Applies To:
Show Versions
BIG-IQ Centralized Management
- 5.2.0
What elements make up a Centralized Management deployment?
A F5® BIG-IQ® Centralized Management solution involves a number of components. This diagram illustrates those that make up the BIG-IQ® Centralized Management solution.
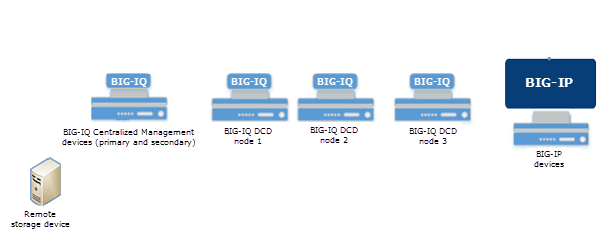
Centralized Management network topology
BIG-IQ Centralized Management device
F5® BIG-IQ® Centralized Management is a platform that helps you manage BIG-IP® devices, and all of their services (such as LTM®, AFM™, or ASM®), from one location. That means you and your co-workers don't have to log in to individual BIG-IP systems to get your job done. Using BIG-IQ Centralized Management, you can centrally manage your BIG-IP devices, performing operations such as backups, licensing, monitoring, and configuration management. And because access to each area of BIG-IQ is role based, you can limit access to users maximizing work flows while minimizing errors and potential security issues.
BIG-IQ data collection device
A BIG-IQ data collection device (DCD) is a specially-provisioned BIG-IQ® system that you use to manage and store alerts, events, and statistical data from one or more BIG-IP® systems.
Configuration tasks on the BIG-IP system determine when and how alerts or events are triggered on the client. The alerts or events are sent to a BIG-IQ data collection device, and the BIG-IQ system retrieves them for your analysis. When you opt to collect statistical data from the BIG-IP devices, the DCD periodically retrieves those statistics from your devices, and then processes and stores that data.
The group of data collection devices and BIG-IQ systems that work together to store and manage your data are referred to as the data collection cluster. The individual data collection devices are generally referred to as nodes.
BIG-IP device
A BIG-IP device runs a number of licensed components designed around application availability, access control, and security solutions. These components run on top ofF5® TMOS®. This custom operating system is an event driven operating system designed specifically to inspect network and application traffic and make real-time decisions based on the configurations you provide. The BIG-IP software runs on both hardware and virtualized environments.
Remote storage device
The remote storage device is necessary only when your deployment includes a data collection device (DCD) and you plan to store backups of your events, alerts, and statistical data for disaster recovery requirements.
Network Requirements for a BIG-IQ Centralized Management Deployment
Before you deploy a Centralized Management solution
Before you begin to deploy a BIG-IQ® system, you should complete these preparations.
- Determine the deployment scenario that works best for your needs.
- Create the interfaces, communications, and networks needed to support your deployment scenario
- Configure your network (including switches and firewalls) to permit BIG-IQ network traffic to flow based on the deployment scenario you choose.
- Assemble the passwords, IP addresses, and licensing information needed for the BIG-IQ cluster components.
Planning for a Centralized Management deployment
To successfully deploy a BIG-IQ® Centralized Management solution, you may need to coordinate with several people in your company.
If you use BIG-IQ virtual editions, you might need to coordinate with the people who manage your virtual environment, so they can provision the virtual machines with the required amount of CPUs, memory, and network interfaces. Further, you’ll need to coordinate with the people who manage the storage for the virtual machines to make sure each virtual machine is provisioned with the necessary storage to support the BIG-IQ environment. You also might need to provide the virtual environment team a copy of the BIG-IQ virtual machine image (available from https://downloads.f5.com), depending how they operate.
If you use BIG-IQ 7000 devices in your network, you need to coordinate with the people who manage the data center where the BIG-IQ devices are housed to make arrangements for the devices to be racked, powered on, and connected to your network.
- IP address allocation for the BIG-IQ nodes, depending on your deployment model.
- Creation of networks, VLANs, and so on dependent on your deployment model.
- Any routing configuration required to ensure traffic passes between the BIG-IQ nodes and the BIG-IP devices.
- Additional networking configuration required to support the BIG-IQ system's operation.
Finally, you may need to coordinate with your network firewall administrators, depending on the network configuration at your company. The BIG-IQ software needs to communicate between BIG-IQ nodes and BIG-IP systems; and, if there are firewalls in the network path, firewall rules probably need to be configured to permit that traffic. For additional detail about required network ports and protocols, refer to Open ports required for data collection device cluster deployment.
Determining the network configuration needed for your deployment
| Which deployment type should you choose? | What functions does your deployment need to perform? | Which hardware components and networks do you need? |
|---|---|---|
| Simple management and configuration. | Manage and configure the BIG-IP® devices. For example, taking backups, licensing virtual editions, and configuring local traffic and security policies. | All you need is one or more BIG-IQ system and the BIG-IP devices you want to manage. This configuration uses a single management network. |
| Advanced management and configuration. | Manage and configure the BIG-IP devices. For example, taking backups, licensing
virtual editions, and configuring local traffic and security policies. Collect and view Local Traffic, DNS, and Device statistical data from the BIG-IP devices. Collect, manage, and view events and alerts from BIG-IP devices provisioned with the APM®, FPS, or ASM® components. |
You need BIG-IQ systems, data collection devices, and an external storage device. This configuration needs a single, management network and an internal BIG-IQ cluster network. |
| Large-scale, distributed management and configuration | Manage and configure the BIG-IP devices. For example, taking backups, licensing
virtual editions, and configuring local traffic and security policies. Collect and view Local Traffic, DNS, and Device statistical data from the BIG-IP devices. Collect, manage, and view events and alerts from BIG-IP devices provisioned with the APM, FPS, or ASM components. Separate network traffic to support large, distributed deployments of the F5 BIG-IQ Centralized Management solution for improved performance, security, and interactions in multiple data center environments. |
You need BIG-IQ systems, data collection devices, and an external storage device. This configuration needs an external network, a management network, and an internal network. |
Network environment for simple management and configuration
To deploy this configuration, all you need is one or more BIG-IQ® systems and the BIG-IP® devices you want to manage. The number of BIG-IQ systems you need depends on how much redundancy your business requires. A second system provides high availability failover capability. Or, for disaster recovery capability, you could operate multiple data centers, each with its own set of BIG-IQ systems. (For additional detail, refer to Managing Disaster Recovery Scenarios.)
The simple management and configuration uses a single management network. Traffic on the management network is used to do the following:
- Provide communication between the BIG-IQ system and DCD nodes.
- Enable bidirectional traffic between the BIG-IQ systems and the BIG-IP devices.
- If you use a secondary high availability BIG-IQ system, enable traffic between the BIG-IQ systems. This traffic keeps the state information synchronized on your BIG-IQ systems.
- Provide access the BIG-IQ user interface. You can also use it to access the BIG-IQ system using SSH if you need to run manual commands.
The figure illustrates the network topology required for a simple management and configuration deployment.
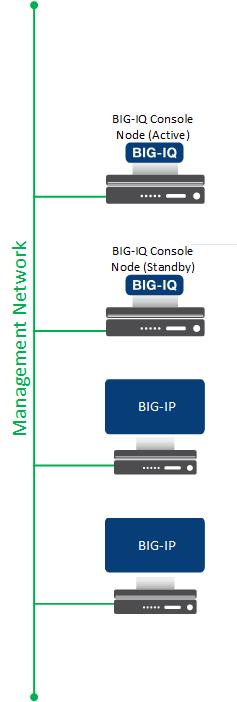
Centralized management network topology
Use the table to record the IP addresses for the devices in the BIG-IQ deployment.
| Device Type | Management IP address(es) |
|---|---|
| Primary BIG-IQ system | |
| Secondary BIG-IQ system | |
| BIG-IP devices |
Network environment for advanced management and configuration
To deploy this configuration, you need BIG-IQ® systems, Data Collection Devices, and an external storage device. This configuration needs a single management network, an internal BIG-IQ cluster network, and an optional external storage device for backing up alert, event, and statistical data..
Traffic on the management network is used to do the following:
- Provide communication between the BIG-IQ system and DCD nodes.
- Enable bidirectional traffic between the BIG-IQ systems and the BIG-IP devices.
- If you use a secondary high availability BIG-IQ system, enable traffic between the BIG-IQ systems. This traffic keeps the state information synchronized on your BIG-IQ systems.
- Provide access the BIG-IQ user interface. You can also use it to access the BIG-IQ system using SSH if you need to run manual commands.
This figure illustrates the network topology required for an advanced management and configuration deployment.
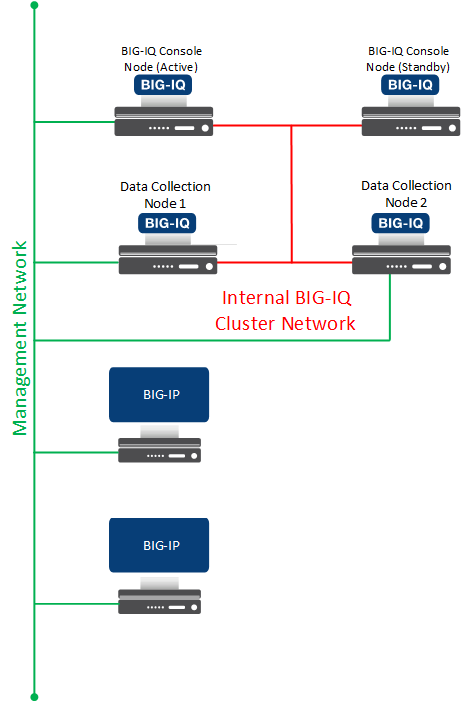
Centralized management and enhanced monitoring network topology
Use the table to record the IP addresses for the devices in the BIG-IQ deployment.
| Device Type | Management IP addresses | Internal Network IP addresses |
|---|---|---|
| Primary BIG-IQ system | ||
| Secondary BIG-IQ system | ||
| Data Collection Device management IP addresses | ||
| BIG-IP devices | ||
| Remote storage device |
Network environment for large-scale, distributed management and configuration
To deploy this configuration, you need BIG-IQ® systems, Data Collection Devices, and an external storage device. This configuration needs an external network, a management network, an internal network, and an optional external storage device for backing up alert, event, and statistical data.
The external network routes traffic between the BIG-IQ Centralized Management cluster and the BIG-IP® devices.
Traffic on the management network is used to do the following:
- Provide communication between the BIG-IQ system and DCD nodes.
- Enable bidirectional traffic between the BIG-IQ systems and the BIG-IP devices.
- If you use a secondary high availability BIG-IQ system, enable traffic between the BIG-IQ systems. This traffic keeps the state information synchronized on your BIG-IQ systems.
- Provide access the BIG-IQ user interface. You can also use it to access the BIG-IQ system using SSH if you need to run manual commands.
This figure illustrates the network topology required for this deployment.
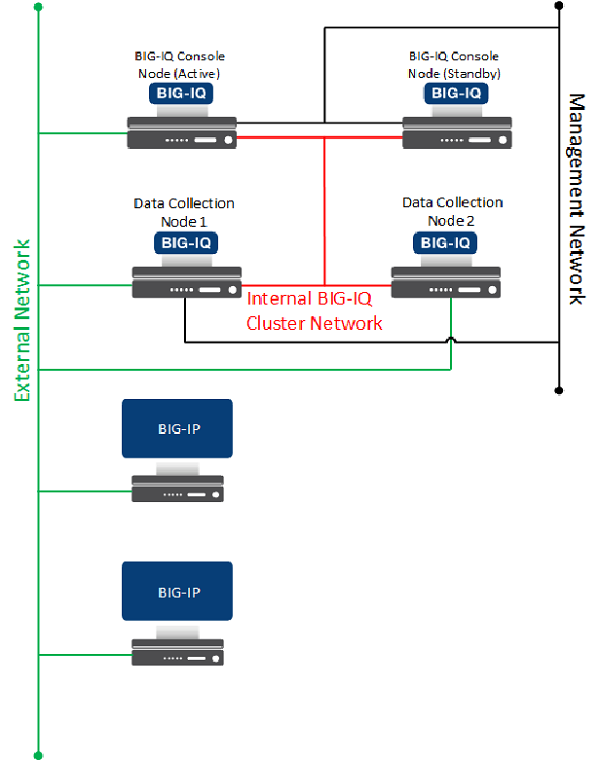
Centralized management, enhanced monitoring, and improved performance network topology
Use the table to record the IP addresses for the devices in the BIG-IQ deployment.
| Device Type | Management IP addresses | Internal Network IP addresses | External Network IP addresses |
|---|---|---|---|
| Primary BIG-IQ system | |||
| Secondary BIG-IQ system | |||
| Data Collection Device management IP addresses | |||
| BIG-IP devices | |||
| Remote storage device |
Open ports required for data collection device cluster deployment
The BIG-IQ® system must have bidirectional communication with the devices in your network to successfully manage them. The ports described in the table must be open to allow for this required two-way communication. You might have to contact a firewall or network administrator to verify that these ports are open, or to have them opened if they are not.
| Source IP Address | Destination IP Address | Destination Port | Protocol | Is port Configurable? | Is the Protocol Configurable? | Purpose | Connection Origination |
|---|---|---|---|---|---|---|---|
| Management IP address or external self IP address of the BIG-IQ console. *See table note 1. |
Management IP address or self IP address of the BIG-IP device. *See table note 1. |
443 (SSL) 22 (SSH) *See table note 4. |
TCP | No | No | Device-level discovery, device configuration changes, and device operations (backup, licensing, and so on), health checking, and some statistics (For example, Access or ADC object status). | From BIG-IQ console to BIG-IP devices. |
| Management IP address or external self IP address of the BIG-IQ data collection
device. *See table notes 1 and 2. |
Management IP address or self IP address of the BIG-IP device. *See table note 1. |
443 (SSL) | TCP | No | No | Statistics collection for Local Traffic, Device, and DNS objects. | From BIG-IQ data collection devices to BIG-IP devices. |
| Management IP address or internal self IP address of the BIG-IQ console. *See table note 1. |
Management IP address or internal self IP address of the BIG-IQ console. *See table note 1. |
443 (SSL) | TCP | No | No | BIG-IQ cluster synchronization and cluster maintenance. |
From the active BIG-IQ console to the standby BIG-IQ console. From the BIG-IQ standby console to the BIG-IQ active console. |
| Management IP address or internal self IP address of the active BIG-IQ console.
*See table note 1. |
Management IP address or internal self IP address of the standby BIG-IQ console.
*See table note 1. |
27017 | TCP | No | No | BIG-IQ high availability cluster data replication. |
From the active BIG-IQ console to the standby BIG-IQ console. From the BIG-IQ standby console to the BIG-IQ active console. |
| Management IP address or internal self IP address of the BIG-IQ console and the
data collection device. *See table notes 1 and 2. |
Management IP address or internal self IP address of the BIG-IQ console and the
data collection device. *See table notes 1 and 3. |
9300 | TCP | Yes | No | Internal node-to-node communication to maintain data consistency and replication across clusters when data collection nodes are used. | Full Mesh That is, all BIG-IQ console and data collection devices can originate a connection for this purpose. |
| Management IP address or self IP address of the BIG-IP device. *See table note 1. |
Management IP address or self IP address of the BIG-IQ data collection device.
*See table notes 1 and 3. |
8514 | TCP | No | No | Logging profile communication for Web Application Security. This traffic uses the syslog protocol documented in RFC 5424. | From BIG-IP devices to BIG-IQ data collection devices. When you have multiple data collection devices, you need to make sure data can pass to all devices in the cluster. |
| Management IP address or self IP address of the BIG-IP device. *See table note 1. |
Management IP address or self IP address of the BIG-IQ data collection device.
*See table notes 1 and 3. |
8008 | TCP | No | No | Logging profile communication for Fraud Protection Service, this traffic uses the syslog protocol documented in RFC 5424. | From BIG-IP devices to BIG-IQ data collection devices. When you have multiple data collection devices, you need to make sure data can pass to all devices in the cluster. |
| Management IP address or self IP address of the BIG-IP device. | Management IP address or self IP address of the BIG-IQ data collection device.
*See table notes 1 and 3. |
9997 | TCP | No | No | For access to events; this traffic uses the syslog protocol documented in RFC 5424. | From BIG-IP devices to BIG-IQ data collection devices. When you have multiple data collection devices, you need to make sure data can pass to all devices in the cluster. |
| Client IP address | BIG-IQ Management IP address or self IP address for all BIG-IQ instances in the cluster. |
443 (SSL) 22 (SSH) |
TCP | No | No | For management access to BIG-IQ GUI or API (port 443) or shell access to BIG-IQ (port 22) | From the client workstation to the BIG-IQ device. |
Passwords required for data collection device cluster deployment
To install and configure a data collection device cluster, you use the default passwords for all of the devices in your cluster. If (as recommended) you intend to schedule regular snapshots of your logging data, you need root access credentials for the machine on which you plan to store these snapshots.
| User Name | Default Password | Access Rights/Role |
|---|---|---|
| admin | admin | This user type can access all aspects of the BIG-IQ® system from the system's user interface. |
| root | default | This user has access to all aspects of the BIG-IQ system from the system's console command line. |
Licenses required for data collection device cluster deployment
To install and configure a data collection device cluster, you need a license for each device.
Data collection device sizing guidelines
This material is being replaced with a new guide scheduled for inclusion in the next release.
Deploying a Data Collection Device
How do I deploy a data collection device cluster?
To manage the data generated by BIG-IP® devices on BIG-IQ® Centralized Management, you deploy a network of devices called a data collection device (DCD) cluster, and then configure that cluster to meet your business needs.
- Prepare your network environment
- Install the DCDs
- Discover and activate the DCDs
- Define an external location to store snapshots
- Enable data collection for the DCD cluster (or configure a BIG-IP system to send alerts or events to the cluster)
- Configure the BIG-IQ console that manages the DCD cluster for HA, if needed.
License basic setup for a data collection device?
The BIG-IQ® data collection device runs as a virtual machine in supported hypervisors, or on the BIG-IQ 7000 series platform. You license the data collection device using the base registration key you purchased. The base registration key is a character string that the F5 license server uses to provide access to data collection device features.
You license data collection device in one of the following ways:
- If the system has access to the internet, you can have the data collection device contact the F5 license server and automatically activate the license.
- If the system is not connected to the internet, you can manually retrieve the activation key from a system that is connected to the internet, and transfer it to the data collection device.
- If your data collection device is in a closed-circuit network (CCN) that does not allow you to export any encrypted information, you must open a case with F5 support.
When you license the data collection device, you:
- Specify a host name for the system.
- Assign a management port IP address.
- Specify the IP address of your DNS server and the name of the DNS search domain.
- Specify the IP address of your Network Time Protocol (NTP) servers and select a time zone.
- Change the administrator’s default admin and root passwords.
Automatically license BIG-IQ and perform initial setup
Manually license BIG-IQ and perform initial setup
Discover and activate a data collection device
Modifying alert log indices for Access
Modifying alert log indices for Web Application Security
Modifying event log indices for FPS
Configure secure communications for data collection device
- Use SSH to log in to the data collection device.
- Replace the content of the /etc/httpd/conf/ssl.crt/ directory on the data collection device with your signed SSL certificate.
- Replace the content of the /etc/httpd/conf/ssl.key/ directory on the data collection device with your signed SSL key.
- To apply these changes to the data collection device, type: bigstart restart webd and then press Enter.
- Log out of the data collection device.
Add a proxy for secure communication
Before you can perform this task, you must be logged in as Admin, and you must have configured a proxy server that your data collection device cluster can access.
Define external storage snapshots location
- Storage-machine-IP-address
- Storage-file-path
- User name, password, and (optionally) the domain for the user account configured on the external storage device
- Read/Write permissions for the storage file path
You need snapshots to perform software upgrades and to restore your old data.
When you create DCD snapshots, they need to be stored on a machine other than the DCD. You define the location for the snapshot using the BIG-IQ® Centralized Management device.
Define snapshot schedules
Overview of configuring the data collection device to BIG-IP device connection
The workflow to configure data to route from the BIG-IP® devices to your data collection device (DCD) cluster depends on the type of data you want to collect.
- To collect statistics data, refer to Discover and activate a data collection device.
- To collect Access Policy Manager® data, refer to Configuring remote logging for Access Policy Manager.
- To collect Fraud Protection Services data, refer to Configuring BIG-IP FPS devices to route alerts to a data collection device.
- To collect Web Application Security
data, refer to:
- Configuring the BIG-IP logging profile
- Virtual servers that remote logging uses to route event logs
- Assigning the logging profile to a virtual server
Configure remote logging for Access Policy Manager
Configuring BIG-IP FPS devices to route alerts to a data collection device
The BIG-IP® device that generates Fraud Protection Service alerts must be configured to send its alerts to the data collection device (DCD). This process is documented in a separate guide. The guide F5® Fraud Protection Service: Configuration, Version 13.0 provides complete setup instructions for using FPS on a BIG-IP® system. Complete the standard setup as documented in the guide, except when you configure the alert server pool, add your DCDs to an alerts pool using their internal self IP addresses.
- Distribute traffic between the nodes.
- Ensure that, if a DCD goes offline, the BIG-IP device must still be able send traffic to the available DCDs without dropping alerts.
The default port to specify is 8008, but you can use a different port if your DCD is configured for it. To ensure that alerts are received even if one DCD goes down, specify at least one alternative DCD.
Configure the BIG-IP logging profile
Virtual servers that remote logging uses to route alert or event logs
You can either create a new virtual server on the BIG-IP® device that creates the alert or event, or you can use a virtual server that already exists on that device.





