Manual Chapter :
Configuring IPsec in Interface Mode between Two BIG-IP Systems
Applies To:
Show Versions
BIG-IP AAM
- 15.1.9, 15.1.8, 15.1.7, 15.1.6, 15.1.5, 15.1.4, 15.1.3, 15.1.2, 15.1.1, 15.1.0, 15.0.1, 15.0.0, 14.1.5, 14.1.4, 14.1.3, 14.1.2, 14.1.0
BIG-IP APM
- 21.1.0 , 17.0.0, 16.1.6, 16.1.5, 16.1.4, 16.1.3, 16.1.2, 16.1.1, 16.1.0, 16.0.1, 16.0.0, 15.1.9, 15.1.8, 15.1.7, 15.1.6, 15.1.5, 15.1.4, 15.1.3, 15.1.2, 15.1.1, 15.1.0, 15.0.1, 15.0.0, 14.1.5, 14.1.4, 14.1.3, 14.1.2, 14.1.0
BIG-IP Link Controller
- 21.1.0 , 17.0.0, 16.1.6, 16.1.5, 16.1.4, 16.1.3, 16.1.2, 16.1.1, 16.1.0, 16.0.1, 16.0.0, 15.1.9, 15.1.8, 15.1.7, 15.1.6, 15.1.5, 15.1.4, 15.1.3, 15.1.2, 15.1.1, 15.1.0, 15.0.1, 15.0.0, 14.1.5, 14.1.4, 14.1.3, 14.1.2, 14.1.0
BIG-IP LTM
- 21.1.0 , 17.0.0, 16.1.6, 16.1.5, 16.1.4, 16.1.3, 16.1.2, 16.1.1, 16.1.0, 16.0.1, 16.0.0, 15.1.9, 15.1.8, 15.1.7, 15.1.6, 15.1.5, 15.1.4, 15.1.3, 15.1.2, 15.1.1, 15.1.0, 15.0.1, 15.0.0, 14.1.5, 14.1.4, 14.1.3, 14.1.2, 14.1.0
BIG-IP AFM
- 21.1.0 , 17.0.0, 16.1.6, 16.1.5, 16.1.4, 16.1.3, 16.1.2, 16.1.1, 16.1.0, 16.0.1, 16.0.0, 15.1.9, 15.1.8, 15.1.7, 15.1.6, 15.1.5, 15.1.4, 15.1.3, 15.1.2, 15.1.1, 15.1.0, 15.0.1, 15.0.0, 14.1.5, 14.1.4, 14.1.3, 14.1.2, 14.1.0
BIG-IP ASM
- 21.1.0 , 17.0.0, 16.1.6, 16.1.5, 16.1.4, 16.1.3, 16.1.2, 16.1.1, 16.1.0, 16.0.1, 16.0.0, 15.1.9, 15.1.8, 15.1.7, 15.1.6, 15.1.5, 15.1.4, 15.1.3, 15.1.2, 15.1.1, 15.1.0, 15.0.1, 15.0.0, 14.1.5, 14.1.4, 14.1.3, 14.1.2, 14.1.0
Configuring IPsec in Interface Mode between Two BIG-IP Systems
Overview: Configuring IPsec in Interface mode between two BIG-IP systems
You can configure an IPsec tunnel when you want to secure traffic that traverses a wide area
network (WAN), from one BIG-IP ®system to another. By following this
procedure, you can create an IPsec tunnel interface that can be used as any other BIG-IP VLAN.
When you configure an IPsec tunnel interface, the IKE tunnel mode security associations occur
automatically as part of the tunnel negotiation. For the IPsec tunnel interface, only the IPsec
Encapsulating Security Protocol (ESP) is supported for the tunnel interface, and IPComp is not
available.
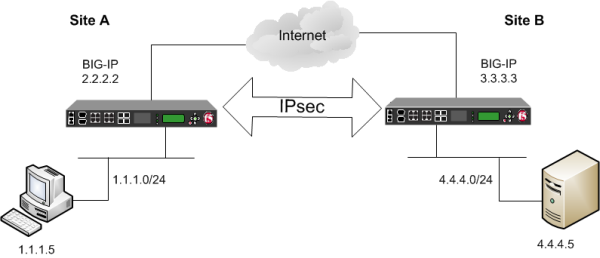
Example of an IPsec deployment
Task summary for
configuring IPSEC interface from BIG-IP to BIG-IP
Before you begin configuring IPsec, verify that these modules, system objects, and
connectivity exist on the BIG-IP® systems in both the local and
remote locations:
- BIG-IP Local Traffic Manager
- This module directs traffic securely and efficiently to the appropriate destination on a network.
- Self IP address
- Each BIG-IP system must have at least one self IP address, to be used in specifying the ends of the IPsec tunnel.
- The default VLANs
- These VLANs are namedexternalandinternal.
- BIG-IP connectivity
- Verify the connectivity between the client or server and its BIG-IP device, and between each BIG-IP device and its gateway. For example, you can usepingto test this connectivity.
Task list
Creating a forwarding virtual server for IPsec
For IPsec, you create a forwarding
(IP) type of virtual server to intercept IP traffic and direct it over the tunnel. With
a forwarding (IP) virtual server, destination address translation and port translation
are disabled.
- On the Main tab, click .The Virtual Server List screen opens.
- ClickCreate.The New Virtual Server screen opens.
- In theNamefield, type a unique name for the virtual server.
- From theTypelist, selectForwarding (IP).
- In theDestination Address/Maskfield, type a wildcard network address in CIDR format, such as0.0.0.0/0for IPv4 or::/0for IPv6, to accept any traffic.
- From theService Portlist, select*All Ports.
- From theProtocollist, select*All Protocols.
- From theVLAN and Tunnel Trafficlist, retain the default selection,All VLANs and Tunnels.
- ClickFinished.
Creating a custom IPsec policy for Interface mode
You can create a custom IPsec policy to specify the Interface mode, which allows you
to use the IPsec tunnel as a network interface object.
You must perform this task on the BIG-IP
systems at both sides of the tunnel.
- On the Main tab, click .
- Click theCreatebutton.The New Policy screen opens.
- In theNamefield, type a unique name for the policy.
- For theIPsec Protocolsetting, retain the default selection,ESP.
- From theModelist, selectIPsec Interface.
- ClickFinished.The screen refreshes and displays the new IPsec policy in the list.
- Repeat this task on the BIG-IP system in the remote location.
Creating an IPsec traffic selector
The traffic selector you create filters traffic based on the IP addresses you
specify and the custom IPsec policy you assign.
You must perform
this task on the BIG-IP systems on both sides of the
WAN.
- On the Main tab, click .
- ClickCreate.The New Traffic Selector screen opens.
- In theNamefield, type a unique name for the traffic selector.
- For theSource IP Addresssetting, specify where the application traffic originates, either:
- ClickHostand type an IP address.
- ClickNetwork, and in theAddressfield, type an IP address.
This table shows sample source IP addresses for BIG-IP A and BIG-IP B.System NameSource IP AddressBIG-IP A1.1.1.0/24BIG-IP B4.4.4.0/24 - For theDestination IP Addresssetting, specify where the application traffic is going, either:
- ClickHostand type an IP address.
- ClickNetwork, and in theAddressfield, type an IP address.
This table shows sample destination IP addresses for BIG-IP A and BIG-IP B.System NameDestination IP AddressBIG-IP A4.4.4.0/24BIG-IP B1.1.1.0/24 - From theIPsec Policy Namelist, select the name of the custom IPsec policy that you created.
- ClickFinished.The screen refreshes and displays the new IPsec traffic selector in the list.
- Repeat this task on the BIG-IP system in the remote location.
Specifying an IPsec tunnel interface traffic selector
You can create an IPsec tunnel profile to filter traffic according to the traffic
selector you specify.
- On the Main tab, click .The New IPsec Profile screen opens.
- In theNamefield, type a unique name for the profile.
- From theParent Profilelist, selectipsec.
- Select theCustomcheck box.
- From theTraffic Selectorlist, select the traffic selector you created.
- ClickFinished.
To use this IPsec profile to filter traffic, you must apply it to an IPsec
tunnel.
Creating an IPsec interface tunnel
You can create an IPsec interface tunnel to apply an IPsec profile you have created
to specify the traffic selector to filter the traffic.
- On the Main tab, click or .The New Tunnel screen opens.
- In theNamefield, type a unique name for the tunnel.
- From theProfilelist, selectIPsec.
- In theLocal Addressfield, type the IP address of the BIG-IP system.
- From theRemote Addresslist, selectSpecify, and type the IP address of the BIG-IP device at the other end of the tunnel.
- ClickFinished.
After you create an IPsec tunnel interface, you can use it just like any other
tunnel interface, such as assigning it a self IP address, associating it with route
domains, and adding it to virtual servers.
Assigning a self IP
address to an IP tunnel endpoint
Ensure that you have created an IP tunnel before starting this task.
Self IP addresses can enable the BIG-IP system,
and other devices on the network, to route application traffic through the associated
tunnel, similar to routing through VLANs and VLAN groups.
If the other
side of the tunnel needs to be reachable, make sure the self IP addresses that you
assign to both sides of the tunnel are in the same subnet.
- On the Main tab, click .
- ClickCreate.The New Self IP screen opens.
- In theNamefield, type a unique name for the self IP address.
- In theIP Addressfield, type the IP address of the tunnel.The system accepts IPv4 and IPv6 addresses.This is not the same as the IP address of the tunnel local endpoint.
- In theNetmaskfield, type the network mask for the specified IP address.For example, you can type255.255.255.0.
- From theVLAN/Tunnellist, select the tunnel with which to associate this self IP address.
- ClickFinished.The screen refreshes, and displays the new self IP address.
Assigning a self IP to a tunnel ensures that the tunnel appears as a resource for
routing traffic.
To direct traffic through the tunnel, add a route
for which you specify the tunnel as the resource.
Assigning a self IP
address to an IP tunnel endpoint
Ensure that you have created an IP tunnel before starting this task.
Self IP addresses can enable the BIG-IP system,
and other devices on the network, to route application traffic through the associated
tunnel, similar to routing through VLANs and VLAN groups.
If the other
side of the tunnel needs to be reachable, make sure the self IP addresses that you
assign to both sides of the tunnel are in the same subnet.
- On the Main tab, click .
- ClickCreate.The New Self IP screen opens.
- In theNamefield, type a unique name for the self IP address.
- In theIP Addressfield, type the IP address of the tunnel.The system accepts IPv4 and IPv6 addresses.This is not the same as the IP address of the tunnel local endpoint.
- In theNetmaskfield, type the network mask for the specified IP address.For example, you can type255.255.255.0.
- From theVLAN/Tunnellist, select the tunnel with which to associate this self IP address.
- ClickFinished.The screen refreshes, and displays the new self IP address.
Assigning a self IP to a tunnel ensures that the tunnel appears as a resource for
routing traffic.
To direct traffic through the tunnel, add a route
for which you specify the tunnel as the resource.





