a self-signed certificate, selectSelf.
- Configure theCommon Namesetting and any other settings as needed.
- From theSecurity Typelist, selectFIPS.
- From theKey Typelist, selectRSA,DSA, orECDSA.
- If you selectedECDSA, then from theCurvelist, select an elliptic curve.The elliptic curve secp521r1 is not supported on the F5 10350v-FIPS hardware platform.
- ClickFinished.
Import keys using the BIG-IP Configuration
utility
You can use the BIG-IP
Configuration utility to import existing keys into the system.
- On the Main tab, click .This displays the list of certificates installed on the system.
- ClickImport.
- From theImport Typelist, selectKey.
- For theKey Namesetting, clickCreate New.
- In theKey Namefield, type a name for the key.
- From theKey Sourcesetting, click eitherUpload FileorPaste Text.
- If you clickUpload File, type a file name or clickBrowseand select a file.
- If you clickPaste Text, copy the text from another source and paste the text into the Key Source screen.
- ClickImport.
After you import the key, you can
convert it to a FIPS key.
Convert a key to FIPS using the BIG-IP Configuration
utility
You can use the BIG-IP
Configuration utility to convert an existing key to a FIPS key.
- On the Main tab, click .This displays the list of certificates installed on the system.
- Click a certificate name.This displays the properties of that certificate.
- On the menu bar, clickKey.This displays the type and size of the key associated with the certificate.
- ClickConvert to FIPSto convert the key to a FIPS key.The key is converted and appears in the list as a FIPS key. After the key is converted, this process cannot be reversed.
FIPS key management using tmsh
You can use the TMOS Shell (
tmsh
) to create FIPS keys,
import existing keys into an F5 system, and convert existing keys to FIPS
keys.Create FIPS keys using tmsh
You can use the TMOS Shell
(
tmsh
) to create
FIPS keys.- Log in to the command line of the system using an account with root access.
- Open the TMOS Shell (tmsh).tmsh
- Create a basic key.create sys crypto key <key-object-name> security-type fipsFor information about additional options for this command, view thesys crypto keyman page:help sys crypto keyThe key creation process takes a few minutes to complete.
- View information about the generated key.list sys crypto key <key-object-name>
Import FIPS keys using tmsh
You can use the TMOS Shell
(
tmsh
) to import
existing keys into the system.- Log in to the command line of the system using an account with root access.
- Open the TMOS Shell (tmsh).tmsh
- Import a key.install sys crypto key <key-object-name> from-local-file <path-to-key_file> security-type fipsThis example imports a FIPS key namedmykeyfrom a local key file stored in the/shared/tmpdirectory:install sys crypto key mykey from-local-file /shared/tmp/mykey.exp security-type fips
Convert a key to FIPS using tmsh
You can use the TMOS Shell
(
tmsh
) to convert
a key to a FIPS key.- Log in to the command line of the system using an account with root access.
- Open the TMOS Shell (tmsh).tmsh
- Convert an existing key to FIPS.install sys crypto key <key-object-name>from-local-file <key-file-path>security-type fips
List FIPS keys in the HSM using tmsh
You can use the TMOS Shell
(
tmsh
) to list
the FIPS keys in the hardware security module (HSM).- Log in to the command line of the system using an account with root access.
- Open the TMOS Shell (tmsh).tmsh
- List the keys in the HSM.tmsh show sys crypto fips keyA summary similar to this example displays:------------------------------------------- FIPS 140 Hardware Device ------------------------------------------- === private keys (2) ID MOD.LEN(bits) dd83774207ea554ba1192439de75e1c1 2048 /Common/testkey1.key d750c989e6afeb5ac8ca8aec2b93461b 1024 /Common/testkey2.key
List FIPS keys in the F5 software configuration using
tmsh
You can use the TMOS Shell
(
tmsh
) to list
the FIPS keys in the F5 software configuration.- Log in to the command line of the system using an account with root access.
- Open the TMOS Shell (tmsh).tmsh
- List the keys in the hardware security module (HSM).tmsh list sys crypto keyA summary similar to this example displays:sys crypto key default.key { key-size 1024 key-type rsa-private security-type normal } sys crypto key testkey2.key { key-id d750c989e6afeb5ac8ca8aec2b93461b key-size 1024 key-type rsa-private security-type fips } sys crypto key testkey1.key { key-id dd83774207ea554ba1192439de75e1c1 key-size 2048 key-type rsa-private security-type fips }
Delete a key from the F5 software configuration and HSM
using tmsh
You can use the TMOS Shell
(
tmsh
) to delete
a key from the F5 software configuration and the hardware security module
(HSM).- Log in to the command line of the system using an account with root access.
- Open the TMOS Shell (tmsh).tmsh
- Delete a specified key.delete sys crypto key <key-object-name>
Supported FIPS key sizes
These are the supported key sizes for F5 FIPS platforms.
FIPS platform model | Supported key sizes (bits) |
|---|---|
5000 | 1024, 2048, 4096 |
7000 | 1024, 2048, 4096 |
10200 | 1024, 2048, 4096 |
10350 | 2048 |
i5000 | 2048 |
i7000 | 2048 |
i15000 | 2048 |
r5000 | 2048, 3072, 4096 |
r10000 | 2048, 3072, 4096 |
Additional FIPS platform management tmsh
commands
This table lists additional
tmsh
commands that you can use
to manage your FIPS platform.Command |
Description |
|---|---|
show sys crypto fips
key |
Lists information about FIPS keys
stored in the FIPS hardware security module (HSM), including
FIPS key ID, length, type, and key objects. |
list sys crypto
key |
Lists keys in the F5 software
configuration. |
delete sys crypto fips key
< key-id > |
Deletes a FIPS key from the FIPS HSM
only. |
FIPS system backup and restore
If needed, you can back up and restore FIPS keys, users, and configuration from one embedded FIPS platform to another. The method used depends on the platforms with which you are working.
Download the cavium_migration_tools utilities
You can download the
cavium_migration_tools
utilities from F5 to migrate FIPS configuration data from a BIG-IP iSeries
FIPS system to an F5 rSeries FIPS system.- On your management workstation, log in to my.f5.com/manage/s/downloads.
- Read the End User License Agreement and Program Terms and select the check box.You must accept the license agreement and program terms before you can proceed.
- ClickNext.
- UnderSelect a product family, selectF5OS.
- UnderTell us more about your product, forProduct Line, selectF5OS Appliance Software.
- ForProduct Version, select the version to download.
- UnderSelect a product container, select the software that you want to download.
- UnderSelect a download file, selectcavium_migration_tools.
- ForDownload locations, select a download location.
- ClickDownload.
- Download the corresponding checksum file and README file.The corresponding checksum file has the same name, except that.md5is the file extension. After the download completes, verify the integrity of the file by checking the MD5 checksum.
After you download the utility from
F5, copy the file to both the F5 rSeries FIPS host system and
tenant.
BIG-IP 10350v-F/iSeries to F5 rSeries
You can back up data from a BIG-IP 10350v-F/iSeries FIPS platform and restore it to an F5 rSeries FIPS platform. Before you can restore to an F5 rSeries FIPS system, the HSM must be initialized. For more information, see Initialize the HSM in F5 r5000/r10000 platforms.
Prerequisites
Before you perform a backup and restore on your F5 FIPS platform with an embedded hardware security module (HSM), you must ensure that you have a remote system that has access to both systems. You must also meet prerequisites on the source and target systems.
BIG-IP 10350v-F and iSeries systems (source)
- You have CLI access to the system.
- You have root access to the system.
- You have the FIPS HSM Security Officer (SO) password.
- You have the security domain label.
- For vCMP guests, ensure that you have verified the SSH host key with all guests. To do this, connect using SSH from all guests and accept the host key verification.
- For systems that include a 3rd generation card (serial number starts with 3.0Gor cards manufactured on or before 2017), see BIG-IP 10350v-F/iSeries to F5 rSeries (3rd generation).
- You are running the latest HSM firmware version. If your system is not running this version, you must upgrade to the required BIG-IP software version and then upgrade the firmware. For more information, see Firmware upgrade for systems running BIG-IP software.
- Create a UCS archive and store the backup file off site in a secure location. For more information, see K13132: Backing up and restoring BIG-IP configuration files with a UCS archive.
- Back up the FIPS key. For more information, see Back up a FIPS key using the n3fipsutil utility.
F5 rSeries systems (target)
- You have CLI access to the system and tenant.
- You have root access to the system and tenant.
- You have the FIPS HSM Security Officer (SO) password.
- You have the security domain label.
- You have created the target/restore FIPS partition with the backup option enabled.
- Your F5 rSeries FIPS partition size is equal to or greater than the number of keys as your source system.
Back up BIG-IP iSeries FIPS key
Before you can back up the FIPS key on your BIG-IP iSeries FIPS system, you must download the
n3fipsutil
utility and use SCP to move the file to a directory on the system, such as /shared/fw-upgrade
. You might need to modify the file permissions with chmod 755 n3fipsutil
. For more information on downloading the utility, see Download the n3fipsutil utility.You can back up the FIPS configuration data, including Security Officer (SO) password, FIPS domain, and keys, on a BIG-IP iSeries FIPS system using the
n3fipsutil
utility.To back up a FIPS key on a vCMP system, log in to the vCMP guest and perform a backup. If there are multiple guests, perform a FIPS key backup from each guest running on the vCMP system.
- Connect to the system using the serial console or by opening an SSH session to the management IP address.
- Log in to the command line of the system using an account with admin access.
- Stop all services.tmsh stop sys service all
- Create an empty directory for the backup.
- Run then3fipsutilutility../n3fipsutil -backup <dir-name> [ -n <partition-name> ] [ -host mgmt-ip ]The[ -n partition-name ]option is optional and applicable only if the system uses custom partition names.The[ -host mgmt-ip ]option must be used only at vCMP mode from vCMP Guest, andmgmt-ipis the host management IP address.
- Restart all services.tmsh start sys service all
- Use SCP to copy the entire backup directory, without modifying the contents of the directory, off site to a secure location.The backup directory contains the encrypted FIPS keys and also containsokbk.keyandpokbk.key, which are generated during the backup process. Be sure to secure these keys using your best standard process to secure the confidentiality of HSM FIPS keys.
Next, you extract necessary data from the rSeries tenant.
Extract pekcv output from an F5 rSeries tenant
Before you begin, use SCP to copy only the
PCO fixed key (
pokbk.key
) from the BIG-IP iSeries backup folder to the F5
rSeries tenant to a directory on the system, such as /shared/images
.You can extract
pekcv
output needed for the
data migration from the F5 rSeries tenant using the cavium_migration_tools
utilities.- Connect to the system using the serial console or by opening an SSH session to the management IP address.
- Log in to the command line of the tenant using an account with root access.
- Stop all services.tmsh stop sys service all
- Extract the downloadedcavium_migration_tools.tar file.tar -xvf <tar-file>
- Run thefipsutil_v2_brutility and enter the Security Officer (SO) password when prompted.Be sure to make note of thepekcvoutput displayed, as you will need it for the script that you will run on the F5 rSeries host../fipsutil_v2_br -irestore <path-to-pokbk.key-file> -n <partition-name>This example shows running the utility on a specified partition:./fipsutil_v2_br -irestore pokbk.key-file -n partition_2 Running iSeries Restore.. Enter Security Officer password: Storing user fixedkey Result: SUCCESS pekcv: 569a16bc12345d72361ef8ab0cdef165e12345abc42340b266a3a12345eb7ce Pre-requisites to perform restoration of 1.x backup is done!
Next, you restore data to the F5 rSeries
host.
Restore to an F5 rSeries host
Before you begin, use SCP to copy the BIG-IP iSeries FIPS configuration backup folder to a directory on the F5 rSeries host system, such as
/var/tmp
. You can restore the FIPS configuration that you backed up from a BIG-IP iSeries FIPS system to an F5 rSeries FIPS system host.
- Connect to the system using the serial console or by opening an SSH session to the management IP address.
- Log in to the command line of the system using an account with root access.
- Extract the downloadedcavium_migration_tools.tar file.tar -xvf <tar-file>
- Run thefipsutil_v2_rutility and enter the Security Officer (SO) password when prompted.Use thepekcvoutput that you extracted from the F5 rSeries tenant earlier../fipsutil_v2_r -restore <backup-folder> -n <partition-name> -pekcv <pekcv>The[ -n partition-name ]option is the name of the FIPS partition in which the tenant is launched.The[ backup-folder ]option is the BIG-IP iSeries backup folder.The[ -pekcv ]option includes the string displayed after running thefipsutil_v2_brutility on the rSeries tenant.This example shows running the utility on a specified FIPS partition:./fipsutil_v2_r -restore fips_keys -n partition_2 -pekcv 569a16bc12345d72361ef8 ab0cdef165e12345abc42340b266a3a12345eb7ce Starting Restoration process Restore.. Input directory: fips_keys/ Enter Security Officer password(host): Storing MCO Fixed key is success. Restore of HSM partition partition_2 SUCCESS On Tenant Perform fipsutil_v2_br -loginreset -n <partition-name>
Next, you restore data to the F5 rSeries tenant.
Complete restoration to an F5 rSeries tenant
You can complete post-restoration operations and restart the services.
- Connect to the system using the serial console or by opening an SSH session to the management IP address.
- Log in to the command line of the tenant using an account with root access.
- Change to the directory that contains the extracted .tar file.
- Run thefipsutil_v2_brutility and enter the Security Officer (SO) password that you used on the BIG-IP iSeries FIPS (source) system when prompted../fipsutil_v2_br -loginreset -n <partition-name>This example shows running the utility on a specified partition:./fipsutil_v2_br -loginreset -n partition_2 Running post iSeries restore operations.. Enter Security Officer password: Enter Security Officer password to disable KEYWRAP_CONFIG policy: Post restore operations are done.. Start tmsh services!!
- Restart the services.tmsh restart sys service all
- Perform a UCS restore on the tenant.While the FIPS keys have been migrated to the FIPS HSM, they will not be available for use until you perform a UCS restore to load the full configuration from your BIG-IP iSeries system. For more information, see K13132: Backing up and restoring BIG-IP configuration files with a UCS archive.
- Verify the FIPS keys on the tenant.tmsh show sys crypto fips key
If you want to restore the same backup data onto multiple FIPS partitions on the same host, you must restore them one by one. Only after you have restored a backup on all targeted partitions can you move on to the next backup. When you move on to the next backup, you cannot use previously used backup data on the same host.
If you have high availability (HA) configured for tenants, you must restore the FIPS partition to both tenants and restore the UCS configuration to any one tenant. Then you can add both the tenants to the config sync cluster.
BIG-IP 10350v-F/iSeries to F5 rSeries (3rd generation)
You can back up data from a BIG-IP 10350v-F/iSeries FIPS platform that includes a 3.0G FIPS HSM and restore it to an F5 rSeries FIPS platform. Before you can restore to an F5 rSeries FIPS system, the HSM must be initialized. For more information, see HSM management on F5 rSeries platforms.
Use these procedures only if your FIPS HSM has a 3rd generation serial number, and you are running one of these BIG-IP software versions:
- BIG-IP v17.0.0
- BIG-IP v16.1.1
- BIG-IP v15.1.5.1
- BIG-IP v14.1.4.6
If you have high availability (HA) configured for tenants, you must restore the FIPS partition to both tenants.
Prerequisites (3.0G)
Before you perform a backup and restore on your F5
FIPS platform with a 3rd generation embedded hardware security module (HSM), you
must ensure that you have a remote system that has access to both systems. You
must also meet prerequisites on the source and target systems.
BIG-IP 10350v-F and iSeries systems (source)
- You have CLI access to the system.
- You have root access to the system.
- You have the FIPS HSM Security Officer (SO) password.
- You have the security domain label.
- For vCMP guests, ensure that you have verified the SSH host key with all guests. To do this, connect using SSH from all guests and accept the host key verification.
- You are running the latest HSM firmware version. If your system is not running this version, you must upgrade to the required BIG-IP software version and then upgrade the firmware. For more information, see Firmware upgrade for systems running BIG-IP software.
- Create a UCS archive and store the backup file off site in a secure location. For more information, see K13132: Backing up and restoring BIG-IP configuration files with a UCS archive.
- Back up the FIPS key. For more information, see Back up a FIPS key using the n3fipsutil utility.
F5 rSeries systems (target)
- You have CLI access to the system and tenant.
- You have root access to the system and tenant.
- You have the FIPS HSM Security Officer (SO) password.
- You have the security domain label.
- You have created the target/restore FIPS partition with the backup option enabled.
- Your F5 rSeries FIPS partition size is equal to or greater than the number of keys as your source system.
Back up BIG-IP iSeries FIPS key (3.0G)
Before you can back up the FIPS key on your BIG-IP iSeries FIPS system, you must download the
n3fipsutil
utility and use SCP to move the file to a directory on the system, such as /shared/fw-upgrade
. You might need to modify the file permissions with chmod 755 n3fipsutil
. For more information on downloading the utility, see Download the n3fipsutil utility.You can back up the FIPS configuration data, including Security Officer (SO) password, FIPS domain, and keys, on a FIPS system with a 3rd generation hardware security module (HSM) using the
n3fipsutil
utility.To back up a FIPS key on a vCMP system, log in to the vCMP guest and perform a backup. If there are multiple guests, perform a FIPS key backup from each guest running on the vCMP system.
- Connect to the system using the serial console or by opening an SSH session to the management IP address.
- Log in to the command line of the system using an account with admin access.
- Create an empty directory for the backup.
- Run then3fipsutilutility../n3fipsutil -exportAll <dir-name> [ -n <partition-name> ]The[ -n partition-name ]option is optional and applicable only if the system uses custom partition names.
- Perform a UCS backup on the tenant.For more information, see K13132: Backing up and restoring BIG-IP configuration files with a UCS archive.
- Use SCP to copy the entire backup directory, without modifying the contents of the directory, off site to a secure location.
Next, you extract necessary data from the rSeries tenant.
Restore data to an F5 rSeries tenant (3.0G)
Before you can restore data, be sure that you have used SCP to copy the source system FIPS partition backup folder to the new tenant on the target system.
You can restore backed up data to the tenant on the target FIPS rSeries system.
- Connect to the system using the serial console or by opening an SSH session to the management IP address.
- Log in to the command line of the tenant using an account with root access.
- Change to the directory that contains the extracted .tar file.
- Run then3fipsutilutility../n3fipsutil -importKeys <dir-name> [ -n <partition-name> ]The[ -n partition-name ]option is optional and applicable only if the system uses custom partition names.
- Restart the services.tmsh restart sys service all
- Perform a UCS restore on the tenant.While the FIPS keys have been migrated to the FIPS HSM, they will not be available for use until you perform a UCS restore to load the full configuration from your BIG-IP iSeries system. For more information, see K13132: Backing up and restoring BIG-IP configuration files with a UCS archive.
- Verify the FIPS keys on the tenant.tmsh show sys crypto fips key
If you have high availability (HA) configured for tenants, you must restore the FIPS partition to both tenants.
F5 rSeries to F5 rSeries
You can back up data from on F5 rSeries FIPS platform and restore it to another rSeries FIPS platform. Before you can restore to an F5 rSeries FIPS system, the HSM must be initialized. For more information, see HSM management on F5 rSeries platforms.
If you want to restore the same backup data to multiple FIPS partitions on the same host, you must do the restore on each partition, one by one. Only after restoring a backup on all targeted FIPS partitions should you move on to the next partition. Once you have moved on to the next FIPS partition, you cannot use the previously used backup data on the same host system.
If you have high availability (HA) configured for tenants, you must restore the FIPS partition to both tenants.
Prerequisites
Before you perform a backup and restore on your F5 FIPS platform with an embedded hardware security module (HSM), you must ensure that you have a remote system that has access to both systems. You must also meet prerequisites on the source and target systems.
F5 rSeries systems (source)
- You have CLI access to the system.
- You have root access to the system.
- You have the FIPS HSM Security Officer (SO) password.
- You have the security domain label.
- You are running the latest HSM firmware version. If your system is not running this version, you must upgrade to the required F5OS software version, and then upgrade the firmware using thefips set-firmwarecommand. For more information, see the "Software management overview" section inF5 rSeries Systems: Administration and Configurationat Documentation - F5OS-A and F5 rSeries.
- You have created the source/backup FIPS partition with the backup option enabled.
F5 rSeries systems (target)
- You have CLI access to the system and tenant.
- You have root access to the system and tenant.
- You have the FIPS HSM Security Officer (SO) password.
- You have the security domain label.
- You are running the latest HSM firmware version. If your system is not running this version, you must upgrade to the required F5OS software version, and then upgrade the firmware using thefips set-firmwarecommand. For more information, see the "Software management overview" section inF5 rSeries Systems: Administration and Configurationat Documentation - F5OS-A and F5 rSeries.
- You have created the target/restore FIPS partition with the backup option enabled.
- Your F5 rSeries FIPS partition is the same size (number of keys) as your source rSeries system.
Back up FIPS data on an F5 rSeries tenant
You can back up data to migrate from one F5 rSeries tenant to another rSeries tenant using the
cavium_migration_tools
utilities.- Connect to the system using the serial console or by opening an SSH session to the management IP address.
- Log in to the command line of the tenant using an account with root access.
- Stop all services.tmsh stop sys service all
- Extract the downloadedcavium_migration_tools.tar file.tar -xvf <tar-file>
- Create an empty directory for the backup.
- Run thefipsutil_v2_brutility and enter the Security Officer (SO) password when prompted../fipsutil_v2_br -backup <directory-name> -n <partition-name>Since this backup data contains the encrypted SO password, the existing SO password is overwritten after a successful restore. Be sure to remember or make note of which SO password is applicable when performing the backup.This example shows running the utility on a specified partition:./fipsutil_v2_br -backup pokbk.key-file -n partition_2
- Restart all services.tmsh start sys service all
- Use SCP to copy the entire backup directory, without modifying the contents of the directory, to a remote system that both the host system and tenant can access.
Next, you back up data from the F5 rSeries host system.
Back up FIPS data on an F5 rSeries host
You can back up data on an F5 rSeries host
system when migrating to another rSeries host.
- Connect to the system using the serial console or by opening an SSH session to the management IP address.
- Log in to the command line of the tenant using an account with root access.
- Use SCP to copy the/var/F5/shared/fips/certs/MCO-fixed.keyfile from the FIPS host system to the new backup directory that you created when backing up the tenant data.The backup directory contains the encrypted FIPS keys, encrypted users (including Security Officer), FIPS partition configuration data, and keys (MCO-fixed.keyandPCO-fixed.key) that are generated during backup process.Be sure to secure these keys using standard best practices, to maintain the confidentiality of HSM FIPS keys.
Use SCP to copy the
/var/F5/shared/fips/certs/MCO-fixed.key
file from the source
FIPS host system to target FIPS host system. Next, you restore data to the F5
rSeries host system. Restore to an F5 rSeries host
Before you restore data, be sure that you
have performed these tasks:
- Initialized the hardware security module (HSM) in the target system. For more information, see HSM management on F5 rSeries platforms.
- Used SCP to copy the/var/F5/shared/fips/certs/MCO-fixed.keyfile from the source FIPS host system to target FIPS host system.
You can restore the FIPS configuration that
you backed up from a F5 rSeries FIPS system to another rSeries FIPS
system.
- Connect to the system using the serial console or by opening an SSH session to the management IP address.
- Log in to the command line of the system using an account with root access.
- Extract the downloadedcavium_migration_tools.tar file.tar -xvf <tar-file>
- Run thefipsutil_v2_rutility../fipsutil_v2_r -restore -storeMCOKey <path-to-MCO-fixed-key>
Use SCP to copy the source system FIPS
partition backup folder to the new tenant on the target system. Next, you
restore data to the F5 rSeries tenant.
Restore data to an F5 rSeries tenant
Before you can restore data, be sure that you have used SCP to copy the source system FIPS partition backup folder to the new tenant on the target system.
You can restore backed up data to the tenant on the target FIPS rSeries system.
- Connect to the system using the serial console or by opening an SSH session to the management IP address.
- Log in to the command line of the tenant using an account with root access.
- Stop all services.tmsh stop sys service all
- Change to the directory that contains the extracted .tar file.
- Run thefipsutil_v2_brutility and enter the Security Officer (SO) password that you used on the BIG-IP iSeries FIPS (source) system when prompted../fipsutil_v2_br -restore <backup-dir> -n <fips-partition-name>
- Restart the services.tmsh restart sys service all
- Perform a UCS restore on the tenant.While the FIPS keys have been migrated to the FIPS HSM, they will not be available for use until you perform a UCS restore to load the full configuration from your BIG-IP iSeries system. For more information, see K13132: Backing up and restoring BIG-IP configuration files with a UCS archive.
- Verify the FIPS keys on the tenant.
If you want to restore the same backup data onto multiple FIPS partitions on the same host, you must restore them one by one. Only after you have restored a backup on all targeted partitions can you move on to the next backup. When you move on to the next backup, you cannot use previously used backup data on the same host.
If you have high availability (HA) configured for tenants, you must restore the FIPS partition to both tenants.
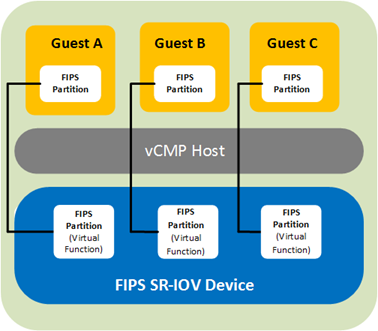
FIPS multi-tenancy for vCMP guests overview
The BIG-IP 10350v-FIPS platform contains a FIPS-validated
hardware security module (HSM) that supports Single Root I/O Virtualization
(SR-IOV) mode on Virtual Clustered Multiprocessing (vCMP)-enabled systems.
Benefit
The benefit of SR-IOV mode is that for a BIG-IP system
on a 10350v-FIPS platform provisioned for Virtual Clustered
Multiprocessing (vCMP), you can create a virtual HSM (known as a FIPS
partition) for each guest on the system. A
FIPS partition
is a portion of cores and private key slots on
the HSM that a host administrator can dedicate to a guest for
cryptographic functions.This illustration shows
a BIG-IP system where three guests each have their own FIPS partition for
FIPS hardware-based processing.
Core allocation
You can create up to 32 FIPS partitions on the HSM, with
some number of cores allocated to each partition. The number of cores you
allocate to a FIPS partition depends on the processing needs of the guest
you assign the partition to. The only limit is that the combined number of
cores for all partitions cannot exceed 63, the total number of cores that
the HSM supports.
To determine how you want to deploy FIPS partitioning
for your vCMP guests, you should:
- Identify the guests that need dedicated cores.
- Decide how many cores and private key slots you want to allocate to each guest's partition.
For example, to decide how many cores to dedicate to
each guest, suppose guests
A
and B
have equal core requirements, but guest C
has twice the needs
of both A
and
B
. In this
case, you could allocate 12 cores each to A
and B
, and 24 cores to
C
. This
would mean a total core allocation of 48 HSM cores, leaving 15 cores
unallocated and available for future guest needs.FIPS private keys
Once you have assigned a FIPS partition to a guest, the
guest administrator can log in to the guest to create, convert, or import
FIPS private SSL keys, which are stored on the HSM. The FIPS partition
assigned to the guest dictates the amount of storage available for FIPS
keys on the HSM for the guest.
Host administration tasks
Before vCMP guest
administrators can create and manage FIPS keys in their own secure partitions
on the FIPS hardware security module (HSM), a host administrator must
initialize the FIPS HSM, resize the default partition to free up cores for
other FIPS partitions, and create those other partitions on the HSM. As host
administrator, you'll create one unique partition for each guest.
Prerequisite tasks for managing FIPS partitions
Before you set up FIPS partitions for your Virtual Clustered Multiprocessing (vCMP) guests, confirm that the vCMP host prerequisites have been met, on each device that hosts vCMP guests in your high availability configuration. Confirm all prerequisites by logging into the BIG-IP system using the management IP address of the vCMP host.
Your BIG-IP user account must have a role of Administrator assigned to it.
Prerequisites | Verification tool | Verification instructions |
|---|---|---|
The BIG-IP system is provisioned for Virtual Clustered Multiprocessing (vCMP). | BIG-IP Configuration utility | On the Main tab, click . In the Module column, locate Virtual CMP (vCMP) and then view the Provisioning column. |
You have created vCMP guests on the system. | BIG-IP Configuration utility | On the Main tab, click . View the list of vCMP guests. |
You have permission to use the TMOS Shell ( tmsh ) command-line interface. | BIG-IP Configuration utility | On the Main tab, click . Then click your account name and view the Terminal Access list. This setting must be set to either tmsh or Advanced shell . |
The license type is 10350v-FIPS. | An SSH application such as PuTTY | At the tmsh prompt, type show sys hardware and under Platform , look for a Name property of 10350F . |
The hardware security module (HSM) is initialized and the security label matches the label on all other devices hosting BIG-IP device group members (that is, vCMP guests). | An SSH application such as PuTTY | At the tmsh prompt, type fips-util -v info . |
The HSMs on the appliances hosting the vCMP guests in the BIG-IP device group are synchronized. | An SSH application such as PuTTY | At the tmsh prompt, type run util fips-card-sync .hostname |
You know the Security Officer password for managing the FIPS HSM. | Not applicable. | If you do not know the Security Officer password, see your security administrator. |
The BIG-IP configurations on all members of the BIG-IP device group (that is, vCMP guests) are synchronized. | BIG-IP Configuration utility | On the Main tab, click . Then verify that all device group members have a status of In Sync . |
For more information, see
BIG-IP Device Service Clustering: Administration
at my.f5.com.FIPS partition size management
After all vCMP guests are deployed with FIPS partitions
assigned to them, you might decide later that you need to increase or decrease
the number of cores for a specific guest.
When you resize a guest's partition, you use the TMOS Shell
(
tmsh
)
command-line interface, and it's helpful to understand the output that
tmsh
displays
during the resizing process. For example, suppose you initially resized
PARTITION_1
and
created three other partitions, with these core allocations:- PARTITION_1: 32 cores
- PARTITION_2: 8 cores
- PARTITION_3: 10 cores
- PARTITION_4: 4 cores
This shows that we have a total of 54 of the 63 cores on the
HSM allocated, leaving 9 cores still unallocated.
Now suppose you decide to adjust the number of cores
allocated to
PARTITION_2
, from 8 cores to 6. In this case, you'll need to
use the fips-util
ptnresize
command within tmsh
. For example, if you
type:tmsh /util fips-util ptnresize
The system prompts you for a password and the relevant
partition name and displays other fields showing their currently-configured
values:
Enter Security Officer password:Enter partition name:SO-passwordPARTITION_2Enter max keys (1-82160, current 5000):4000Enter max accel devs (0 to 25, current 8):
In the
Enter
max accel devs
field, the system shows that there are
0 to 25
cores
available to PARTITION_2
for resizing, with 8
cores currently
allocated. The system calculates this 0 to 25
value using this
formula:(Total cores on the HSM - The sum of cores for the three other partitions) + (cores currently assigned to PARTITION_2)
which translates to:
63 - (32 + 10 + 4) + 8 = 25
Notice that the displayed number of
maximum cores available to
PARTITION_2
(25
) includes the current allocation of 8 cores.For
Enter mac
accel devs
, once you specify a new value of 6
, the number of
unallocated cores on the HSM increases from 9 to 11.Enable vCMP after a BIG-IP software upgrade
If your BIG-IP system was provisioned for
vCMP prior to upgrading to this BIG-IP version, you must enable the
kernel.iommu
BigDB
variable.Be sure to do this
before you manage the hardware security module (HSM) to create FIPS
partitions for vCMP guests.
- Log in to the command line of the system using an account with root access.
- Open the TMOS Shell (tmsh).tmsh
- Enable thekernel.iommuDB variable.modify /sys db kernel.iommu value enable
- Save your BIG-IP configuration.save /sys config
- Reboot the system.sys reboot
Resize the default FIPS partition
When you initialize the FIPS hardware security module (HSM) on a vCMP host, the process creates a FIPS partition named
PARTITION_1
that you can assign to one of your vCMP guests. By default, PARTITION_1
contains all available FIPS cores on the HSM (63).To free up cores for other guests, you'll need to reduce the number of cores assigned to
PARTITION_1
. You can then allocate those freed-up cores to other FIPS partitions that you create. - Log in to the command line of the system using an account with root access.
- Open the TMOS Shell (tmsh).tmsh
- Resize the default partition.fips-util ptnresize
- Enter the Security Officer password.
- At thePartition nameprompt, enter the name of the default partition,PARTITION_1.
- At theEnter max keysprompt, re-type or change the current value for the maximum number of SSL keys allocated to the default partition.
- At theEnter max accel devsprompt, reduce the current value of63.The specified value represents the number of cores currently allocated toPARTITION_1.For example, if you intend to create three guests, and you know that for two of those guests, you'll want to createPARTITION_2andPARTITION_3and allocate 20 and 10 cores respectively, change the value forPARTITION_1from 63 to 33.Changing this value frees up the number of cores that you'll need for the other partitions.
- Press Enter.
- Save your BIG-IP configuration.save /sys config
After you complete this task, the HSM has available cores for you to allocate to other FIPS partitions that you create.
Create FIPS partitions on the HSM
You can create a virtual hardware security module (HSM)
for each vCMP guest on the system that processes FIPS-related traffic.
After creating FIPS partitions on the HSM, you can provide each guest with
its own dedicated FIPS hardware resource to use for cryptographic
functions.
You only need to create a FIPS
partition for a guest when the guest is processing FIPS-related
traffic.
- Open the TMOS Shell (tmsh).tmsh
- Create a FIPS partition.fips-util ptncreateIf you receive an error message about acceleration, you'll need to resize the default FIPS partition before creating FIPS partitions.The system then prompts you for Security Officer password.
- Type the Security Officer password.
- At theEnter partition nameprompt, assign a name to the partition, such asPARTITION_2.Do not assign the namePARTITION_1. This is the name of the default FIPS partition.
- At theMax key countprompt, type the maximum number of private SSL keys that a guest administrator will be able to store in the guest's partition.
- At theMax accel devsprompt, type a value for the number of FIPS hardware cores that you want to allocate to the partition.
- Press Enter.
- Save your BIG-IP configuration.save /sys config
- Repeat for each additional partition that you want to create.
After you complete this task, the HSM
has a unique FIPS partition for each guest that you want to assign FIPS
hardware SSL resources to. You can then provide a guest with its own dedicated
FIPS hardware SSL resource by assigning the FIPS partition to the
guest.
Disable a vCMP guest
Before performing this task, confirm that you are logged in to the BIG-IP Configuration utility as a vCMP host administrator.
Before you assign a FIPS partition to a guest, you must set the guest to the Configured state.
This task is based on the assumption that the guest you want to disable is currently in a Deployed or Provisioned state.
- On the Main tab, click .This displays a list of guests on the system.
- In the Name column, find the name of the guest you want to assign a FIPS partition to, and in the left-most column, select the check box.
- ClickDisable.The guest state changes to Configured.
- Repeat this task for each guest to which you plan on assigning a FIPS partition.
After performing this task, the guest can no longer process traffic, and you can now modify the guest to assign a FIPS partition.
Assign a FIPS partition to a vCMP guest
Before performing this task, confirm
that you are logged into the BIG-IP Configuration utility as a vCMP host
administrator.
For BIG-IP
systems containing a FIPS hardware security module (HSM) on which you have
created FIPS partitions, you can assign a separate FIPS partition to each
vCMP guest on the system. This provides each guest with its own virtual
FIPS HSM to use for cryptographic functions when processing FIPS-related
traffic.
It’s worth noting that in addition to
using FIPS partitions for FIPS-related traffic, you can configure the
SSL Mode
setting for non-FIPS related traffic. This controls the non-FIPS hardware
SSL resources on the system.- On the Main tab, click .This displays a list of guests on the system.
- In the Name column, click the name of the guest that you want to modify.This displays the configured properties of the guest.
- From theFIPS Partitionlist, select a FIPS partition name.
- From theRequested Statelist, selectDeployed.
- ClickUpdate.This action causes the guest to restart.
- Repeat this task for each guest to which you want to assign a FIPS partition.
After you complete this task, each
vCMP guest that you modified has a virtual FIPS HSM assigned to it to use for
cryptographic functions.
Display the list of FIPS partitions on the HSM
When the FIPS
hardware security module (HSM) in your BIG-IP system contains FIPS
partitions for multi-tenancy, you can display a list of the partitions at
any time.
- Open the TMOS Shell (tmsh).tmsh
- View a list of partitions.fips-util ptninfo
- Type the Security Officer password.The system displays a list of existing FIPS partitions on the HSM.
Deleting FIPS partitions on the HSM
When the FIPS
hardware security module (HSM) in your BIG-IP system contains FIPS
partitions for multi-tenancy, you can delete one or more of those
partitions from the HSM if for some reason you no longer need
them.
- Open the TMOS Shell (tmsh).tmsh
- Delete a partition.fips-util ptndeleteThe system prompts you for the Security Officer password.
- Type the Security Officer password.
- At theEnter partition nameprompt, type the name of the partition you want to delete.
- Press Enter.
- Save your BIG-IP configuration.save /sys config
Guest administration tasks
When a vCMP guest has a FIPS partition assigned to it, the guest administrator can store private SSL keys on the FIPS hardware security module (HSM). Specifically, a guest administrator can use the BIG-IP Configuration utility to:
- Create and store FIPS keys in the HSM.
- Import non-FIPS keys (.expfiles) or FIPS keys to the HSM. Importing FIPS keys requires the BIG-IP system to use the same masking key that was previously used to export the FIPS keys.
- Convert non-FIPS keys to FIPS keys, which are then stored in the HSM.
For information about managing your FIPS keys, see the Key Management section of this guide.
Before you log in to a vCMP guest and manage private SSL keys, confirm that you have met these prerequisites:
- You have a user role that allows you to log in to the system as a vCMP guest administrator.
- You have permission to use thetmshCLI.
- You have permission to manage private SSL keys.
For more information, see
BIG-IP Digital Certificates Administration
at my.f5.com.Recovery options
You can use one of these options for recovering your
embedded FIPS system.
- Configure an additional unit for recovery
- Save the keys on a disk
- Configure a device group
FIPS system recovery options
This table describes configuration options for
FIPS system recovery.
Option |
Description |
|---|---|
Configure a device group |
Configure the F5 devices in a device
group with the FIPS HSMs synchronized. In the event of a
system failure, the standby unit becomes active and handles
incoming traffic. Contact F5 to arrange a Return Material
Authorization (RMA) for the failed device and then follow
the steps for implementing a replacement unit to recover the
failed device. |
Configure an additional unit for
recovery |
Fully configure a third unit, add it
to the security domain, and synchronize the configurations.
Remove the unit from the network and store it in a secure
location. If the F5 system in production is damaged or
destroyed, you can use the backup unit to reconstitute the
security domain. |
Save the keys on a disk |
Generate the private keys outside of the FIPS HSM.
Copy the non-FIPS protected keys to a secure external location
as a backup. Then convert the non-FIPS into FIPS keys on the
F5 system. The keys on the F5 system are now protected by the
FIPS HSM. If there is a catastrophic system failure, use the
non-FIPS protected backup keys to repopulate the FIPS HSM.
This backup
method is not FIPS compliant. |
Implement a replacement unit in a device group after a system failure
Before you recover hardware security module (HSM) information, ensure that the F5 software is configured and then install your saved UCS file on the new replacement system. For information about backup and recovery of a BIG-IP system UCS file, see
BIG-IP System: Essentials
at my.f5.com.If one unit of a device group fails, the failover unit becomes active and maintains the HSM information. After you replace the failed unit in a device group, you need to restore the HSM information on the replacement unit.
- Connect the currently active unit to the replacement unit.
- On the replacement unit, initialize the FIPS hardware security module (HSM). For information about performing this initialization, see the appropriate HSM initialization procedure for your platform.Be sure to run this FIPS HSM initialization command sequence on the replacement unit. If you run it on the currently active unit, you will lose all of your existing keys.Be sure to use the same security domain that you specified when you initially set up the currently active unit.
- On the currently active unit, copy information from the currently active unit to the replacement unit.fipscardsync peerBe sure to run this FIPS HSM initialization command from the currently active unit. If you run this command from the replacement unit, you will lose your original FIPS information.
- On the currently active unit, synchronize the full software configuration to the replacement unit usingtmsh.tmsh run config-sync to-group /Common/<device-group-name>Synchronizing the software configuration using this command sequence also synchronizes the keys stored in the HSM.
The replacement unit is now ready to function as the failover unit in a device group.
Implement a replacement standalone device after a system
failure
You must have a backup of your
non-FIPS protected keys before you can restore the hardware security module
(HSM) information on a standalone replacement device.
After you replace a failed
standalone unit, you need to restore the HSM information on the replacement
unit.
- Copy the full software configuration to the replacement unit usingtmsh.tmsh load ucs <ucs-filename>Synchronizing the configuration does not synchronize the keys stored in the HSM.
- On the replacement unit, initialize the FIPS HSM. For information about performing this initialization, see the appropriate HSM initialization procedure for your platform.
- Log in to the command line of the system using an account with root access.
- Open the TMOS Shell (tmsh).tmsh
- Convert an existing key to FIPS.install sys crypto key <key-object-name> from-local-file <key-file-path> security-type fipsThis example converts an SSL private key namedmykeyfrom a local key file stored in the/shared/tmpdirectory:install sys crypto key mykey from-local-file /shared/tmp/mykey.key security-type fips
Troubleshooting options
You can use one of these options for
troubleshooting your embedded FIPS system.
FIPS troubleshooting
You can use CLI utilities to troubleshoot common
issues with your embedded FIPS device.
- How do I check that my system includes an embedded FIPS device (FIPS card)?
- Log in to the CLI of your system and typetmsh show sys hardwareto view details about your platform. If your system includes an embedded FIPS device, it displays as type "crypto" under one of the "Hardware Version Information" sections. This is an example of how the system output might appear when you run this command:Name n3-crypto0 Type crypto Model Cavium NITROX-3 Parameters -- -- version CNN35x-MC-SSL-0022
- How do I see which embedded FIPS device is installed in my system?
- Log in to the CLI of your system and view the model of FIPS device in your platform by typingfipsdevice.Thefipsdevicecommand is available only on BIG-IP software versions 11.0 and later.
- Where does the system log messages from the embedded FIPS device?
- The Cavium device driver provides minimal logging, but you can view any log messages by logging in to the CLI of your system and typingdmesg | grep -i cavium.
- Which directories or files on my system pertain to FIPS?
- /config/ssl/ssl.key
- Contains key files on BIG-IP software versions 9.x and 10.x.
- /config/filestore/files_d/Common_d/certificate_key_d/
- Contains key files on BIG-IP software versions 11.x and later.
- /config/ssl/ssl.crt
- Contains certificate files on BIG-IP software versions 9.x and 10.x.
- /config/filestore/files_d/Common_d/certificate_d
- Contains certificate files on BIG-IP software versions 11.x and later.
- /config/ssl/ssl.cavfips
- Contains encrypted key files (.exp); used in config sync.
- /usr/bin/fipsutil
- Used to configure the embedded FIPS device.
- My alarm LED is blinking red, and I see this warning message on my LCD or in the system event log (SEL):FIPS initialization error in booted slot asserted.
- Clear the alarm using the LCD, then power cycle the system using either the AOM command menu, the LCD, or by externally power cycling the system.





