Applies To:
Show Versions
BIG-IP LTM
- 12.1.6, 12.1.5, 12.1.4, 12.1.3, 12.1.2, 12.1.1, 12.1.0
Overview: DS-Lite Configuration on BIG-IP systems
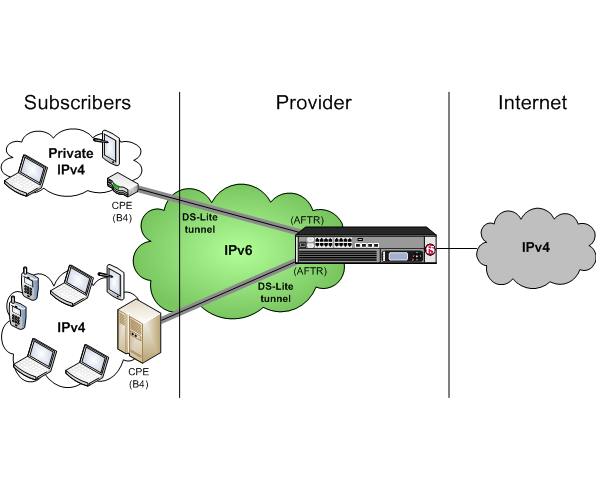
As IPv4 addresses are becoming depleted, service providers (DSL, cable, and mobile) face the challenge of supplying IP addresses to new customers. Providing IPv6 addresses alone is often not workable, because most of the public Internet still uses only IPv4, and many customer systems do not yet fully support IPv6. The Dual-Stack Lite (DS-Lite) tunneling technology is one solution to this problem. DS-Lite gives service providers the means to migrate to an IPv6 access network without changing end user devices or software.
What is DS-Lite?
DS-Lite is an IPv4-to-IPv6 transition technology, described in RFC 6333, that uses tunneling and network address translation (NAT) to send IPv4 packets over an IPv6 network. This technology makes it possible, for example, for a service provider with an IPv6 backbone to properly route traffic while overlapping IPv4 networks.
How does DS-Lite work?
The customer-premises equipment (CPE), known as the B4 (Basic Bridging BroadBand) device, encapsulates the IPv4 packets inside IPv6 packets, and sends them to the AFTR (Address Family Transition Router) device. The AFTR device includes carrier-grade NAT (CGNAT), which has a global IPv4 address space. The AFTR device decapsulates the IPv4 traffic and performs address translation, as it sends the traffic to the external IPv4 network.
How does F5 implement DS-Lite?
On the BIG-IP® system, a DS-Lite tunnel is a variation of IPIP tunnels that uses augmented flow lookups to route traffic. Augmented flow lookups include the IPv6 address of the tunnel to identify the accurate source of packets that might have the same IPv4 address. When the BIG-IP device receives an IPv6 encapsulated packet, the system terminates the tunnel, decapsulates the packet, and marks it for DS-Lite. When the system re-injects the packet into the IP stack, it performs an augmented flow lookup to properly route the response.
Illustration of a DS-Lite deployment
In this example, a service provider transports encapsulated IPv4 traffic over its IPv6 network.
Example of a DS-Lite configuration
Task summary
About CGNAT hairpinning
An optional feature on the BIG-IP ®system, hairpinning routes traffic from one subscriber's client to an external address of another subscriber's server, where both client and server are located in the same subnet. To each subscriber, it appears that the other subscriber's address is on an external host and on a different subnet. The BIG-IP system can recognize this situation and send, or hairpin, the message back to the origin subnet so that the message can reach its destination.





