Applies To:
Show Versions
BIG-IP AAM
- 11.5.10, 11.5.9, 11.5.8, 11.5.7, 11.5.6, 11.5.5, 11.5.4, 11.5.3, 11.5.2, 11.5.1
Overview: Configuring the BIG-IP system in routed mode
A routed deployment is one method of deploying a BIG-IP system directly in the path of traffic, such as between a WAN router and LAN switch. In routed mode, the BIG-IP system is nontransparent on the network, with separate LAN and WAN self IP addresses on each side. This setup ensures that requests from clients go to the BIG-IP system, which optimizes the traffic before it reaches the server.
Illustration of a routed deployment
This illustration shows a pair of BIG-IP systems in a routed deployment (Site B) on one side of the WAN, and a one-arm deployment on the other side.
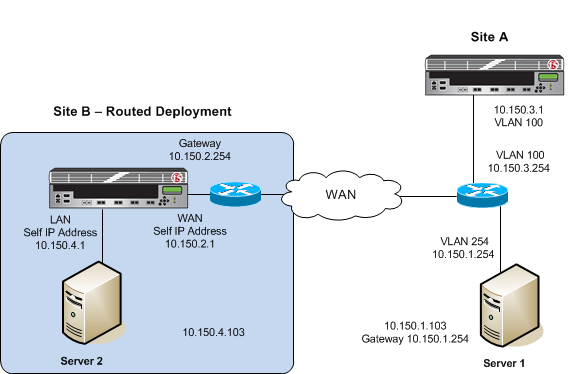 Example of a routed deployment
Example of a routed deployment
About symmetric optimization using iSession on BIG-IP systems
The BIG-IP systems work in pairs on opposite sides of the WAN to optimize the traffic that flows between them through an iSession connection. A simple point-to-point configuration might include BIG-IP systems in data centers on opposite sides of the WAN. Other configuration possibilities include point-to-multipoint (also called hub and spoke) and mesh deployments.
The following illustration shows an example of the flow of traffic across the WAN through a pair of BIG-IP devices. In this example, traffic can be initiated on both sides of the WAN.
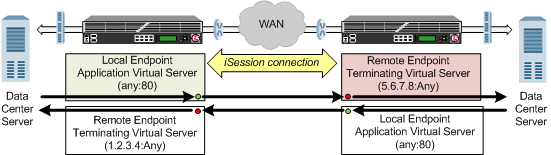 Example of traffic flow through a BIG-IP pair with iSession connection
Example of traffic flow through a BIG-IP pair with iSession connection
Each BIG-IP device is an endpoint. From the standpoint of each BIG-IP device, it is the local endpoint. Any BIG-IP device with which the local endpoint interacts is a remote endpoint. After you identify the endpoints, communication between the BIG-IP pair takes place in an iSession connection between the two devices. When you configure the local BIG-IP device, you also identify any advertised routes, which are subnets that can be reached through the local endpoint. When viewed on a remote system, these subnets appear as remote advertised routes.
To optimize traffic, you create iApps templates to select the applications you want to optimize, and the BIG-IP system sets up the necessary virtual servers and associated profiles. The system creates a virtual server on the initiating side of the WAN, with which it associates a profile that listens for TCP traffic of a particular type (HTTP, CIFS, FTP). The local BIG-IP system also creates a virtual server, called an iSession listener, to receive traffic from the other side of the WAN, and it associates a profile that terminates the iSession connection and forwards the traffic to its destination. For some applications, the system creates an additional virtual server to further process the application traffic.
The default iSession profile, which the system applies to application optimization, includes symmetric adaptive compression and symmetric data deduplication.
Before you begin configuring an iSession connection
Before you configure an iSession connection on the BIG-IP system, make sure that you have completed the following general prerequisites.
- You must have an existing routed IP network between the two locations where the BIG-IP devices will be installed.
- One BIG-IP system is located on each side of the WAN network you are using.
- The BIG-IP hardware is installed with an initial network configuration applied.
- F5 recommends that both units be running the same BIG-IP software version.
- The Application Acceleration Manager license is enabled.
- Application Acceleration Manager (AAM) is provisioned at the level Nominal.
- The management IP address is configured on the BIG-IP system.
- You must have administrative access to both the Web management and SSH command line interfaces on the BIG-IP system.
- If there are firewalls, you must have TCP port 443 open in both directions. Optionally, you can allow TCP port 22 for SSH access to the command line interface for configuration verification, but not for actual BIG-IP iSession traffic. After you configure the BIG-IP system, you can perform this verification from the Configuration utility ().
Task summary
If you are configuring a BIG-IP system in routed mode, you configure separate self IP addresses for the internal and external interfaces. Also, you need to create a passthrough virtual server that you can use to verify the connection before you try to optimize traffic.
Task list
Creating self IP addresses for internal and external VLANs
Creating a default gateway
Creating a passthrough virtual server
Checking connectivity
- Ping the gateway using the command-line access to the BIG-IP system.
- Ping end-to-end across the WAN. In the example shown, this is between Server 1 and Server 2.
- Initiate a TCP file transfer between Server 1 and Server 2.
Setting up an iSession connection using the Quick Start screen
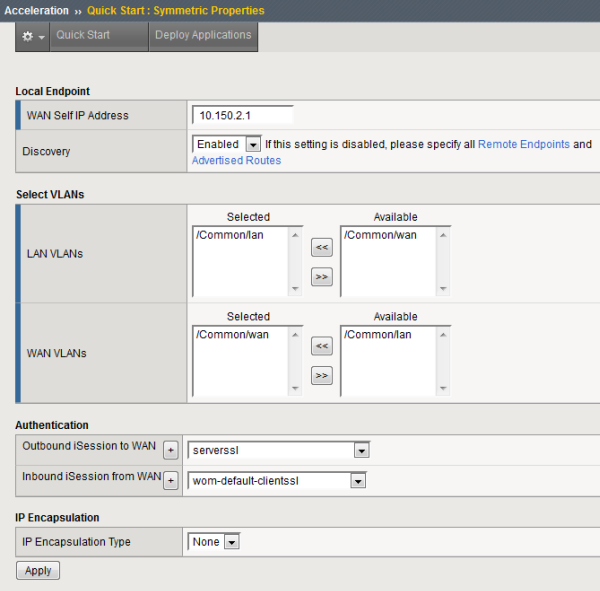 Example of completed Quick Start screen
Example of completed Quick Start screen
Validating iSession configuration
Implementation result
After you complete the tasks in this implementation, the BIG-IP system is configured in a routed deployment. For symmetric optimization using an iSession connection, you must also configure the BIG-IP system on the other side of the WAN. The other BIG-IP deployment can be in bridge, routed, or one-arm mode.





