Manual Chapter :
Adding subroutines for SAML Auth with and without MFA
Applies To:
Show Versions
BIG-IP APM
- 16.0.1, 16.0.0
Adding subroutines for SAML Auth with and without MFA
You should have a per-request policy, and SAML
authentication servers for authentication with and without MFA.
Create the subroutines to allow continuous
checks and reauthenticate with SAML and MFA when the user goes to a specific
URL.
- From the Main tab, click .
- Find the policy you want to edit, and in the Per-Request Policy column, clickEdit.
- In the per-request policy, clickAdd New Subroutine.
- Name the subroutine for use with SAML Auth and MFA. For example,APP Azure SAML Auth + MFA.
- ClickSave.
- Expand the subroutine, and click the plus to add a new item.
- Click theAuthenticationtab, selectSAML Auth, and clickAdd Item.
- Select theAAA Serverfor SAML Authentication with MFA. For example,/Common/app.example.com-azure-mfa.
- ClickSave.
- In the subroutine, clickEdit Terminals.
- ClickAdd Terminal.
- Select the red color for the new terminal, and name the unsuccessful terminal, for example,fail.You cannot name the failure terminalfallback.
- Create another subroutine for SAML Auth without MFA, name it accordingly, and for theAAA Server, select the non-MFA AAA server.Configure the terminals in the same way.
- On the MFA branch of the per-request policy, click the plus symbol.
- Click the Subroutines tab, select the SAML Auth with MFA subroutine you created, and clickAdd Item.
- On the non-MFA branch of the per-request policy, click the plus symbol.
- Click the Subroutines tab, select the SAML Auth without MFA subroutine you created, and clickAdd Item.
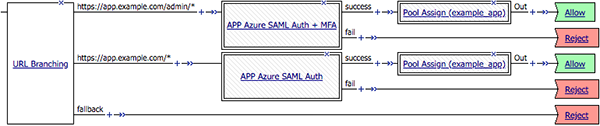
- Add any other items your per-request policy requires.This example shows a completed per-request policy with MFA and non-MFA subroutines, assigned by URL branching. A Pool Assign macro has also been added, which assigns a static pool after authentication succeeds. TheStartof the policy has been removed for image clarity.
The per-request policy is now configured.
Configure a virtual server for the application, and attach
the allow-all access policy and the authentication per-request policy.





