Manual Chapter :
Modify and Manage Layer 7 Security Objects
Applies To:
Show Versions
BIG-IQ Centralized Management
- 7.0.0
Modify and Manage Layer 7 Security Objects
Modifying object Layer 7 security to improve application
protection
On BIG-IP devices, virtual servers have Layer 7 (L7) security objects
(such as DoS profiles, logging profiles, or Web Application Security policies) that detect
and mitigate bad traffic to an application. After configuring your virtual servers, you can
manage the application security settings using BIG-IQ Centralized Management. The L7
Security Dashboard () lists all deployed applications and virtual servers that are managed by
your system. You can use this list to manage the L7 protection and logging needs of all
your objects. Object management capabilities include:
- Edit one or more application L7 protection.
- Edit one or more virtual server L7 protection
- Deploy bulk changes to multiple virtual servers
Adjust Layer 7 protection for applications
To view object information you must have the
following:
- A Data Collection Device (DCD) configured to your BIG-IQ system.
- Managed BIG-IP devices have ASM provisioned for managing security policies.
- The BIG-IQ system has Shared Security (SSM) discovered to manage virtual servers' DoS and logging profiles.
- Managed BIG-IP devices have AVR provisioned (recommended).
You identify the Layer 7 security configuration of
your managed applications so you can modify the security objects that improve security.
To deploy changes on both applications and virtual servers, see
Adjust Layer 7
security for virtual servers
.- Go to .This displays all monitored objects.
- Select one or more applications that you want to edit.If you are attaching a DoS profile, it is recommended to configure only one DoS profile per application. Ensure that any existing DoS profile for the selected applications are removed.
- To attach a security object to your selected application:
- ClickAttachand select a security resource type from the list.
- From theChoose resource to attachwindow select a security object resource.
- ClickContinue.
- To remove a security object from your selected application:
- ClickDetachand select the security object type from the list.
- In theDetach Confirmationpopup screen, clickContinueto confirm the security object's removal.
Changes to applications will render an immediate update
for the deployment process, and changes are immediately reflected in the L7 Security
Dashboard. The time required to complete the deployment process varies based on the
number of applications selected.
To monitor overall health and status of all your applications, go to . For more information about managing your applications, refer to
the topics in BIG-IQ
Centralized Management: Monitoring and Managing Application Services
on support.f5.com
.Adjust Layer 7 security for virtual servers
To view object information, you must have the
following:
- A Data Collection Device (DCD) configured to your BIG-IQ system.
- Managed BIG-IP devices have ASM provisioned for managing security policies.
- The BIG-IQ system has Shared Security (SSM) discovered to manage virtual servers' DoS and logging profiles.
- Managed BIG-IP devices have AVR provisioned (recommended).
You identify L7 security configuration of your
managed virtual servers so you can modify the security configuration. This applies to
virtual servers connected to one or more host devices. Any changes to multiple virtual
servers can be deployed individually, or in bulk, depending on the complexity of your
system setup. You can use this process to apply bulk object changes to applications and
virtual servers.
Changes to your virtual servers'
configuration can be deployed immediately or manually. The time required to complete
the deployment process varies depending on the number of virtual servers and the
complexity of their configuration. It is not recommended to deploy immediate changes
for more than 20 virtual servers at single time.
- Go to .This displays all monitored objects.
- Select one or more virtual servers that you want to edit.For immediate deployment of changes, limit the selection to 20 virtual servers.
- To add or remove a security object to your selected virtual server:
- ClickAttach(to add), orDetach(to remove), and select a security resource type from the list.
- From the bottom of theChoose resource to attachwindow, select a security resourceThe list of resources is specific to your object selection. If you have selected multiple objects, only resources shared by your selection are available.
- If you would like to deploy your changes immediately, select the check box forDeploy Virtual Servers.Deployment times vary depending on the selected virtual server. If you do not select this option, you can continue to adjust your virtual server's settings and conduct a bulk deployment for selected objects in the L7 Security Dashboard.
- ClickContinue.
Changes to virtual servers immediately deploy, if you
selected
Deploy Virtual Server
. If you did not select this
option, you can continue to adjust the L7 protection properties of your virtual server,
and conduct a bulk deployment later.To monitor the overall status of your virtual
server, go to and click the
Protected Objects
area at the top
right of the screen. This will provide information about the health status and current
configuration of your objects.Deploying virtual server L7 protection changes
If you have made changes to the L7 security or
logging settings of a virtual server, these changes might not be deployed, unless
otherwise prompted. You can deploy these changes directly from the L7 security
dashboard.
The maximum recommended limit for deployment is 20 virtual
servers.
- Go to .This displays all monitored objects.
- Select the check box next to the name of the virtual server(s) with changes that have yet to be deployed.
- ClickDeploy Now.
The changes made to your virtual servers are deployed
immediately. The time to complete the deployment process varies depending on the
complexity of your virtual servers' configuration, and the number of virtual servers
selected.
Object protection modes for Layer 7 security
The L7 Security Dashboard ( ) displays objects with different protection modes.
Protected objects
consist of the applications or virtual severs that have a Web
Application Security policy or DoS profile. Object protection modes
The PROTECTION MODE area on this screen displays the number
of managed objects for each protection mode.

Blocking
A virtual server has a Blocking security mode if it has at least one
of the following security configurations. Likewise, an application has a Blocking
security mode if at least one of its assigned virtual servers has a Blocking protection
mode.
- Web Application Security Policy
- The policy's Enforcement Mode is set toBlocking.
- DoS Profile
- The operation mode for TPS-based Detection is set toBlocking.
- and/or
- The operation mode for Behavioral & Stress-based Detection is set toBlocking.
Monitoring
A virtual server has a Monitoring security mode if it has at least
one of the following security configurations, and has no Blocking security
configurations. Likewise, an application has a Monitoring security mode if at least one
of its assigned virtual servers has a has a Monitoring protection mode and none of its
virtual servers has a Blocking protection mode.
- Web Application Security Policy
- The policy's Enforcement Mode is set toTransparent.
- DoS Profile
- The operation mode for TPS-based Detection is set to Blocking .
- and/or
- The operation mode for Behavioral & Stress-based Detection is set toTransparent.
Not Protected
A virtual server is not protected if it does not have a Monitoring or
Blocking configuration. An application is not protected if all of its assigned virtual
servers are not protected.
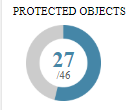
Protected objects with Layer 7 Security
The Layer 7 Security screen () displays the applications and virtual servers monitored by BIG-IQ Centralized
Management.
Protected objects
consist of the applications or
virtual severs that have a Web Application Security policy or DoS profile with an enabled
protection status. The PROTECTED OBJECTS area on this screen displays the number of protected
objects, out of the total objects. The following describes the object count for this screen,
regardless of protection status:The number of managed protected objects, out of all the objects
managed by your system.
- Virtual Server
- A stand-alone virtual server counts as a managed object (protected or unprotected) when it is not assigned to an application. The virtual server must have at least one HTTP profile. Once it is assigned to an application, the virtual server is no longer included in the total object count.
- Application
- Each application counts as an object (protected or unprotected). The application includes all its assigned virtual servers.
L7 Security Alerts
Security alerts in the TRENDS AND IMPACTS area of the L7
Security Dashboard () notify you of the number of objects reporting Web Application Security policy
(Web Exploits) or DoS profile (L7 DDoS Attacks) events over the past day (trend charts report
the past week). These alerts indicate that a protected object (application or virtual server)
recently experienced an increased rate in performance issues. To view data the corresponds with
these traffic events go to To view the status of your deployed applications, go to .
Alert | Description | Indication | Default Thresholds | Action (if applicable) |
|---|---|---|---|---|
BAD TRAFFIC
TRENDS | The number of objects with a significant increase in
traffic with any violation rating. | Increase in transactions with any violation
rating. | Web Exploits: The average number of transactions with a
violation rating exceeded 10% in the past 24 hours and increased by a ratio of 0.1%
out of all traffic over the past week. L7 DDoS Attacks: The average volume of active, simultaneous
attacks increased in the past 24 hours. | Investigate transactions and fine tune your security
policy/profile for new threats. |
POTENTIALLY
HARMFUL ATTACKS | The number of objects with a transparent protection mode
(Monitoring), that have an increase in bad traffic. | Increase in transactions with high violation rating. | Web Exploits: The rate of transactions with violation rating of
4 or 5 exceeded 0.1% in the past 24 hours. L7 DDoS Attacks: The volume of simultaneous active attacks
increased in the past 24 hours. | Change security policy or profile to Blocking
mode. |
FALSE
POSITIVE ATTACKS | The number of objects with a blocking protection mode that
have an increase in blocked traffic with a low violation rating. | Increase in blocked transactions. | Web Exploits: The rate of blocked transactions with a violation
rating of 1 or 2 exceeded 0.01% over the past 24 hours. | Investigate blocked transactions and fine-tune your Web
Application Security policy to allow valid transactions. |
BLOCKED
ATTACKS | The number of objects with a blocking protection mode that
blocked any bad traffic over the past 24 hours. | N/A | N/A | N/A |





