Updated Date: 04/27/2026
System Settings
You can access system settings in the system controller webUI and chassis partition webUI. Each webUI provides different settings.
This table lists the available system settings in the system controller and chassis partition webUIs:
| System controller webUI | Chassis partition webUI |
|---|---|
| Alarms and Events | Alarms and Events |
| Controller Management | Cluster Details |
| System Inventory | High Availability |
| Log Settings | Log Settings |
| File Utilities | File Utilities |
| Time Settings | SNMP Configuration |
| SNMP Configuration | Configuration Backup |
| Configuration Backup | General |
| Licensing | |
| Software Install Status | |
| General |
You can view active system alarms and events in the system controller webUI and CLI.
The Alarms & Events screen is available in both the system controller and chassis partition webUIs. This screen lists the alert information for all performance and network indicators that have currently crossed a performance or health threshold. Use this screen to identify the specific object that is affected.
-
Log in to the VELOS system controller webUI or the chassis partition webUI using an account with admin access.
-
On the left, click SYSTEM SETTINGS > Alarm & Events.
-
Choose from one of these actions:
- To refresh the alarms or events list, click the Refresh icon on the right of the screen.
- To display events result by time preference, click the down arrow next to Refresh icon, select a value from the list. The default value is one hour. For example, select five minutes to display any event that occurred in the last five minutes.
- To display events by severity, select a value from the Severity list. The default value is WARNING.
Option Description Emergency Emergency system panic messages Alert Serious errors that require administrator intervention Critical Critical errors, including hardware and file system failures Error Non-critical, but possibly important, error messages Warning Warning messages that should be logged and reviewed Notice Messages that contain useful information, but might be ignored Informational Messages that contain useful information, but might be ignored Debug Detailed messages used for troubleshooting
You can view information about active system alarm conditions from the system controller CLI.
-
Connect using SSH to the system controller floating management IP address.
-
Log in to the command line interface (CLI) of the system controller using an account with admin access.
When you log in to the system, you are in user (operational) mode.
-
View a list of active system alarm conditions.
show system alarms | tabThis example shows a power supply unit (PSU) redundancy fault:
syscon-1-active# show system alarms ID RESOURCE SEVERITY TEXT TIME CREATED –––––––––––––––––––––––––––––––––––––––––––––––––––––––––––––––––––––––––––––––––––––––––––––––––––––––––––––––- 65796 psu-controller WARNING PSU redundancy fault detected 2021-07-01-11:11:11.992270499 UTC 65793 psu-2 ERROR PSU fault detected 2021-07-01-11:11:11.999825828 UTC
You can configure system controller high availability (HA) from Controller Management screen on the system controller webUI. The system controllers work together as a redundant pair. The default mode for system controller HA is Auto, which automatically selects the system controller that is best suited at the time as the active controller and fails over only as needed.
The High Availability screen on the chassis partition webUI includes options for configuring chassis partition HA. High availability is already implemented for chassis partitions on the VELOS system.
You should not need to change system controller high availability (HA) to something other than the default configuration (Auto), but you can opt to change the configuration or initiate a failover from the active controller to the standby from the system controller webUI.
-
Log in to the VELOS system controller webUI using an account with admin access.
-
On the left, click SYSTEM SETTINGS > Controller Management.
-
For the Preferred Node field, select System Controller 1 or System Controller 2 to act as an active system controller, or choose Auto (recommended).
Note: Changing the Preferred Node configuration creates a failover event and ends the session if you select the system controller that is currently acting as the standby. Wait 30 seconds and then start a new session with either the floating IP address or the active system controller IP address after the change has completed.
Hardware health conditions of the system controllers always take precedence. If one of the system controllers is not healthy, the chassis partition will ignore the preference and synchronize with the healthy system controller.
-
To force a failover to occur immediately, click Failover.
Note: The Failover button is available only when Preferred Node field is set to Auto.
You would do this only if you want the current standby system controller to become the active system controller.
You can change the preferred system controller high availability (HA) mode from either the system controller or chassis partition CLI.
-
Connect using SSH to the system controller floating management IP address or chassis partition management IP address.
-
Log in to the command line interface (CLI) of the system controller or chassis partition using an account with admin access.
When you log in to the system, you are in user (operational) mode.
-
Change to config mode.
configThe CLI prompt changes to include
(config). -
Change system controller high availability/redundancy to a specified mode.
system redundancy config mode [ auto | prefer-1 | prefer-2 }These redundancy modes are available:
Option Description auto System chooses preferred mode automatically. This is the default value. prefer-1 Prefer controller-1 to be active. prefer-2 Prefer controller-2 to be active. This example shows configuring controller-1 as the preferred active system controller from the system controller CLI:
syscon-1-active(config)# system redundancy config mode prefer-1 -
Commit the configuration changes.
commit
You can access settings for hardening the security of your system in the system controller or chassis partition webUI.
An allow list enables you to specify either specific IPv4 or IPv6 addresses, ports, or a netmask as an accepted source that can access the system.
When the IP address is configured and saved to the system allow list, only traffic coming from that IP address and port is accepted by the system’s management interface. You can also edit or delete entries in the allow list after you have configured them.
You can configure the system allow list from either the system controller or chassis partition webUI. To edit an existing allow list entry, select the IP address that you want to edit. You cannot change the designated name, but you can change all other fields.
-
Log in to the VELOS system controller webUI or the chassis partition webUI using an account with admin access.
-
On the left, click SYSTEM SETTINGS > System Security.
-
In the Allowed IP Addresses area, click Add to add an IP address to the allow list.
-
For Name, enter a descriptive name for the IP address.
-
For IPv4/IPv6, select IPv4 or IPv6.
-
For Address, enter the IP address to be added to the allow list.
-
For Prefix Length, enter or select the prefix length.
The prefix length values must be between 1 and 32 for IPv4 and between 1 and 128 for IPv6.
-
For Port, select a port number for the IP address.
Available options are:
- 443 (HTTPS): Allow only HTTP with SSL traffic on this IP address.
- 80 (HTTP): Allow only HTTP traffic on this IP address.
- 8888 (RESTCONF): Allow only RESTCONF traffic on this IP address.
- 161 (SNMP): Allow only SNMP traffic on this IP address.
- 7001 (VCONSOLE): Allow only VCONSOLE traffic on this IP address.
- 22 (SSH): Allow only SSH traffic on this IP address.
-
Click Save & Close.
You can configure the system allow list from either the system controller or chassis partition CLI.
-
Log in to the command line interface (CLI) of the system controller or chassis partition using an account with admin access.
When you log in to the system, you are in user (operational) mode.
-
Change to config mode.
configThe CLI prompt changes to include
(config). -
Configure the system to allow traffic only from specified IP addresses.
Note: This is applicable only for ports 22, 161, 8888, 443, 80, and 7001.
system allowed-ips allowed-ip <*allowlist-profile-name*> config [ ipv4 | ipv6 ] address <*ip-address*> port <*port-number*>prefix-length <*subnet-prefix-length*>This example adds a specified IPv4 address to the system allow list:
syscon-1-active(config)# system allowed-ips allowed-ip test config ipv4 address 192.0.2.33 port 161 prefix-length 32This example adds a netmask to the system allow list:
syscon-1-active(config)# system allowed-ips allowed-ip test config ipv4 address 12.13.14.0 port 161 prefix-length 24 -
Commit the configuration changes.
commit
You can run the system in appliance mode. Appliance mode adds a layer of security removing user access to Root and Bash. Enabling appliance mode disables all Root and Bash shell access for the system.
You can enable appliance mode at each of these levels:
- System
- Tenant
Appliance mode is disabled at all levels, by default. You can enable it from the webUI or the CLI. The appliance mode option for the system is available to users with admin access under SYSTEM SETTINGS > General in the webUI. For tenants, it is available in the webUI under TENANT MANAGEMENT > Tenant Deployments.
These are the effects of enabling appliance mode at each of the different levels.
System-level appliance mode
- Root or Bash access is disabled on the system.
- Console access: Root or Bash access is disabled on the system. Users can log in to the system CLI from the console using an admin account.
Tenant appliance mode
- Root access to the tenant is disabled by all means. Bash access is disabled for users (with a terminal shell flag enabled) inside the tenant.
- Users can access the tenant only through the webUI or the CLI.
- Tenant console access: Users can log in to the CLI from the virtual console using an admin account (with a terminal shell flag enabled).
You can enable appliance mode if you want to disable all root and Bash shell access.
Note: For greater security, it is highly recommended that you configure the system controllers and chassis partitions to run in appliance mode.
From the system controller webUI, appliance mode disables root and Bash access to the controllers. From the chassis partition webUI, appliance mode limits access to the specific chassis partition to which you are connected. You can enable or disable the appliance mode for system controllers and partitions from their respective webUIs.
Note: The appliance mode option for tenants is available in the chassis partition webUI under TENANT MANAGEMENT > Tenant Deployments.
-
Log in to the VELOS system controller webUI or the chassis partition webUI using an account with admin access.
-
On the left, click SYSTEM SETTINGS > System Security.
-
For Appliance Mode, in the Appliance Mode area, for Enable/Disable, select either Enabled or Disabled.
The default value is Disabled.
-
Click Save.
You can configure appliance mode from either the system controller or chassis partition CLI if you want to disable all root and Bash shell access.
Note: For greater security, it is highly recommended that you configure the system controllers and chassis partitions to run in appliance mode.
From the system controller CLI, appliance mode disables root and Bash access to the controllers. From the chassis partition CLI, appliance mode limits access to the specific chassis partition to which you are connected.
Note: The appliance mode option for tenants is available in the chassis partition CLI using the tenants tenant <*tenant-name*> config appliance-mode command sequence.
-
Connect using SSH to the system controller floating management IP address or chassis partition management IP address.
-
Log in to the command line interface (CLI) of the system controller or chassis partition using an account with admin access.
When you log in to the system, you are in user (operational) mode.
-
Change to config mode.
configThe CLI prompt changes to include
(config). -
Enable appliance mode.
system appliance-mode config [ disabled | enabled ]In this example, you enable appliance mode on the system controllers:
syscon-1-active(config)# system appliance-mode config enabled -
Commit the configuration changes.
commit
Cryptographic agility on F5 VELOS systems enables you to replace cryptographic implementations for the httpd and sshd services. This applies to the F5OS management interface.
You can configure the sshd service from either the system controller or chassis partition CLI.
-
Connect using SSH to the system controller floating management IP address or chassis partition management IP address.
-
Log in to the command line interface (CLI) of the system controller or chassis partition using an account with admin access.
When you log in to the system, you are in user (operational) mode.
-
Change to config mode.
configThe CLI prompt changes to include
(config). -
Configure the sshd service.
system security services service sshd config ciphers [ <*string*> ] kexalgorithms [ <*string*> ] macs [ <*string*> ]These are the available configuration options:
|
Option |
Description |
|---|---|
|
ciphers |
User-specified ciphers. For example, aes128-cbc or aes128-ctr.The cipher string can take several additional forms. It can consist of a single cipher suite or a list of cipher suites containing a certain algorithm, or cipher suites of a certain type. You can combine lists of cipher suites into a single cipher string using the + character as a logical AND operation. |
|
kexalgorithms |
User-specified key exchange algorithms. For example, diffie-hellman-group14-sha1 or diffie-hellman-group14-sha256.You can combine lists of KEX algorithms into a single string using the + character as a logical AND operation. |
|
macs |
User-specified MAC algorithms. For example, hmac-sha2-512 or AEAD_AES_128_GCM.You can combine lists of MAC algorithms into a single string using the + character as a logical AND operation. |
This example shows configuring the sshd service:
```
syscon-1-active(config)# system security services service ssh config ciphers [ aes128-ctr aes256-cbc ]
kexalgorithms [ ecdh-sha2-nistp521 echd-sha2-nistp384 ] macs [ hmac-sha1 ]
```
-
Commit the configuration changes.
commit
After you commit the change, you are prompted to confirm the change. The service will then restart.
You can configure the SSL cipher suites used for the httpd service from either the system controller or chassis partition CLI.
-
Connect using SSH to the system controller floating management IP address or chassis partition management IP address.
-
Log in to the command line interface (CLI) of the system controller or chassis partition using an account with admin access.
When you log in to the system, you are in user (operational) mode.
-
Change to config mode.
configThe CLI prompt changes to include
(config). -
Configure one or more cipher suites for the httpd service.
system security services service httpd config ssl-ciphersuite <*string*>In this example, you indicate that the system uses only the specified cipher suite:
syscon-1-active(config)# system security services service httpd config ssl-ciphersuite ECDHE-RSA-AES256-GCM-SHA384In this example, you specify more than one cipher suite by separating the cipher suite names with a colon:
syscon-1-active(config)# system security services service httpd config ssl-ciphersuite ECDHE-RSA-AES128-SHA:ECDHE-RSA-AES256-SHA -
Commit the configuration changes.
commit
After you commit the change, you are prompted to confirm the change. The service will then restart.
When you configure ciphers for httpd, you can use multiple formats. You can specify a single cipher suite, such as RC4-SHA. You can also represent a list of cipher suites containing a certain algorithm or cipher suites of a certain type using a shortened name. For example, SHA1 represents all cipher suites using the digest algorithm SHA1, and SSLv3 represents all SSLv3 algorithms. You can combine lists of cipher suites into a single cipher string using the + character as a logical AND operation. For example, SHA1+DES represents all cipher suites containing the SHA1 and DES algorithms.
These are the allowed SSL cipher suites for general appliances:
- ECDHE-RSA-AES256-GCM-SHA384
- ECDHE-ECDSA-AES256-GCM-SHA384
- ECDHE-RSA-AES256-SHA384
- ECDHE-ECDSA-AES256-SHA384
- ECDHE-RSA-AES256-SHA
- ECDHE-ECDSA-AES256-SHA
- DHE-DSS-AES256-GCM-SHA384
- DHE-RSA-AES256-GCM-SHA384
- DHE-RSA-AES256-SHA256
- DHE-DSS-AES256-SHA256
- DHE-RSA-AES256-SHA
- DHE-DSS-AES256-SHA
- DHE-RSA-CAMELLIA256-SHA
- DHE-DSS-CAMELLIA256-SHA
- ECDH-RSA-AES256-GCM-SHA384
- ECDH-ECDSA-AES256-GCM-SHA384
- ECDH-RSA-AES256-SHA384
- ECDH-ECDSA-AES256-SHA384
- ECDH-RSA-AES256-SHA
- ECDH-ECDSA-AES256-SHA
- AES256-GCM-SHA384
- AES256-SHA256
- AES256-SHA
- CAMELLIA256-SHA
- PSK-AES256-CBC-SHA
- ECDHE-RSA-AES128-GCM-SHA256
- ECDHE-ECDSA-AES128-GCM-SHA256
- ECDHE-RSA-AES128-SHA256
- ECDHE-ECDSA-AES128-SHA256
- ECDHE-RSA-AES128-SHA
- ECDHE-ECDSA-AES128-SHA
- DHE-DSS-AES128-GCM-SHA256
- DHE-RSA-AES128-GCM-SHA256
- DHE-RSA-AES128-SHA256
- DHE-DSS-AES128-SHA256
- DHE-RSA-AES128-SHA
- DHE-DSS-AES128-SHA
- DHE-RSA-CAMELLIA128-SHA
- DHE-DSS-CAMELLIA128-SHA
- ECDH-RSA-AES128-GCM-SHA256
- ECDH-ECDSA-AES128-GCM-SHA256
- ECDH-RSA-AES128-SHA256
- ECDH-ECDSA-AES128-SHA256
- ECDH-RSA-AES128-SHA
- ECDH-ECDSA-AES128-SHA
- AES128-GCM-SHA256
- AES128-SHA256
- AES128-SHA
- CAMELLIA128-SHA
- PSK-AES128-CBC-SHA
These are the allowed SSL cipher suites for systems that have a FIPS software license applied. It does not apply to the F5 r5900-DF or r10900-DF platforms that have an embedded FIPS hardware security module (HSM).
- ECDHE-RSA-AES128-GCM-SHA256
- ECDHE-RSA-AES256-GCM-SHA384
- ECDHE-RSA-AES128-SHA
- ECDHE-RSA-AES256-SHA
- ECDHE-RSA-AES128-SHA256
- ECDHE-RSA-AES256-SHA384
- ECDHE-ECDSA-AES128-GCM-SHA256
- ECDHE-ECDSA-AES256-GCM-SHA384
- ECDHE-ECDSA-AES128-SHA
- ECDHE-ECDSA-AES256-SHA
- ECDHE-ECDSA-AES128-SHA256
- ECDHE-ECDSA-AES256-SHA384
When you configure ciphers for sshd, you enclose the cipher string in square brackets and include more than one by separating them with a space. These ciphers are allowed on the system.
- ecdh-sha2-nistp256
- ecdh-sha2-nistp384
- ecdh-sha2-nistp521
- diffie-hellman-group16-sha512
- diffie-hellman-group14-sha256
- diffie-hellman-group14-sha1
- aes128-ctr
- aes256-ctr
- aes128-gcm@openssh.com
- aes256-gcm@openssh.com
- aes128-cbc
- aes256-cbc
- umac-64-etm@openssh.com
- umac-128-etm@openssh.com
- hmac-sha2-256-etm@openssh.com
- hmac-sha1-512-etm@openssh.com
- hmac-sha1-etm@openssh.com
- umac-64@openssh.com
- umac-128@openssh.com
- hmac-sha2-256
- hmac-sha2-512
- hmac-sha1
For security purposes, you can configure how long management sessions can remain idle before you are logged out of the system. If you are connected using an SSH connection, the system closes the SSH connection after this time expires.
You can configure how long management sessions can remain idle before you are logged out of the system from either the system controller or chassis partition webUI. If you are connected using an SSH connection, the system closes the SSH connection after this time expires.
-
Log in to the VELOS system controller webUI or the chassis partition webUI using an account with admin access.
-
On the left, click SYSTEM SETTINGS > System Security.
-
In the Services area, for CLI Idle Timeout, enter a time, in seconds, for how long management sessions can remain idle before they time out.
A value of 0 (zero) sets the time to infinity, so the user is never logged out. The timeout can be a value from 0 through 8192 seconds. The default value is 1800 seconds (30 minutes).
-
Click Save.
You can configure how long management sessions can remain idle before you are logged out of the system from the from either the system controller or chassis partition CLI. If you are connected using an SSH connection, the system closes the SSH connection after this time expires. You can also configure how long the system is inactive for a root user before the user is logged out of the system.
-
Connect using SSH to the system controller floating management IP address or chassis partition management IP address.
-
Log in to the command line interface (CLI) of the system controller or chassis partition using an account with admin access.
When you log in to the system, you are in user (operational) mode.
-
Configure the CLI system idle timeout setting for an admin user connected to the system.
system settings config idle-timeout <*time-in-seconds*>A value of 0 (zero) sets the time to infinity, so the user is never logged out. The timeout can be a value from 0 through 8192 seconds. The default value is 1800 seconds (30 minutes).
This example sets an idle timeout of 3600 seconds (one hour):
syscon-1-active(config)# system settings config idle-timeout 3600 -
Configure the SSH system idle timeout setting for a root user.
system settings config sshd-idle-timeout <*time-in-seconds*>A value of 0 (zero) sets the time to infinity, so the user is never logged out. The timeout can be a value from 0 through 8192 seconds. The default value is 0 (zero).
This example sets an SSH system idle timeout of 3600 seconds (one hour):
syscon-1-active(config)# system settings config sshd-idle-timeout 3600 -
Commit the configuration changes.
commit
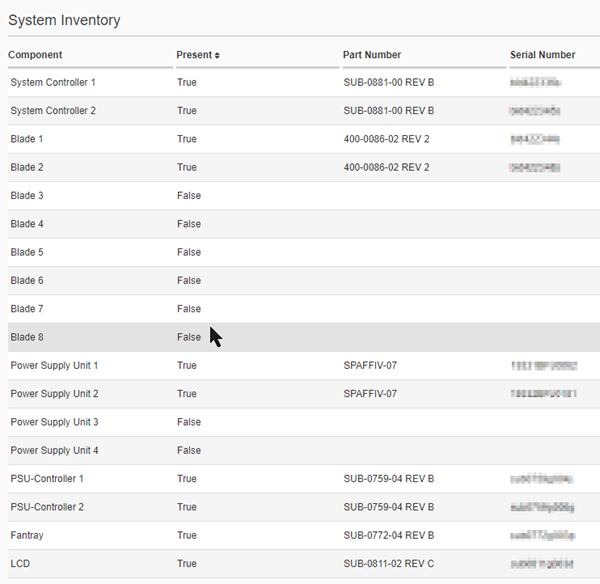
The System Inventory screen on the system controller webUI enables you to see an inventory of all components on the VELOS system, including the system controllers, blades, power supply units (PSU), PSU controller, fan tray, and LCD. The inventory includes the component name, status, part number, and serial number.
You can view an inventory of all of the system components on the VELOS system, including the system controllers, blades, power supply units (PSU), PSU controller, fan tray, and LCD from the system controller webUI. The inventory includes the component name, status, part number, and serial number.
-
Log in to the VELOS system controller webUI using an account with admin access.
-
On the left, click SYSTEM SETTINGS > System Inventory.
The system inventory displays, and you can review the information about the components on the VELOS system. An example is shown here.
You can view an inventory of all of the system components on the VELOS system, including the system controllers, blades, power supply units (PSU), PSU controller, fan tray, and LCD from the system controller CLI. The inventory includes the component name, status, part number, and serial number.
-
Connect using SSH to the system controller floating management IP address.
-
Log in to the command line interface (CLI) of the system controller using an account with admin access.
When you log in to the system, you are in user (operational) mode.
-
View information about system components.
Add a specific component to show information only about that component or omit it to show information about all components.
show components component [ <*specific-component*> ]In this example, you view details only about the system storage:
syscon-1-active# show components component storage components component controller-1 storage state disks disk nvme0n1 state model "SAMSUNG MZ1LB960HAJQ-00007" state vendor Samsung state version EDA7602Q state serial-no S123NA0NA04567 state size 894.00GB state type nvme storage state disks disk sda state model DataTraveler state vendor Kingston state version 3.0 state serial-no 0000000005?? state size 28.00GB state type usb components component controller-2 storage state disks disk nvme0n1 state model "SAMSUNG MZ1LB960HAJQ-00007" state vendor Samsung state version EDA7602Q state serial-no S123NA0NA45678 state size 894.00GB state type nvme storage state disks disk sda state model DataTraveler state vendor Kingston state version 3.0 state serial-no 000000000123 state size 28.00GB state type usb
The system controller and chassis partition webUIs include options for configuring remote log servers and the log severity level for individual software components and services.
From the webUIs you can generate a system report, or QKView file, to collect configuration and diagnostic information from the VELOS system if you have any concerns about your system operation. The QKView file contains machine-readable (JSON) diagnostic data and combines the data into a single compressed tar.gz format file. You can upload the QKView file to F5 iHealth where you can get help to verify proper operation of the system and get help with troubleshooting and understanding any issues you might be having and ensure that the system is operating at its maximum efficiency.
You can view event logs and configure secure remote logging from the CLI. You can also send host log files, which are in the /var/log directory, as well as audit.log files to the remote server from the CLI.
You can add and display information about configured remote log servers from either the system controller or chassis partition webUIs. You can also change the log severity level for individual software components and services.
-
Log in to the VELOS system controller webUI or the chassis partition webUI using an account with admin access.
-
On the left, click SYSTEM SETTINGS > Log Settings.
-
To add access to a Remote Log Server, click Add.
-
In the Server field, enter the IPv4 address, IPv6 address, or fully qualified domain name (FQDN) of the remote server. After the remote log server is saved, you cannot modify the server address.
-
In the Port field, enter the port number of the remote server.
The default port value is 514.
-
For Protocol, select UDP or TCP to choose between TCP or UDP input. When the TCP protocol is selected, the Authentication field displays.
-
From the Facility list, select LOCAL0.
F5OS supports only the LOCAL0 logging facility. All logs are directed to this facility, and it is the only one that you can use for remote logging.
-
From the Severity list, select the severity level of the messages to log.
Option Description Emergency Emergency system panic messages Alert Serious errors that require administrator intervention Critical Critical errors, including hardware and file system failures Error Non-critical, but possibly important, error messages Warning Warning messages that should be logged and reviewed Notice Messages that contain useful information, but might be ignored Informational Messages that contain useful information, but might be ignored Debug Detailed messages used for troubleshooting -
For Authentication, select the enable or disable option from the list. The default value is Disabled. This option is visible when the TCP protocol is selected while configuring the remote log server. If the UDP protocol is selected, the authentication value is saved as N/A.
-
Click Save & Close.
-
To delete a remote log server, select the server and click Delete.
-
To view the Host Log Settings, click Show.
-
For Host Log Forwarding, select the enable or disable radio button for remote forwarding. The default value is Disabled. When host log forwarding is enabled, the Include Standby Controller field displays.
-
System Controller webUI: For Include Standby Controller, select true or false from the list to include the standby controllers and send the host log files to the active controller. The default value is False. This option is visible when the Host Log Forwarding option is enabled at the chassis level.
-
Chassis Partition webUI: For Include Blades, select one or more blades from the list. This option is visible when the Host Log Forwarding option is enabled at the chassis partition level.
-
For Selectors, select the required facility and severity options from the list. To add more selectors, click the add + icon. To remove the existing selectors, click the remove (X) icon.
-
To add the required host log files to the Selected Files panel, at the chassis level, click the required host log files checkboxes.
At the chassis partition level, you can only view the already selected and locked host files.
The Selected Files option allows the host logs files to be forwarded from the directory and subdirectories.
-
For Custom Log File, enter the log file in the text box and click Add to manually add host log file names to the Selected Files panel.
-
For TLS Certificate & Key, click Show. It displays TLS Certificate and TLS Key options. If the authentication value is set as enabled for any of the remote log servers, you cannot be able to clear the TLS configuration fields.
-
For CA Bundles, click Add to enter the name and TLS CA certificate. When any of the remote server authentication is enabled, you cannot delete the CA bundle.
-
On the Log Settings screen, review the software component log levels for individual software components and adjust them as needed. Click Save if you made changes.
The log levels determine at what level events (and all higher levels) are logged for each service. Informational is the default so all except debug-level events are logged.
-
Click Save to save the log settings.
The system logs events to the velos.log file located in the /var/log_controller directory. To list files and view the contents of log files, you use the file command from either the system controller or chassis partition CLI.
-
Connect using SSH to the system controller floating management IP address or chassis partition management IP address.
-
Log in to the command line interface (CLI) of the system controller or chassis partition using an account with admin access.
When you log in to the system, you are in user (operational) mode.
-
List all files in the log directory.
file list path [ log/confd/ | log/controller/ | log/host/ }This example shows an excerpt of the contents of the
log/controller/directory:syscon-1-active# file list path log/controller/ entries { name afu-cookie date Wed Jun 15 19:52:37 UTC 2022 size 33B } entries { name cc-confd date Wed Jun 15 20:25:49 UTC 2022 size 581KB } entries { name cc-confd-hal date Wed Jun 15 19:52:10 UTC 2022 size 0B } ... -
Show the contents of a log file.
file show [ log/confd/<*filename*> | log/controller/<*filename*> | log/host/<*filename*> ]This example shows the contents of the
log/controller/velos.logfile and uses themoreoption to paginate the output:syscon-1-active# file show log/controller/velos.log | more 2022-04-21T08:18:28-07:00 localhost.localdomain notice boot_marker: ---===[ BOOT-MARKER ]===--- 2022-04-21T08:19:39-07:00 controller-1.chassis.local notice boot_marker: ---===[ BOOT-MARKER ]===--- 2022-04-21T15:27:39.925830+00:00 controller-1 alert-service[8]: priority="Notice" version=1.0 msgid=0x2201000000000001 msg="Alert Service Starting..." version="3.10.2" date="Fri Apr 8 09:42:10 2022". 2022-04-21T15:27:39.926245+00:00 controller-1 alert-service[8]: priority="Info" version=1.0 msgid=0x6602000000000005 msg="DB is not ready". 2022-04-21T15:27:39.926264+00:00 controller-1 snmp-trapd[9]: priority="Notice" version=1.0 msgid=0x2101000000000007 msg="SNMP Trap Service Starting..." version="3.2.3" date="Fri Apr 8 09:43:28 2022". 2022-04-21T15:27:39.926274+00:00 controller-1 alert-service[8]: priority="Info" version=1.0 msgid=0x6602000000000005 msg="DB is not ready". -
Show only the most recent entries in a log file.
file tail [ log/confd/<*filename*> | log/controller/<*filename*> | log/host/<*filename*> }This example shows the last ten lines of the
velos.logfile and uses the-foption to append output as the file grows:syscon-1-active# file tail -f log/controller/velos.log 2022-06-16T23:24:36.170220+00:00 controller-1 switchd[8]: priority="Notice" version=1.0 container="VCC-SWITCHD" msgid=0x1001000000000485 msg="Linkstatus change" PORT="1/mgmt0" LINKSTAT="DOWN". 2022-06-16T23:24:36.176481+00:00 controller-1 vcc-lacpd[82]: priority="Info" version=1.0 msgid=0x330100000000004e msg="" info_str="check_if_op_modify(): new oc_if_oper_status: 2 (1:UP 2:DOWN ... )". 2022-06-16T23:24:36.176820+00:00 controller-1 vcc-lacpd[82]: priority="Info" version=1.0 msgid=0x330100000000004e msg="" info_str="check_if_op_modify(): new oc_eth_port_speed: ns: 1857063266 id: 1980508219 ". 2022-06-16T23:24:36.267589+00:00 controller-1 switchd[8]: priority="Notice" version=1.0 container="VCC-SWITCHD" msgid=0x1001000000000485 msg="Linkstatus change" PORT="1/mgmt0" LINKSTAT="DOWN". 2022-06-16T23:24:36.425971+00:00 controller-1 vcc-lacpd[82]: priority="Info" version=1.0 msgid=0x330100000000004e msg="" info_str="CCLacpdWriteHdlr::delete_member(memberName=1/mgmt0) from ConfD". 2022-06-16T23:24:36.434091+00:00 controller-1 vcc-lacpd[82]: priority="Info" version=1.0 msgid=0x330100000000004e msg="" info_str="InterfaceCmObj::modifyOp: if_name=1/mgmt0 mode=FULL DUPLEX status=DOWN speed=10000#012". 2022-06-16T23:24:36.434371+00:00 controller-1 vcc-lacpd[82]: priority="Info" version=1.0 msgid=0x330100000000004e msg="" info_str="InterfaceCmObj::modifyOp: if_name=1/mgmt0 mode=FULL DUPLEX status=DOWN speed=0#012". 2022-06-16T23:25:09.324530+00:00 controller-1 platform-hal[8]: priority="Info" msg="NEBS is assumed to be true as chassis SEEPROM NEBS option couldn't be read" interface="job-2648493" apogeeUuid="a519fa20-ece4-11ec-a487-024264410634" $parent.jobId=0 $parent.apogeeUuid="a519fa20-ece4-11ec-a487-024264410634" $parent.treeUuid="90151e75-edcb-11ec-a487-024264410634" $parent.appKey="hal" actionKey="GET:chassis/nebs-capable" jobId=2648493 jobTreeUuid="90151e75-edcb-11ec-a487-024264410634" 2022-06-16T23:25:09.399391+00:00 controller-1 platform-hal[8]: priority="Info" msg="NEBS is assumed to be true as platform SEEPROM NEBS option couldn't be read" interface="job-2648493" actionKey="GET:chassis/nebs-capable" jobId=2648493 jobTreeUuid="90151e75-edcb-11ec-a487-024264410634" apogeeUuid="a519fa20-ece4-11ec-a487-024264410634" $parent.jobId=0 $parent.apogeeUuid="a519fa20-ece4-11ec-a487-024264410634" $parent.treeUuid="90151e75-edcb-11ec-a487-024264410634" $parent.appKey="hal" 2022-06-16T23:25:09.429431+00:00 controller-1 platform-hal[8]: priority="Info" msg="NEBS is assumed to be true as platform SEEPROM NEBS option couldn't be read" interface="job-2648493" actionKey="GET:chassis/nebs-capable" jobId=2648493 jobTreeUuid="90151e75-edcb-11ec-a487-024264410634" apogeeUuid="a519fa20-ece4-11ec-a487-024264410634" $parent.jobId=0 $parent.apogeeUuid="a519fa20-ece4-11ec-a487-024264410634" $parent.treeUuid="90151e75-edcb-11ec-a487-024264410634" $parent.appKey="hal" _
The system logs events to the velos.log file located in the /var/log_controller directory. To list files and view the contents of log files, you use the file command from the CLI.
-
Connect using SSH to the system controller floating management IP address or chassis partition management IP address.
-
Log in to the command line interface (CLI) of the system controller using an account with admin access.
When you log in to the system, you are in user (operational) mode.
-
Change to config mode.
configThe CLI prompt changes to include
(config). -
Configure secure remote logging. The default value is disabled.
system logging remote-servers remote-server <*name*> config proto <*proto*> remote-port <*port*> authentication { disabled | enabled }This example enables secure remote logging:
syscon-1-active(config)# system logging remote-servers remote-server test config proto test2 remote-port 80 authentication enabled -
Add authentication details for secure remote logging.
system logging remote-servers remote-server <*server-IP*> config authentication -
Add certificate or key details for secure remote logging.
system logging tls { certificate | key } <*string*> -
Add CA bundle details for secure remote logging.
system logging tls ca-bundles ca-bundle <*name*> config name <*name*> content <*ca-cert-contents*>Note: The certificate bundle that you specify must include the certificate chain of the certificate authority.
-
Remove authentication details from secure remote logging.
no system logging remote-servers remote-server <*server-IP*> config authentication -
Remove certificate or key details from secure remote logging.
no system logging tls { certificate | key } <*string*> -
Remove CA bundle details from secure remote logging.
no system logging tls ca-bundles ca-bundle -
Send log files to the remote server.
You can send host log files, which are in the /var/log directory, or audit.log files to the remote server
system logging host-logs config files file <file-name>
-
Commit the configuration changes.
commit -
Return to user (operational) mode.
end -
Show authentication, certificate, key, and CA bundle details.
show running-config system logging tls { certificate | key | ca-bundles } <*string*>
You can use File Utilities to import, export, download, or delete files asynchronously depending on which directory you select to work in. All file transfers are done using the HTTPS protocol.
You can import a file from an external server into the system controller or chassis partition from either the webUI or the CLI. HTTPS is the supported protocol. The remote host should be an HTTPS server with PUT/POST enabled and have a valid CA-signed certificate.
Note: If you want to import the contents of a tar file, you need to extract the contents first before you can import them onto the F5 system.
You can import files into these directories on a system controller :
- images/staging
- configs
You can import files into these directories on a chassis partition:
- configs
- images/import
- images/staging
- images/tenant
You can export a file from a system controller or chassis partition to an external server from either the webUI or the CLI. HTTPS is the supported protocol. The remote host should be an HTTPS server with PUT/POST enabled and have a valid CA-signed certificate.
You can export files in these directories from a system controller:
- configs
- log/confd
- log/controller
- log/host
- diags/core
- diags/crash
- diags/shared
- images/import
- images/staging
You can export files in these directories from the chassis partition:
- configs
- diags/core
- diags/shared
- images
- log
You can download files in these directories from a system controller to your local workstation from the webUI:
- configs
- diags/core
- diags/crash
- diags/shared
- log/confd
- log/controller
You can download files in these directories from a chassis partition to your local workstation from the webUI:
- configs
- diags/core
- diags/shared
- log
You can upload files in these directories from your local workstation to a system controller from the webUI:
- configs
- images/staging
You can upload files in these directories from your local workstation to a chassis partition from the webUI:
- configs
- images
You can delete files (to which you have file permissions) on a system controller or a chassis partition only from the diags/shared or configs directories from either the webUI or the CLI.
File Utilities are available in both the system controller and chassis partition webUIs. You can use File Utilities to import, export, download, upload, or delete files asynchronously depending on which directory you select to work in. All file transfers are done using the HTTPS protocol.
-
Log in to the VELOS system controller webUI or the chassis partition webUI using an account with admin access.
-
On the left, click SYSTEM SETTINGS > File Utilities.
-
From the Base Directory list, browse the directories and click subfolders to view their contents and the commands that are available from each one.
From a subfolder, click the left arrow next to the path to navigate back to the main folder.
-
To import a file, click Import.
-
In the popup, enter the URL of the file to import.
-
Provide the Username and Password only if required by the remote host.
-
Select Ignore Certificate Warnings if you want to skip warnings when importing files (such as if the remote host does not have a valid CA-signed certificate).
-
Click Import File to begin the import.
-
-
To export a file, select the file and click Export.
-
In the popup, enter the Server URL for where to export the file.
-
Provide the Username and Password only if required by the remote host.
-
Select Ignore Certificate Warnings if you want to skip warnings when importing files.
-
Click Export File to begin the export.
-
-
To upload or download a file:
-
Select the file and click Upload or Download.
The selected file will be uploaded or downloaded.
-
-
To delete a file, select the file and click Delete.
On the system controller and chassis partition, you can delete files from
diags/shared.
You can view the status of a file transfer operation to view its progress and see if it was successful. If an operation fails, hover over the warning icon to see the error that occurred.
Note: A runtime error displays in the File Transfer status area, if an invalid operation is performed.
MIB files can be managed from the File Utilities page in both the system controller and chassis partition webUIs. You can use File Utilities to export or download MIB files. File transfers are done using the HTTPS protocol.
-
Log in to the VELOS system controller webUI or the chassis partition webUI using an account with admin access.
-
On the left, click SYSTEM SETTINGS > File Utilities.
-
From the Base Directory list, select mibs.
-
To export a MIB file, select the file and click Export.
-
In the popup, enter the Server URL for where to export the file.
-
Provide the Username and Password only if required by the remote host.
-
Select Ignore Certificate Warnings if you want to skip warnings when importing files.
-
Click Export File to begin the export.
-
-
To download a file:
-
Select the file and click or Download.
The selected file will be downloaded.
-
You can view the status of a file transfer operation to view its progress and see if it was successful. If an operation fails, hover over the warning icon to see the error that occurred.
Note: A runtime error displays in the File Transfer status area, if an invalid operation is performed.
You can view the contents of a file from either the system controller or chassis partition CLI.
-
Log in to the command line interface (CLI) of the system controller or chassis partition using an account with admin access.
When you log in to the system, you are in user (operational) mode.
-
View the contents of a file.
file show <*local-file-path*>This example shows how to view the contents of the
velos.logfile:default-1# file show log/velos.log 2022-02-26T18:23:05.160009+00:00 controller-1(p1) partition-bladesd[7]: priority="Info" version=1.0 msgid=0x6602000000000005 msg="DB is not ready". 2022-02-26T18:23:05.161038+00:00 controller-1(p1) tcpdumpd-master[10]: priority="Notice" version=1.0 msgid=0x5402000000000002 msg="tcpdumpd-master starting" VERSION="1.3.18" DATE="Wed Feb 10 17:04:45 2021". 2022-02-26T18:23:05.161047+00:00 controller-1(p1) tcpdumpd-master[10]: priority="Notice" version=1.0 msgid=0x5402000000000004 msg="tcpdumpd-master args." ARGS="/usr/bin/tcpdumpd_master". 2022-02-26T18:23:05.161053+00:00 controller-1(p1) tcpdumpd-master[10]: priority="Notice" version=1.0 msgid=0x5402000000000004 msg="tcpdumpd-master args." ARGS="-r". 2022-02-26T18:23:05.161057+00:00 controller-1(p1) tcpdumpd-master[10]: priority="Notice" version=1.0 msgid=0x5402000000000004 msg="tcpdumpd-master args." ARGS="1". 2022-02-26T18:23:05.161062+00:00 controller-1(p1) tcpdumpd-master[10]: priority="Notice" version=1.0 msgid=0x5402000000000004 msg="tcpdumpd-master args." ARGS="-l". 2022-02-26T18:23:05.161067+00:00 controller-1(p1) partition-bladesd[7]: priority="Info" version=1.0 msgid=0x6602000000000005 msg="DB is not ready". ...
You can import a file from an external serve onto your system from either the system controller or chassis partition CLI.
-
Log in to the command line interface (CLI) of the system controller or chassis partition using an account with admin access.
When you log in to the system, you are in user (operational) mode.
-
Import a file.
file import [ remote-port <*port-number*> } username <*user*> password <*password*> remote-host <*ip-address-or-fqdn*> remote-file <*remote-file-path*> remote-url <*full-remote-url*> local-file <*local-file-path*> [insecure] web-token <*remote-system-token*>Note: The insecure option ignores certificate warnings during the transfer.
This example shows how to import a file to the system controller:
file import username admin password remote-url https://files.company.com/images/BIGIP-1x.x.x.x-x.x.xxx.ALL-F5OS.qcow2.zip local-file images/stagingThis example shows how to import a file to the chassis partition:
file import username admin password remote-url https://files.company.com/images/BIGIP-1x.x.x.x-x.x.xxx.ALL-F5OS.qcow2.zip local-file images -
Return to user (operational) mode.
end -
Optionally, you can check the file transfer status.
file transfer-status file-name <*local-file-path*>
You can cancel an in-progress file import onto your system from either the system controller or chassis partition CLI.
-
Log in to the command line interface (CLI) of the system controller or chassis partition using an account with admin access.
When you log in to the system, you are in user (operational) mode.
-
Get the operation identifier for the file transfer process.
show file transfer-operationsA summary similar to this example displays:
syscon-1-active# show file transfer-operations file transfer-operations transfer-operation images/import/iso/F5OS-C-1.6.0-1234.CONTROLLER.iso files/F5OS-C/controller/images/F5OS-C-1.6.0-1234.CONTROLLER.iso "Import file" "HTTPS " operation-id IMPORT-C16QYpun status "In Progress (13.0%)" timestamp "Fri Mar 24 23:05:54 2023" -
Cancel the specified file transfer.
file abort-transfer operation-id <*id*>This example shows canceling a specified in-progress file transfer:
syscon-1-active# file abort-transfer operation-id IMPORT-C16QYpun Aborting will stop the file transfer. Do you want to proceed? [yes/no] yes result File transfer abort operation initiated.
You can export files to an external server from your system from either the system controller or chassis partition CLI.
-
Log in to the command line interface (CLI) of the system controller or chassis partition using an account with admin access.
When you log in to the system, you are in user (operational) mode.
-
Export a file.
file export insecure local-file <*local-file-path*> protocol { https | scp | sftp } remote-file <*remote-file-path*> remote-host <*ip-address-or-fqdn*> remote-port <*port-number*> remote-url <*ip-address-or-fqdn*> username <*user*> web-token <*remote-system-token*>
You can delete files from either the system controller or chassis partition CLI.
-
Log in to the command line interface (CLI) of the system controller or chassis partition using an account with admin access.
When you log in to the system, you are in user (operational) mode.
-
Delete a file.
file delete file-name <*local-file-path*>
You can configure Network Time Protocol (NTP) for the VELOS system. An NTP server ensures that the system clock is synchronized with Coordinated Universal Time (UTC). The system also provides authentication support for NTP, which can enhance security by ensuring that the system sends time-of-day requests only to trusted NTP servers. You can also configure the time zone and set the time and date manually, if NTP is disabled. You can use either thesystem controller CLI or webUI to configure time settings.
After the VELOS system license is activated, you can configure Network Time Protocol (NTP) servers, including authentication support for NTP, time zone, and manual configuration of date and time, if NTP is disabled. The NTP server ensures that the system clock is synchronized with Coordinated Universal Time (UTC). You can specify a list of servers that you want the system to use when updating the time on network systems. You can configure time settings for the system from the system controller webUI.
-
Log in to the VELOS system controller webUI using an account with admin access.
-
On the left, click SYSTEM SETTINGS > Time Settings.
-
To synchronize the system clock with an NTP server, for NTP Service, select Enabled.
The NTP Service is set to Disabled by default.
-
To set the time and date manually:
-
For NTP Service, select Disabled.
-
In the Manual Time & Date Settings area, click the calendar to set the date and time.
-
-
To use authentication support for NTP:
-
For NTP Authentication, select Enabled.
The NTP Authentication is set to Disabled by default.
-
For NTP Keys, click Add.
The Add NTP Key screen displays.
-
For Key ID, type an identifier used by the client and server to designate a secret key.
The client and server must use the same key ID.
-
For Key Type, select the encryption type used for the NTP authentication key.
The default value is F5_NTP_AUTH_SHA256.
Select from these options:
- F5_NTP_AUTH_MD5
- F5_NTP_AUTH_SHA1
- F5_NTP_AUTH_SHA256
- F5_NTP_AUTH_SHA384
- F5_NTP_AUTH_SHA512
-
For Key Value, paste the text of the NTP authentication key.
-
Click Save & Close.
-
-
To specify an NTP server, from NTP Servers:
-
Click Add.
-
For NTP Server, type the IPv4 address, IPv6 address, or Fully Qualified Domain Name (FQDN) of the NTP server. This information will be displayed in the Name column of the table on the Time Settings screen.
Note: If specifying an FQDN, you must configure a resolvable DNS server for the system. The resolved IP address will display in the NTP Server column of the table on the Time Settings screen. If the FQDN is unresolvable, this will be indicated in the NTP Server column, although this could be a transitional state.
Note: If specifying an IPv4 or IPv6 address, the address will display in both the Name and the NTP Server columns.
-
-
To set the time zone, from Locations, select the time zone region.
-
Click Save & Close.
You can manually configure the date and time for your system from the CLI.
-
Connect using SSH to the system controller floating management IP address.
-
Log in to the command line interface (CLI) of the system controller using an account with admin access.
When you log in to the system, you are in user (operational) mode.
-
Change to config mode.
configThe CLI prompt changes to include
(config). -
Change the system date and/or time.
Note: You can opt to change only the time or only the date by including only the relevant option (either time or date).
system set-datetime date <*YYYY-MM-DD*> time <*HH:MM-SS*>In this example, you change the system date to 2022-01-01 and the system time to be 12:01:00:
syscon-1-active# system set-datetime date 2022-01-01 time 12:01:00
The system date and time are now updated.
You can configure Network Time Protocol (NTP) for your VELOS system from the system controller CLI.
Note: If you want to enable NTP authentication, see Configure NTP authentication from the CLI.
-
Connect using SSH to the system controller floating management IP address.
-
Log in to the command line interface (CLI) of the system controller using an account with admin access.
When you log in to the system, you are in user (operational) mode.
-
Change to config mode.
configThe CLI prompt changes to include
(config). -
Enable NTP.
system ntp config enabled -
Add an NTP server.
system ntp servers server <*ip-address*>In this example, you configure an NTP server at pool.ntp.org:
syscon-1-active(config)# system ntp servers server pool.ntp.org -
Commit the configuration changes.
commit -
Return to user (operational) mode.
end -
Verify that NTP is enabled and a server is configured.
syscon-1-active# show system ntp system ntp state enabled system ntp state enable-ntp-auth false system ntp servers server pool.ntp.org state address pool.ntp.org state port 123 state version 4 state association-type SERVER state iburst false state prefer false state stratum 4 state root-delay 32 state root-dispersion 45 state offset 0 state poll-interval 8 state authenticated false
You can configure Network Time Protocol (NTP) authentication for your VELOS system from the system controller CLI. NTP authentication enhances security by ensuring that the system sends time-of-day requests only to trusted NTP servers.
-
Connect using SSH to the system controller floating management IP address.
-
Log in to the command line interface (CLI) of the system controller using an account with admin access.
When you log in to the system, you are in user (operational) mode.
-
Change to config mode.
configThe CLI prompt changes to include
(config). -
Enable NTP.
system ntp config enabled -
Enable NTP authentication.
system ntp config enable-ntp-auth true -
Add the key associated with your server to the system.
system ntp ntp-keys ntp-key <*public-key-id*> config key-id <*secret-key-id*> key-type [ F5_NTP_AUTH_MD5 | F5_NTP_AUTH_SHA1 | F5_NTP_AUTH_SHA256 | F5_NTP_AUTH_SHA384 | F5_NTP_AUTH_SHA512 ] key-value HEX:<*ntp-auth-key-value*>Important: The ID, key type, and key value on this client system must match the server exactly.
syscon-1-active(config)# system ntp ntp-keys ntp-key 11 config key-id 11 key-type F5_NTP_AUTH_SHA1 key-value HEX:E27611234BB5E7CDFC8A8ACE55B567FC5CA7C890 -
Add an NTP server and associate the key ID you added with the server.
system ntp servers server <*ip-address*>In this example, you configure an NTP server at the IP address pool.ntp.org:
syscon-1-active(config)# system ntp servers server pool.ntp.org syscon-1-active(config-server-pool.ntp.org)# config key-id 11 -
Commit the configuration changes.
commit -
Return to user (operational) mode.
end -
Verify that NTP with authentication is enabled and a server is configured.
syscon-1-active# show system ntp servers system ntp servers server pool.ntp.org state address pool.ntp.org state port 123 state version 4 state association-type SERVER state iburst false state prefer false state stratum 8 state root-delay 0 state root-dispersion 0 state offset 251333 state poll-interval 6 state key-id 11 state authenticated true
Simple Network Management Protocol (SNMP) is an industry-standard protocol that enables you to use a standard SNMP management system to remotely manage network devices. VELOS systems support SNMPv1, SNMPv2c, and SNMPv3. You can configure the system from both the CLI and webUI.
You can use SNMP to monitor VELOS systems at both the system controller and chassis partition levels. For more comprehensive monitoring, configure your system at both levels from the CLI or webUI. SNMP traps always send from the active system controller’s fixed management IP address as the source IP address.
SNMP support is available in different ways, depending on which F5OS software version you are using. On VELOS systems, SNMP is available from both the system controller and chassis partition CLIs and webUIs.
SNMP support is available in different ways, depending on which F5OS software version you are using. On VELOS systems, SNMP is available from both the system controller and chassis partition CLIs and webUIs.
F5 recommends using the newer system snmp commands, which include support for SNMP versions 1, 2c, and 3. For more information on the older commands, see:
|
F5OS-C software version |
Older CLI (v1/v2c only) |
Newer CLI (v1/v2c/v3) |
webUI |
|---|---|---|---|
|
1.5.0 |
SNMP-COMMUNITY-MIB SNMP-NOTIFICATION-MIB SNMP-TARGET-MIB SNMP-VIEW-BASED-ACM-MIB SNMPv2-MIB |
system snmp communities system snmp engine-id system snmp targets system snmp users |
SYSTEM SETTINGS > SNMP Configuration |
Before you configure SNMP access for VELOS systems:
- Add the SNMP manager IP address to the system allow list. For more information, see Allow list overview.
- Add descriptions to front-panel interfaces. For more information, see Configure an interface from the CLI.
- Add descriptions to management interfaces. For more information, see Configure management IP addresses from the CLI.
- Add descriptions to LAGs, if needed. For more information, see Configure a static LAG interface from the CLI.
- Download the F5 MIB files from File Utilities in the system controller or chassis partition webUI (on the left, click SYSTEM SETTINGS > File Utilities, and then from Base Directory, select mibs, select a
.tar.gzfile, and click Download). - Configure a DNS name server if you would like to use a fully-qualified domain name (FQDN) instead of an IP address for the SNMP trap destination. For more information, see Configure DNS from the webUI.
You can view SNMP information in the /log/system/snmp.log file. You can download the log file to your local workstation from the File Utilities screen in the system controller or chassis partition webUI (on the left, click SYSTEM SETTINGS > File Utilities, and then from Base Directory, select log/system, select snmp.log, and click Download).
For more information about managing files from the system controller or chassis partition webUI or CLI, see File utilities overview.
SNMPWALK is an application on an SNMP management system that performs SNMP GETNEXT requests to query a network device for information. You can provide an object identifier (OID) to specify which portion of the object identifier space to search using GETNEXT requests. The SNMP management system queries all variables in the subtree below the specified OID, displays these values to the user, and stops when it returns results that are no longer inside the range of the specified OID.
The IDs display in text format when the corresponding MIB is loaded in your SNMP management system. If the MIB is not loaded, the walk displays in OID format.
To more accurately map these system OIDs, you must download the F5-OS-SYSTEM-MIB.mib file and load it into your SNMP management system. To download the F5 MIB files, use File Utilities in the system controller or chassis partition webUI (on the left, click SYSTEM SETTINGS > File Utilities, and then from Base Directory, select mibs, select a .tar.gz file, and click Download).
You can configure SNMP communities with either version 1, version 2c, or both security models from either the system controller or chassis partition webUI.
-
Log in to the VELOS system controller webUI or the chassis partition webUI using an account with admin access.
-
On the left, click SYSTEM SETTINGS > SNMP Configuration.
-
In the Communities area, click Add.
The Add Community screen displays.
-
For Community, enter a descriptive name.
-
For Security Model, select from these security models: v1, v2c, and v1 and v2c.
-
Click Save & Close.
You can configure SNMP version 3, which is a user-based security model, from either the system controller or chassis partition webUI. This model provides support for additional authentication and privacy protocols.
-
Log in to the VELOS system controller webUI or the chassis partition webUI using an account with admin access.
-
On the left, click SYSTEM SETTINGS > SNMP Configuration.
-
In the Users area, click Add.
The Add V3 User screen displays.
-
For User, enter the user name.
-
For Authentication Protocol, select from these protocols: MD5, SHA, or None.
-
For Authentication Password, enter the password for the specified user.
-
For Privacy Protocol, select from these protocols: AES128, DES, or None.
-
Click Save & Close.
Before you can add an SNMP target, you must have already configured either the SNMPv1/v2c community or SNMPv3 user.
You can configure SNMP targets from either the system controller or chassis partition webUI. These are required to send system-generated traps to a manager. You can choose either community (v1/v2c) or user-based (v3) security.
-
Log in to the VELOS system controller webUI or the chassis partition webUI using an account with admin access.
-
On the left, click SYSTEM SETTINGS > SNMP Configuration.
-
In the Targets area, click Add.
The Add Target screen displays.
-
For Name, enter a descriptive name.
-
For Security Model, select from these security models: v1, v2c, or v3.
-
Select one of these options, depending on the selected security model:
- If you select v1 or v2, for Community, select the community that you created.
- If you select v3, for User, select the user that you created.
-
For IPv4/IPv6, select either IPv4 or IPv6.
-
For Name, enter the IPv4 address, IPv6 address, or fully qualified domain name (FQDN) of the target.
-
For Port, enter the port number for the target.
The default value is 162, and the range is from 1024 to 65535
-
Click Save & Close.
You can configure SNMP communities with either version 1, version 2c, or both security models from either the system controller or chassis partition CLI.
-
Connect using SSH to the system controller floating management IP address or chassis partition management IP address.
-
Log in to the command line interface (CLI) of the system controller or chassis partition using an account with admin access.
When you log in to the system, you are in user (operational) mode.
-
Change to config mode.
configThe CLI prompt changes to include
(config). -
Configure a community.
system snmp communities community <*community-name*> | config security-model { v1 | v2c }This example creates a community that uses the v2c security model:
syscon-1-active(config)# system snmp communities community v2comm config security-model v2cThis example creates a community that uses both v1 and v2c community models:
syscon-1-active(config)# system snmp communities community v1v2c config security-model [ v1 v2c ] -
Commit the configuration changes.
commit -
Return to user (operational) mode.
end -
Verify the community configuration.
show system snmp communitiesA summary similar to this example displays:
syscon-1-active# show system snmp communities SECURITY NAME NAME MODEL ---------------------------------- v1v2c v1v2c [ v1 v2c ]Note: This example shows both security models configured. If you configure only one security model, then only the configured model displays in the output.
You can configure SNMP version 3, which is a user-based security model, from either the system controller or chassis partition CLI. This model provides support for additional authentication and privacy protocols.
-
Connect using SSH to the system controller floating management IP address or chassis partition management IP address.
-
Log in to the command line interface (CLI) of the system controller or chassis partition using an account with admin access.
When you log in to the system, you are in user (operational) mode.
-
Change to config mode.
configThe CLI prompt changes to include
(config). -
Configure a user, including authentication and privacy protocols.
system snmp users user <*user-name*> config authentication-protocol config { md5 | none | sha } privacy-protocol { aes | des | none }This example creates a user that uses MD5 authentication and AES for password authentication:
syscon-1-active(config)# system snmp users user jdoe config authentication-protocol md5 privacy-protocol aes authentication-passwordAfter you press Enter, you are prompted to enter the authentication password.
(<string, min: 8 chars, max: 32 chars>): ********After you press Enter, configure the privacy password.
syscon-1-active(config-user-v3-user)# config privacy-passwordAfter you press Enter, you are prompted to enter the privacy password.
(<string, min: 8 chars, max: 32 chars>): ********* -
Commit the configuration changes.
commit -
Return to user (operational) mode.
end -
Verify the user configuration.
show system snmp usersA summary similar to this example displays:
syscon-1-active# show system snmp users AUTHENTICATION PRIVACY NAME NAME PROTOCOL PROTOCOL -------------------------------------------- jdoe jdoe md5 aes
You can configure SNMP targets with community-based security (SNMPv1/SNMPv2c) from either the system controller or chassis partition CLI. These are required to send system-generated traps to a manager.
-
Connect using SSH to the system controller floating management IP address or chassis partition management IP address.
-
Log in to the command line interface (CLI) of the system controller or chassis partition using an account with admin access.
When you log in to the system, you are in user (operational) mode.
-
Change to config mode.
configThe CLI prompt changes to include
(config). -
Configure a target with community-based security.
system snmp targets target <*target-name*> config community <*community-name*> security-model { v1 | v2c } { ipv4 | ipv6 } address <*ip-address*> port <*port-number*>This example creates a target with community-based security:
syscon-1-active(config)# system snmp targets target v2c-target config community v2c-comm security-model v2c ipv4 address 192.0.2.24 port 5001 -
Commit the configuration changes.
commit -
Return to user (operational) mode.
end -
Verify the target configuration.
show system snmp usersA summary similar to this example displays:
syscon-1-active# show system snmp targets SECURITY NAME NAME USER COMMUNITY MODEL ADDRESS PORT ADDRESS PORT ----------------------------------------------------------------------------------------- v2c-target v2c-target jdoe - - 192.0.2.24 5001 - -
You can configure SNMP targets with user-based security (SNMPv3) from either the system controller or chassis partition CLI. These are required to send system-generated traps to an SNMP management system.
-
Connect using SSH to the system controller floating management IP address or chassis partition management IP address.
-
Log in to the command line interface (CLI) of the system controller or chassis partition using an account with admin access.
When you log in to the system, you are in user (operational) mode.
-
Change to config mode.
configThe CLI prompt changes to include
(config). -
Configure a target with user-based security.
system snmp targets target <*target-name*> config user <*user-name*> { ipv4 | ipv6 } address <*ip-address*> port <*port-number*>This example creates a target with user-based security:
syscon-1-active(config)# system snmp targets target v3-target config user jdoe ipv4 address 192.0.2.24 port 5001 -
Commit the configuration changes.
commit -
Return to user (operational) mode.
end -
Verify the target configuration.
show system snmp targetsA summary similar to this example displays:
syscon-1-active# show system snmp targets SECURITY NAME NAME USER COMMUNITY MODEL ADDRESS PORT ADDRESS PORT ----------------------------------------------------------------------------------------- v3-target v3-target jdoe - - 192.0.2.24 5001 - -
You can back up the configurations of the system controller or chassis partition in which you are working from the webUI.
-
Log in to the VELOS system controller webUI or the chassis partition webUI using an account with admin access.
-
On the left, click SYSTEM SETTINGS > Configuration Backup.
-
Click Create.
The Create Configuration Backup popup opens.
-
In the Name field, enter a name for the backup (for example, system-controller-12-21-21 or partition1-6-14-21).
-
Click Create.
The backup is created and added to the list.
-
To delete a backup file, select the file and click Delete.
System controller and chassis partition configuration backups are stored in configs/. Backups should be stored off the system.
You can restore configurations from the CLI. For more information on saving and restoring the configuration, see the Complete backup and restore overview section.
You can activate a license for the VELOS system from either the system controller CLI or webUI. There is one license per VELOS system, which is used by the chassis partitions and any tenants.
There are two ways to license the system:
- Automatically
- If your system is connected to the internet, use the Automatic method to prompt the system to contact the F5 license server and activate the license.
- Manually
- If your system is not connected to the internet, use a management workstation that is connected to the internet to retrieve an activation key from F5 and then transfer it to the system.
Important:
Adding or reactivating a license on an active VELOS system might impact traffic on tenantsrunning on chassis partitions. Traffic processing will stop briefly on the tenants, and then restart automatically. This occurs when the tenant receives a new or reactivated license causing a configuration reload on the tenants. For more information, see these other references:
- VELOS Systems: Installation and Upgrade at Documentation - F5OS-C and VELOS
- K31810358: Activating the license on a VELOS system causes a brief traffic disruption on tenants
- K7752: Licensing the BIG-IP system
- For information about BIG-IP Next licensing, also see the documentation on my.f5.com and clouddocs.f5.com.
You can license the system automatically from the webUI, as long as the system has internet access.
-
Log in to the VELOS system controller webUI using an account with admin access.
-
On the left, click SYSTEM SETTINGS > Licensing.
-
For the Base Registration Key field, the registration key is auto-populated.
You can choose to overwrite this field with a new registration key.
-
For the Add-On Keys field, the associated add-on keys are auto-populated.
You can click + or x to add or remove additional add-on keys.
Note: To add add-on keys to a licensed system, enter the keys in the Add-On Keys field and click Reactivate.
-
For the Activation Method, select Automatic.
-
Click Activate.
The End User License Agreement (EULA) displays.
-
Click Agree to accept the EULA, .
The system is now licensed. If a base registration key or add-on key fails to activate, try re-activating the license or contact support.f5.com.
You can use the system controller webUI to manually license the VELOS system for systems without access to the internet.
-
Log in to the VELOS system controller webUI using an account with admin access.
-
On the left, click SYSTEM SETTINGS > Licensing.
-
For the Base Registration Key field, the registration key is auto-populated.
You can choose to overwrite this field with a new registration key.
-
For the Add-On Keys field, the associated add-on keys are auto-populated.
You can click + or x to add or remove additional add-on keys.
Note: To add add-on keys to a licensed system, enter the keys in the Add-On Keys field and click Reactivate.
-
For the Activation Method, select Manual.
-
For the Device Dossier, click Get Dossier.
The VELOS system refreshes and displays the dossier.
-
Copy the dossier text into the Device Dossier field.
-
Click Click here to access F5 Licensing Server.
The Activate F5 Product page displays.
-
Paste the dossier in the Enter Your Dossier field.
-
Click Next.
The license key text displays.
-
Copy the license key text.
Alternatively, you can use the F5 license activation portal at activate.f5.com/license.
-
In the License Text field, paste the license key text.
-
Click Activate.
The End User License Agreement (EULA) displays.
-
Click Agree to accept the EULA.
The system is now licensed. If a base registration key or add-on key fails to activate, try re-activating the license or contact support.f5.com.
You can view information about the software license activated on your system, including license activation and expiration dates, service check date, and licensed modules, from either the system controller or chassis partition webUIs.
-
Log in to the VELOS system controller webUI or the chassis partition webUI using an account with admin access.
-
On the left, click SYSTEM SETTINGS > Licensing.
-
View the license information for the system.
For automatic VELOS system licensing, the system needs to be able to connect to the F5 licensing server either through the internet or another means of networking. You need to have the Base Registration Key (five sets of characters separated by hyphens) provided by F5, and any add-on keys (two sets of 7 characters separated by a hyphen) that you have purchased. The Base Registration Key with associated add-on keys are pre-installed on a new VELOS system.
You can activate the VELOS system license automatically from the system controller CLI.
-
Connect using SSH to the system controller floating management IP address.
-
Log in to the command line interface (CLI) of the system controller using an account with admin access.
When you log in to the system, you are in user (operational) mode.
-
Change to config mode.
configThe CLI prompt changes to include
(config). -
Apply a license to the chassis.
system licensing install registration-key <*key*>The registration key is optional. If it is not included, the system uses the one that is already pre-installed. If no registration key is found, you receive an error.
This example applies a specified base registration license to the system:
syscon-1-active(config)# system licensing install registration-key I1234-12345-12345-12345-1234567 result License installed successfully. -
Apply any add-on keys.
system licensing install add-on-keys <*add-on-keys*>This example enables the additional features associated with the three specified add-on-keys, along with the entitlements of the base registration key:
syscon-1-active(config)# system licensing install add-on-keys [1234567-1234567 2345678-2345678 3456789-3456789] result License installed successfully.
The VELOS system is licensed. The license and any add-on keys apply to all partitions and tenants.
You can activate the VELOS system license manually from the system controller CLI.
-
Connect using SSH to the system controller floating management IP address.
-
Log in to the command line interface (CLI) of the system controller using an account with admin access.
When you log in to the system, you are in user (operational) mode.
-
Change to config mode.
configThe CLI prompt changes to include
(config). -
Get the system dossier.
system licensing get-dossier [registration-key XXXXX-XXXXX-XXXXX-XXXXX-XXXXXXX]The registration key is optional. If it is not included, the system uses the one already pre-installed. If no registration key is found, you receive an error.
The dossier for the system displays.
-
Get the license file using the dossier output you just received by going to the F5 siteactivate.f5.com/license/dossier.jsp.
-
Install the license.
-
Copy the license file text.
-
Run the manual install command and press Enter:
system licensing manual-install license -
Paste the license file content in multiline mode, then press Ctrl+D.
syscon-1-active(config)# system licensing manual-install license Value for 'license' (<string>): [Multiline mode, exit with ctrl-D.] > -
The VELOS system is licensed. The license applies to all of the chassis partitions and tenants.
You can display the license of a VELOS system from the system controller CLI.
-
Connect using SSH to the system controller floating management IP address.
-
Log in to the command line interface (CLI) of the system controller using an account with admin access.
When you log in to the system, you are in user (operational) mode.
-
Display the system license in a simple form.
show system licensingA summary similar to this example displays:
syscon-1-active# show system licensing system licensing license Licensed version 7.4.0 Registration Key Gxxxx-xxxxx-xxxxx-xxxxx-xxxxxxxx Licensed date 2021/01/01 License start 2021/04/16 License end 2022/01/01 Service check date 2021/12/02 Platform ID F101 Appliance SN chs600144s Active Modules Local Traffic Manager, CX410 (Exxxxxx-xxxxxx) Best Bundle, CX410 APM-Lite Carrier Grade NAT (AFM ONLY) Max Compression, CX410 Rate Shaping Max SSL, CX410 Advanced Firewall Manager, CX410 Access Policy Manager, Base, CX410 Anti-Virus Checks Base Endpoint Security Checks Firewall Checks Machine Certificate Checks Network Access Protected Workspace Secure Virtual Keyboard APM, Web Application App Tunnel Remote Desktop Advanced Routing, CX410 Advanced Web Application Firewall, CX410 DNS, Max QPS, CX410 -
Display the raw license file content that was received from the F5 license server.
show running-config system licensing
The VELOS system is licensed. The license applies to all of the chassis partitions and tenants.
A cluster on a VELOS system is group of blades or nodes working together as a logical unit. The Cluster Details screen on the chassis partition webUI provides detailed information about clusters that might be useful when a chassis partition is made up of more than one slot/blade.
You can view detailed information about clusters from the chassis partition webUI.
-
Log in to the VELOS chassis partition webUI using an account with admin access.
-
On the left, click SYSTEM SETTINGS > Cluster Details.
-
Set the Auto Refresh interval for refreshing the data displayed or click the refresh icon to update the data immediately.
-
View the cluster detail information.
You can view detailed information about clusters from the chassis partition CLI.
-
Log in to the command line interface (CLI) of the chassis partition using an account with admin access.
When you log in to the system, you are in user (operational) mode.
-
Show all cluster details.
show clusterA summary similar to this excerpt displays:
default-1# show cluster cluster state cluster disk-usage-threshold state warning-limit 85 cluster disk-usage-threshold state error-limit 90 cluster disk-usage-threshold state critical-limit 97 cluster disk-usage-threshold state growth-rate-limit 10 cluster disk-usage-threshold state interval 60 cluster nodes node blade-1 state enabled true state assigned true state node-running-state running state present single state platform-id B60100 state slots [ 1 ] state platform fpga-state FPGA_RDY state platform dma-agent-state DMA_AGENT_RDY state slot-number 1 state node-info creation-time 2023-01-06T02:11:09Z state node-info cpu 28 state node-info pods 250 state node-info memory 131576224Ki state ready-info ready true ...
You can configure general system settings for the VELOS system, such as system hostname, login banner, and message of the day (MOTD) banner. Depending on which setting you want to configure, you can use either the CLI or the webUI.
You can configure general system settings, including hostname, login banner, message of the day (MOTD) banner, and an advisory banner from the system controller webUI. When enabled and configured, the advisory banner will display at the top of the webUI after authentication. The product name displays but cannot be changed.
-
Log in to the VELOS system controller webUI using an account with admin access.
-
On the left, click SYSTEM SETTINGS > General.
-
For Hostname, enter a custom hostname for the system.
-
For Login Banner, enter any text to be displayed when users log in to the system.
-
For MOTD Banner, enter any text to be displayed as a MOTD when users log in to the system.
-
For Advisory Banner, select Enabled or Disabled.
-
For Advisory Banner Color, select the color for the banner.
-
For Advisory Banner Text, enter the text for the banner. The maximum number of characters is 80.
-
Click Save.
You can configure general system settings, including login banner, message of the day (MOTD) banner, advisory banner, and time zone/location from the chassis partition webUI. When enabled and configured, the advisory banner will display at the top of the webUI after authentication.
-
Log in to the command line interface (CLI) of the chassis partition using an account with admin access.
When you log in to the system, you are in user (operational) mode.
-
On the left, click SYSTEM SETTINGS > General.
-
For Login Banner, enter any text to be displayed when users log in to the chassis partition.
-
For MOTD Banner, enter any text to be displayed as a MOTD when users log in to the chassis partition.
-
For Advisory Banner, select Enabled or Disabled.
-
For Advisory Banner Color, select the color for the banner.
-
For Advisory Banner Text, enter the text for the banner. The maximum number of characters is 80.
-
From Time Zone/Locations, select the time zone region.
-
Click Save.
You can manually configure the hostname for your system from either the system controller or chassis partition CLI. The hostname must be a fully-qualified domain name (FQDN).
-
Log in to the command line interface (CLI) of the system controller or chassis partition using an account with admin access.
When you log in to the system, you are in user (operational) mode.
-
Change to config mode.
configThe CLI prompt changes to include
(config). -
Change the hostname.
system config hostname <*hostname*>The minimum length is 1 character, and the maximum length is 253 characters.
In this example, you change the hostname for the system to test.company.com:
syscon-1-active# system config hostname test.company.com
The system hostname is now updated.
You can configure the login banner for your system manually from either the system controller or chassis partition CLI. The login banner displays before users log in to each respective system.
-
Log in to the command line interface (CLI) of the system controller or chassis partition using an account with admin access.
When you log in to the system, you are in user (operational) mode.
-
Change to config mode.
configThe CLI prompt changes to include
(config). -
Change the login banner text.
system config login-bannerIn this example, you change the login banner text to notify users that unauthorized access is prohibited:
syscon-1-active(config)# system config login-banner (<string>): [Multiline mode, exit with ctrl-D.] UNAUTHORIZED ACCESS TO THIS DEVICE IS PROHIBITED -
Commit the configuration changes.
commit
The login banner is now updated.
You can manually configure the message-of-the-day (MOTD) banner for your system from either the system controller or chassis partition CLI. The MOTD banner displays after users log in to each respective system.
-
Log in to the command line interface (CLI) of the system controller or chassis partition using an account with admin access.
When you log in to the system, you are in user (operational) mode.
-
Change to config mode.
configThe CLI prompt changes to include
(config). -
Change the MOTD banner text.
system config motd-bannerIn this example, you change the login banner text to notify users of upcoming system maintenance:
syscon-1-active(config)# system config motd-banner (<string>): [Multiline mode, exit with ctrl-D.] ATTENTION! This system is scheduled for maintenance in two days. -
Commit the configuration changes.
commit
The MOTD banner is now updated.
You can verify the current MAC allocation data from the system controller CLI.
-
Log in to the command line interface (CLI) of the system controller using an account with admin access.
When you log in to the system, you are in user (operational) mode.
-
Display the current MAC allocation data.
show system mac-allocationA summary similar to this example displays:
syscon-1-active# show system mac-allocation system mac-allocation state free-single-macs 144 system mac-allocation state allocated-single-macs 16 system mac-allocation state free-large-blocks 24 system mac-allocation state allocated-large-blocks 0 system mac-allocation state total-free-mac-count 912 system mac-allocation state total-allocated-mac-count 16 system mac-allocation state total-mac-count 928
You can verify the current runtime status of the MAC pool from the system controller CLI.
-
Log in to the command line interface (CLI) of the system controller using an account with admin access.
When you log in to the system, you are in user (operational) mode.
-
Display the current chassis MAC allocation.
show system chassis-macsA summary similar to this example displays:
syscon-1-active# show system chassis-macs system chassis-macs base 000a49ff1800 ALLOCATED IDENTIFIER UUID OFFSET MAC ADDRESS INDEX AS SINGLE ----------------------------------------------------------------------------------------------- 1 c2c66fb4-7426-4134-8110-a0fb4547c866 8 00:0a:49:ff:18:08 - - 9 00:0a:49:ff:18:09 - - 10 00:0a:49:ff:18:0a - - 11 00:0a:49:ff:18:0b - - 12 00:0a:49:ff:18:0c - - 13 00:0a:49:ff:18:0d - - 14 00:0a:49:ff:18:0e - - 15 00:0a:49:ff:18:0f - - 16 00:0a:49:ff:18:10 - - 17 00:0a:49:ff:18:11 - - 18 00:0a:49:ff:18:12 - - 19 00:0a:49:ff:18:13 - - 20 00:0a:49:ff:18:14 - - 21 00:0a:49:ff:18:15 - - 22 00:0a:49:ff:18:16 - - 23 00:0a:49:ff:18:17 - - 28 00:0a:49:ff:18:1c 0 false 29 00:0a:49:ff:18:1d 0 false 30 00:0a:49:ff:18:1e 0 false 31 00:0a:49:ff:18:1f 0 false 32 00:0a:49:ff:18:20 0 false 33 00:0a:49:ff:18:21 0 false 34 00:0a:49:ff:18:22 0 false 35 00:0a:49:ff:18:23 0 false 36 00:0a:49:ff:18:24 0 false 37 00:0a:49:ff:18:25 0 false 38 00:0a:49:ff:18:26 0 false 39 00:0a:49:ff:18:27 0 false 40 00:0a:49:ff:18:28 0 false 41 00:0a:49:ff:18:29 0 false 42 00:0a:49:ff:18:2a 0 false 43 00:0a:49:ff:18:2b 0 false 44 00:0a:49:ff:18:2c 0 false 45 00:0a:49:ff:18:2d 0 false 46 00:0a:49:ff:18:2e 0 false 47 00:0a:49:ff:18:2f 0 false 48 00:0a:49:ff:18:30 0 false 49 00:0a:49:ff:18:31 0 false 50 00:0a:49:ff:18:32 0 false 51 00:0a:49:ff:18:33 0 false 52 00:0a:49:ff:18:34 0 false 53 00:0a:49:ff:18:35 0 false 54 00:0a:49:ff:18:36 0 false 55 00:0a:49:ff:18:37 0 false 56 00:0a:49:ff:18:38 0 false 57 00:0a:49:ff:18:39 0 false 58 00:0a:49:ff:18:3a 0 false 59 00:0a:49:ff:18:3b 0 false
If you are having an issue with a chassis partition (such as unusually high CPU or memory usage or lockup), it is possible that rebooting a blade in the chassis partition might help to resolve the issue.
When there is a problem, the system sends alerts that you would see on the dashboard or on the Alarms & Events screen. A blade status of Not ready for a prolonged time on the General screen can also indicate the need to reboot the blade. You should rarely have to reboot a blade, however, because typically if the VELOS system needs to reboot a blade, it will do so automatically without administrator intervention. F5 recommends working with customer support if you think a blade reboot is necessary.
You can manually reboot a system controller in your VELOS system from the system controller CLI.
-
Connect using SSH to the system controller floating management IP address.
-
Log in to the command line interface (CLI) of the system controller using an account with admin access.
When you log in to the system, you are in user (operational) mode.
-
Reboot a system controller.
system reboot controllers controller { active | standby ]In this example, you reboot the standby system controller:
syscon-1-active# system reboot controllers controller standby
The specified system controller reboots.
You can reboot a system controller from the system controller webUI.
-
Log in to the VELOS chassis partition webUI using an account with admin access.
-
On the left, click SYSTEM SETTINGS > General.
-
Review the status of the system controllers.
The Reboot button will not be available for a system controller that is currently being rebooted.
-
If you decide that a reboot is necessary, click Reboot to the right of the system controller that you want to reboot.
If the system controller has the active role, a popup displays asking you to confirm the reboot operation. This causes a failover to the standby controller.
The It takes a few minutes for the system controller to reboot. The status will show
Reboot in progress, thenNot ready, and when reboot is complete, it saysReady.
You can manually reboot a blade in your system from the chassis partition CLI.
-
Connect using SSH to the chassis partition management IP address.
-
Log in to the command line interface (CLI) of the chassis partition using an account with admin access.
When you log in to the system, you are in user (operational) mode.
-
Reboot a blade.
cluster nodes node <*blade-number*> rebootIn this example, you reboot blade-1:
default-1#(config) cluster nodes node blade-1 reboot
The specified blade reboots.
You can reboot a blade within a chassis partition from the chassis partition webUI.
-
Log in to the VELOS chassis partition webUI using an account with admin access.
-
On the left, click SYSTEM SETTINGS > General.
-
Review the status of each of the blades in the chassis partition.
The Reboot button will not be available for slots that do not have blades present, or for blades that are currently being rebooted.
-
If you have tenants running on the chassis partition you might want to warn users that their service might be interrupted temporarily.
-
If you decide that a reboot is necessary, click Reboot to the right of the slot containing the blade that you want to reboot.
It takes a few minutes for the blade to reboot. The status will show
Reboot in progress, thenNot ready, and when reboot is complete, it saysReady.
