Manual Chapter :
API rate limiting: Customer ID based quota enforcement
Applies To:
Show Versions
BIG-IP APM
- 21.1.0 , 15.1.10, 15.1.9, 15.1.8, 15.1.7, 15.1.6, 15.1.5, 15.1.4, 15.1.3, 15.1.2, 15.1.1, 15.1.0
API rate limiting: Customer ID based quota enforcement
In this example of API rate limiting, each customer application gets its own
request quota. The example uses two airline applications called Southwest and Alaska. The policy
uses OAuth token validation, and branch logic is based on Client application ID using the key
ClientAppID.
Each application has a different API rate limiting agent. The Southwest
application is allowed up to 10,000 requests every 10 minutes, and Alaska allows up to 5,000
requests every 10 minutes. The API protection per-request policy checks the client application
ID, and adds the request to the quota tally for that application.
To develop this example, you need to
- Create an API protection profile that defines the paths, servers, and responses preferably using an OpenAPI spec file.
- In the API protection profile, forAuthorization, useOAuth 2.0.
- On the Rate Limiting tab of the API protection profile, use the predefined identity key calledClientAppIDin two rate limiting configurations that use different request quotas and spike arrest values for each airline.
- On the Access Control tab, clickEditto see the visual representation of the per-request policy that was created.
- In the visual policy editor, edit the policy as needed for rate limiting each application. Create API Rate Limiting agents for each application and in each agent, select the appropriate configuration and response for that airline.
Here is the example API protection per-request policy that performs
different levels of rate limiting for two airline applications.
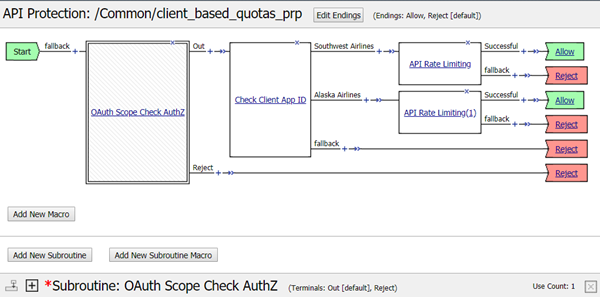
How it works
- Access Policy Manager receives an API request with an authorization header containing a JWT access token.
- The access token is extracted from the authorization header.
- For all API requests, the OAuth Scope agent in the subroutine validates the access token.
- If OAuth validation fails, the system returns an appropriate response for that API request.
- On successful validation of the JWT access token, the policy classifies the request based on the value ofClientAppIdand sends it to the appropriate branch.
- By assigning different Rate Limiting configurations in the two API Rate Limiting agents, the policy enforces different rate limiting quotas for each airline.
- If the number of requests exceeds the quota, the system returns a response to the sender of the API request, and logs an error message.





