Manual Chapter :
Configuring Azure Conditional Access
Applies To:
Show Versions
BIG-IP APM
- 21.1.0 , 21.0.0, 17.5.1, 17.5.0, 17.1.3, 17.1.2, 17.1.1, 17.1.0, 17.0.0, 16.1.6, 16.1.5, 16.1.4, 16.1.3, 16.1.2, 16.1.1, 16.1.0, 16.0.1, 16.0.0, 15.1.9, 15.1.8, 15.1.7, 15.1.6, 15.1.5, 15.1.4, 15.1.3, 15.1.2, 15.1.1, 15.1.0, 15.0.1, 15.0.0, 14.1.5, 14.1.4, 14.1.3, 14.1.2, 14.1.0, 14.0.1, 14.0.0, 13.1.5, 13.1.4, 13.1.3, 13.1.1, 13.1.0, 12.1.4, 12.1.3
Configuring Azure Conditional Access
Configuring BIG-IP client certificate inspection
To configure BIG-IP client certificate inspection:
- Sign in to the Azure portal.
- In Azure active directory, click .
- Create a new certificate with:
- Validity:One year
- Primary:Yes
- Import the certificate onto the BIG-IP system.
- Navigate to . ClickImportto import certificate.
- Navigate to .
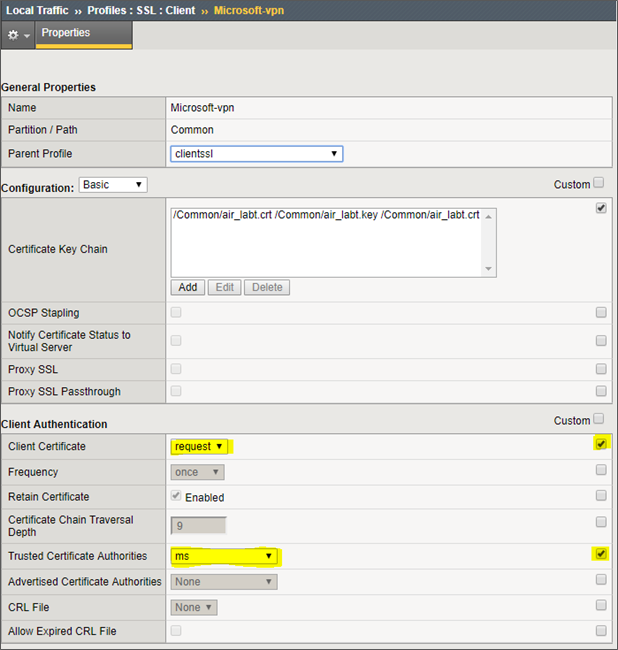
- Choose the certificate forTrusted Certificate Authorities, and enablerequestforClient Certificate.Client certificate enabled in client SSL profile
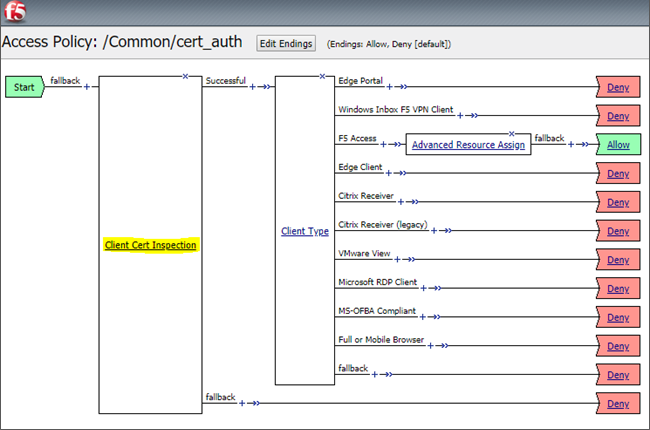
- Add Client Certificate Inspection to your current VPN APM Access Policy.Example of a client certificate inspection in access policy
Configuring Azure AD conditional access policy
To configure your conditional access policy:
- Sign in to the Azure portal.
- In Azure active directory, in theManagesection, click .
- In the example here, we want make sure that all VPN connections from "VPN Users" group are controlled. Create a new policy with the following selections:
- Name:TypeVPN CA Policy
- Users and Groups:VPN Users
- Cloud Apps:VPN Server
- Conditions:No conditions
- Grant:SelectGrant accessand then selectRequire device to be marked as compliant. You can also useRequire multi-factor authenticationorRequire domain joined (Hybrid Azure AD)options.
- Session:No session
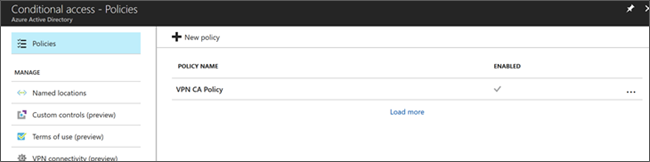
Conditional access policy settings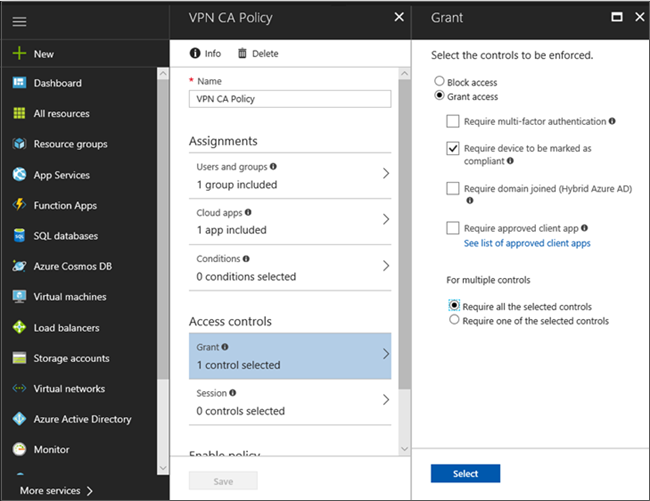
- Enable the new policy in .Policy enabled in conditional access
Marking the device as compliant in Azure AD
You can deploy compliance policy to users in user groups or devices in device groups.
When a compliance policy is deployed to a user, all of the user's devices are
checked for compliance. If a device doesn't have a compliance policy assigned, then
this device is considered not compliant. To become a managed device, a device must
be a
device that has been marked as compliant
. To mark the
device as compliant in Azure AD:- Sign in to the Azure portal.
- Click .
- Create a new compliance policy without configuring any settings.
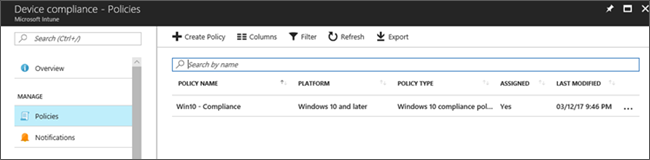
- Assign this policy to VPN users group.Example of a device compliance policy
Adding conditional access to VPN profile
To add a conditional access to VPN profile using Intune:
- Sign in to the Azure portal.
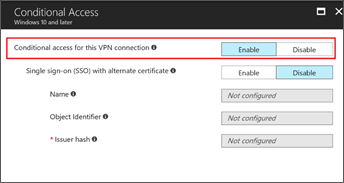
- Create a new VPN profile for Windows 10. Follow the steps similar to creating a base VPN profile. Enable theEnable conditional access for this VPN connectionto ensure that devices that connect to the VPN are tested for conditional access compliance before connecting.Conditional access enabled for VPN connection
Configuring custom XML in profile using Intune
F5 Access for Windows Desktop supports the following three authentication flows:
- Username
- Certificate only (no prompt for credentials)
- Username & certificate
These authentication flows can be configured through custom XML commands. You can enter
Custom XML commands that configure the VPN connection in F5 Access profile using Intune.
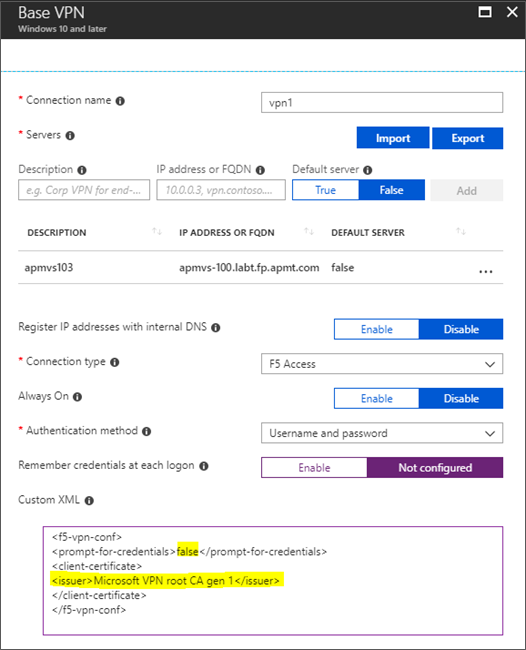
The following example shows how a certificate is configured using custom XML.
<f5-vpn-conf> <prompt-for-credentials>false</prompt-for-credentials> <client-certificate> <issuer>Microsoft VPN root CA gen 1</issuer> </client-certificate> </f5-vpn-conf>
Example of a custom XML command
Refer to Configuration Notes: F5 Access for Microsoft Windows 10 and
Windows 10 Mobile for more information.
Accessing certificates
To access pre-defined certificates:
- Follow the below steps to connect to VPN:
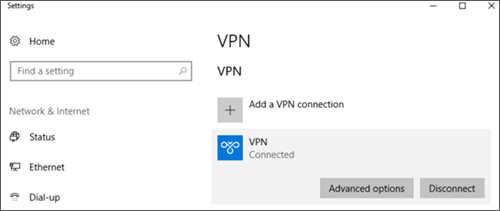
- On the Windows 10 device, navigate to .
- Wait for the new VPN to be installed. Connect to VPN.VPN connected screen
- On successful VPN connection, run theCertmgr.msccommand in cmd prompt or PowerShell window.This will launch the Current User certificate MSC.
- Navigate to . You should see a newly provisioned certificate issued by "Microsoft VPN root CA gen 1".Current User certificate MSC
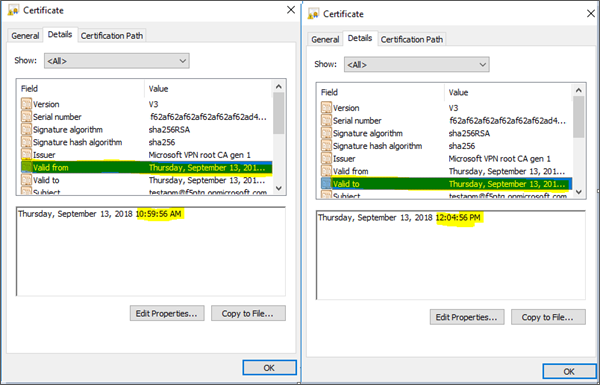
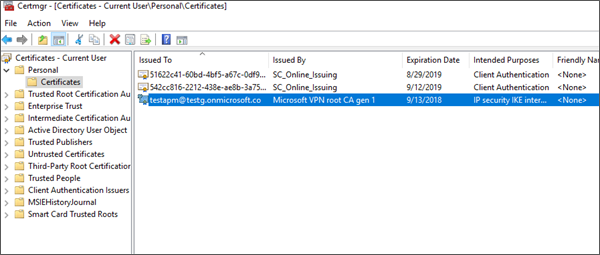 Certificate's expiry date will be 60 minutes from when it was last requested.Certificate's expiry date
Certificate's expiry date will be 60 minutes from when it was last requested.Certificate's expiry date