Manual Chapter :
Detecting DDoS Attack Impact
Applies To:
Show Versions
BIG-IQ Centralized Management
- 8.4.0, 8.3.0, 8.2.0, 8.1.0, 8.0.0
Detecting DDoS Attack Impact
Detecting the impact of DDoS attacks
The DoS profiles configured in Shared Security help prevent DoS (Denial of
Service) attacks aimed at the resources that are used for serving the application (the web
server, web framework, and the application logic). Ensure that your Network Security,
Application Security, and DNS Security are properly mitigating distributed DoS (DDoS) attacks.
The following data view is only available for managed BIG-IP devices
v13.1.0.8 or later. To view Network Firewall reports for BIG-IP devices prior to version
13.1.0.8, go to .
By isolating attacks, you can investigate whether you need to:
- Adjust the protection mode of your DoS profile (mitigating as opposed to monitoring)
- Edit or reassign a DoS profile
- Configure additional resources for your BIG-IP devices to maintain their protection services
Summary of DDoS attacks
The following details the summary information/data for
ongoing DDoS attack reported by the virtual server with a DDoS profile. To view the DDoS attack summary on your system, go to .
DDoS attack summary screen
The image displays the DDoS attack screen. The ATTACKS area, located in the summary bar, provides automatic filters to the attacks listed in the grid below the summary bar. You can use the information found in the grid to assess the status of the attack, view affected objects, or drill down into a specific attack.
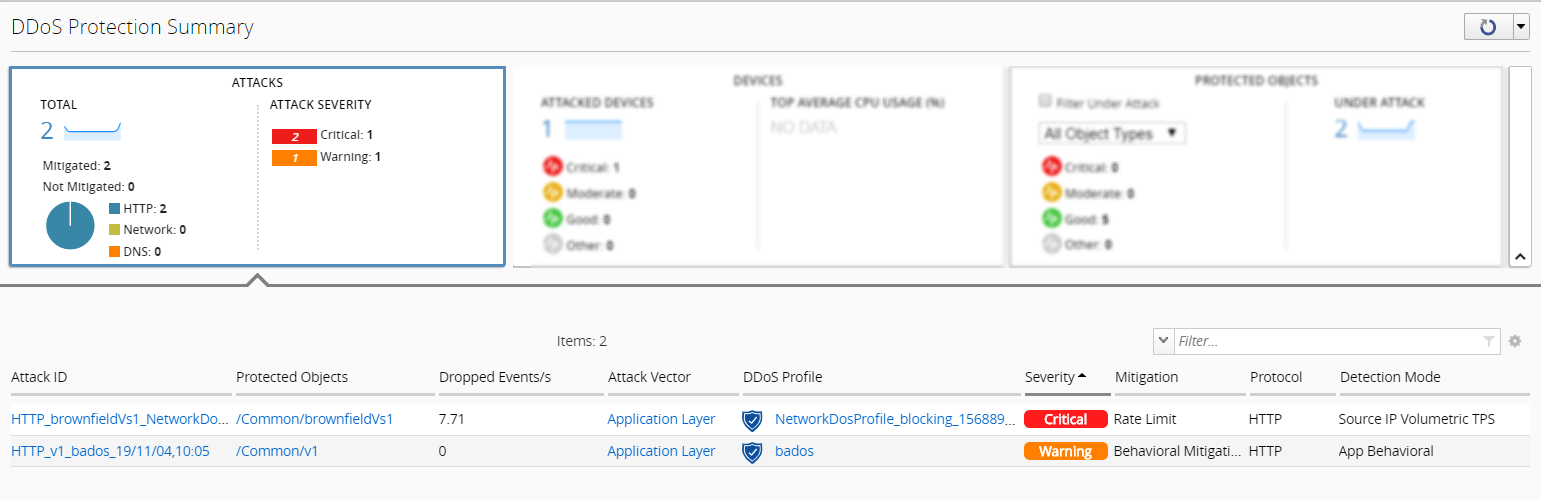
Grid Heading | Description | Link |
|---|---|---|
Attack ID | The unique identifier for the correlated (ongoing) attack event, once it was initially detected by the DDoS profile. For more information about correlated attacks, see Rules for correlated DoS attacks. | The attack's summary screen detailing additional data specific to the correlated attack. |
Protected Objects | The application or virtual server that is under DDoS attack. | Contingent on protected object type:
|
Dropped Events | The average rate of dropped packets per second. | N/A |
Attack Vector | The type of DDoS attack detected, based on configured thresholds and traffic patterns configured to the DDoS profile. | The DDoS profile configuration, based on the detecting protocol (HTTP, Network, or DNS) |
DDoS Profile | The DDoS profile that detected the attack, and the protection mode. | |
Severity | The severity assigned to the DDoS attack. For more information about severity, see DDoS attack severity. | N/A |
Mitigation | The method in which traffic is controlled to mitigate the effects of a DDoS attack. | N/A |
Protocol | The security service that detected the DDoS attack. This can also indicate the internet layer at which the object was attacked. | N/A |
Detection Mode | The threshold or traffic criteria in your DDoS profile that indicated that the protected object was under attack. | N/A |
Duration | The elapsed time of the attack since its initial detection. | N/A |
Filter ongoing DDoS attacks
Before you can display statistics and protected objects in the Protection Summary screen, you must have:
- A BIG-IQ data collection device configured for the BIG-IQ device
- The BIG-IP device located in your network and running a compatible software version
- Statistics collection enabled for managed BIG-IP devices
- AVR provisioned on your BIG-IP devices
You isolated the recent and ongoing distributed denial of service (DDoS) attacks based on the protocol and protection mode. You can use the filters on this screen to identify attacks that might impact application, network, or managing BIG-IP performance. Once you isolate an attack that impacts your system objects, you further can evaluated whether mitigation is necessary.
- Go to .
- Locate the ATTACKS area at the top left side of the screen to view a summary of all ongoing DDoS attacks.
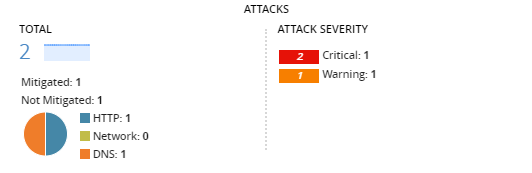
- To filter DDoS attacks by the targeted protocol, selectHTTP,Network, orDNS.The attack information that is displayed varies according to your security provisioning and the BIG-IP software version reporting the attack's data.
- To isolate attacks by severity, select one of the severity levels from ATTACK SEVERITY.
- The Warning alert. The attack's details indicate that an non-mitigated attack would have a moderate impact on your protected objects.
- The Critical alert. The attack's details indicate that a non-mitigated attack would have a critical impact on your protected objects
- To filter attacks by protection mode, specify how to view them:
- ClickMitigatedto view attacks detected by a DoS profile that is configured to mitigate or block traffic recognized at an attack.
- ClickNot Mitigatedto view attacks detected by a DoS profile that is configured to monitor traffic recognized as an attack.
Protection modes against DDoS attacks
The attack protection mode indicates whether your DoS
profile's configuration mitigates or monitors detected attacks based on the security
services provisioned on your BIG-IP devices (ASM, DNS, and AFM).
Mitigated
The DoS profile that reported the attack has at least one
mitigating element:
- HTTP protocol (Application Security): One or more operation modes is configured to Blocking.
- DNS protocol or Network protocol: One or more attack type states is configured to Mitigate.
Not Mitigated
The DoS profile that reported the attack has at least one
monitoring element, and no mitigating elements:
- HTTP protocol (Application Security): One or more operation modes is configured to Transparent.
- DNS protocol or Network protocol: One or more attack type states is configured to Detect Only or Learn Only.
DDoS attack severity
The severity assigned to the DDoS attacks displayed in the
Protection Summary screen () have either a Critical or Warning attack score. The score reflects
the recently reported correlated attack with the highest attack severity. Severity is based
on the following criteria.
Detection Mode
The attack's detection mode (trigger) influences the weight of the attack
severity.
IP Ratio
The ratio of different attacking client IP addresses, out of all client IP
addresses processed. An increased number of IP addresses attacking indicates a
broader attack distribution.
Mitigated traffic
The ratio of mitigated traffic out of all traffic processed.
Rules for correlated DoS attacks
Attacks detected from multiple BIG-IP devices may be
correlated with an ongoing attack if they meet the following criteria, per security
protocol. You can view correlated attack alerts either in the Attack Details screen
() or Alert History screen ().
HTTP
Reported HTTP attacks correlate if they share the following
characteristics:
- DoS Profile name
- Device Service Cluster (DSC) name
- Application
DNS
Reported DNS attacks correlate if they share the following
characteristics:
- DoS Profile name
- Virtual server name or Device Sync Group
- Device Service Cluster (DSC) name
Network
Reported DNS attacks correlate if they share the following
characteristics:
- DoS Profile name
- Virtual server nameA network attack on a device level correlates attacks with the virtual server nameDevice.
- Device Service Cluster (DSC) name
DDoS attack events
The BIG-IP system defines an attack by assigning an attack ID. The
shared characteristics within the DDoS attack's data can correlate different attack IDs
across a BIG-IP system environment (see Rules for correlated DoS attacks). These correlated attacks trigger events that allow you to
evaluate a single attack's overall status, severity, and system impact. Attack inactivity indicates the end of a DDoS attack, which triggers a cleared event.
Raw attack events
Raw attack events
report on the
basis of a single attack ID reported by the BIG-IP system. Any changes in a raw
attack's dimensions or severity are reflected in the raw attack events.Correlated attack events
Correlated attack events
report on the basis of the raw attack events that comprise a single correlated attack. Correlated events occur
as a result of significant modifications to an attack's state across your BIG-IP system environment. The following modifications change the correlated attack state:
- A change in the highest reported status out of the active raw attacks that comprise the correlated attack:
- Attack severity
- Attack mitigation (this also impacts the corresponding attack trigger).
- The correlated attack was detected by an additional BIG-IP blade or hostname.
- The addition or removal of a raw attack.





